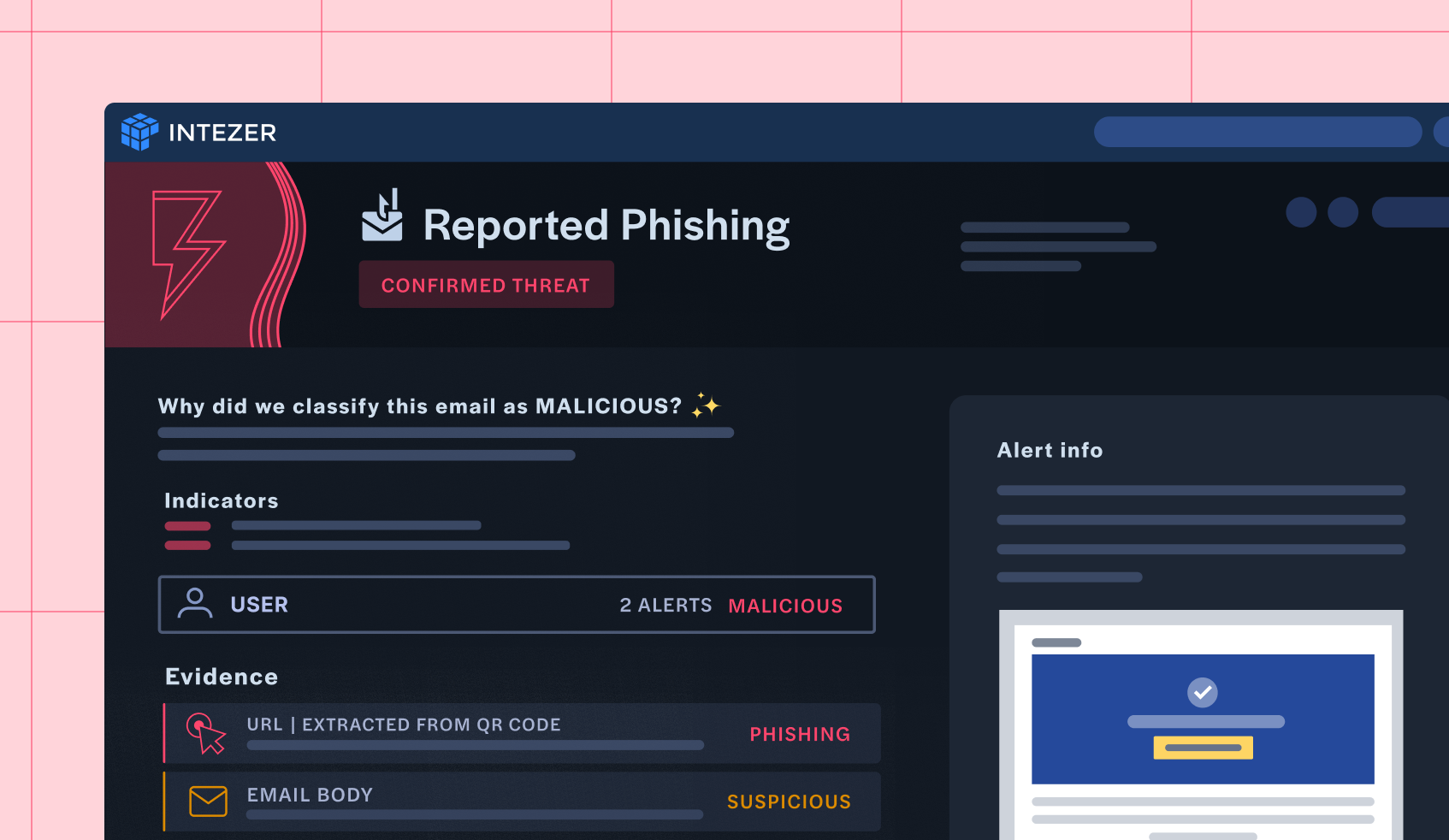
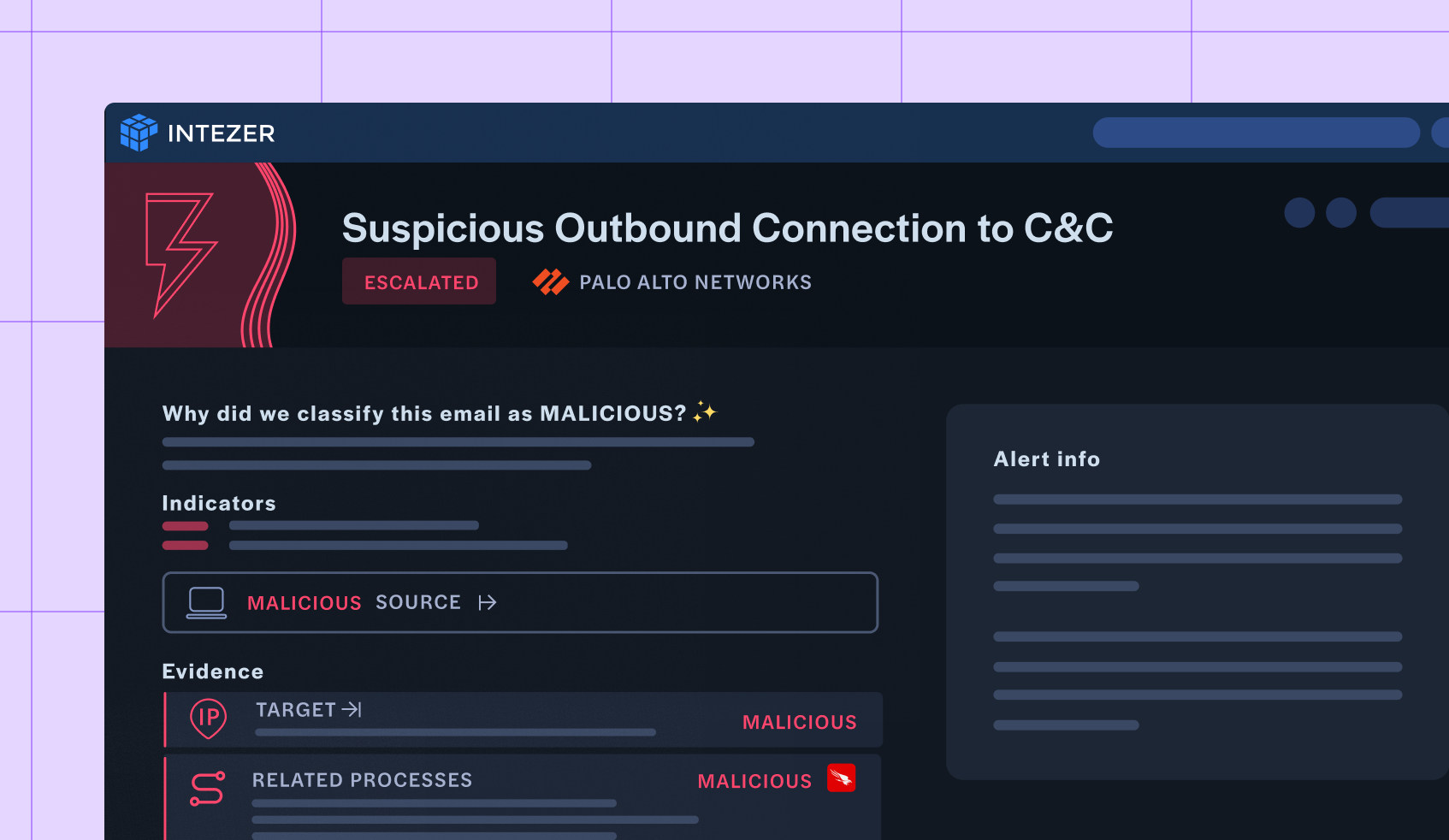
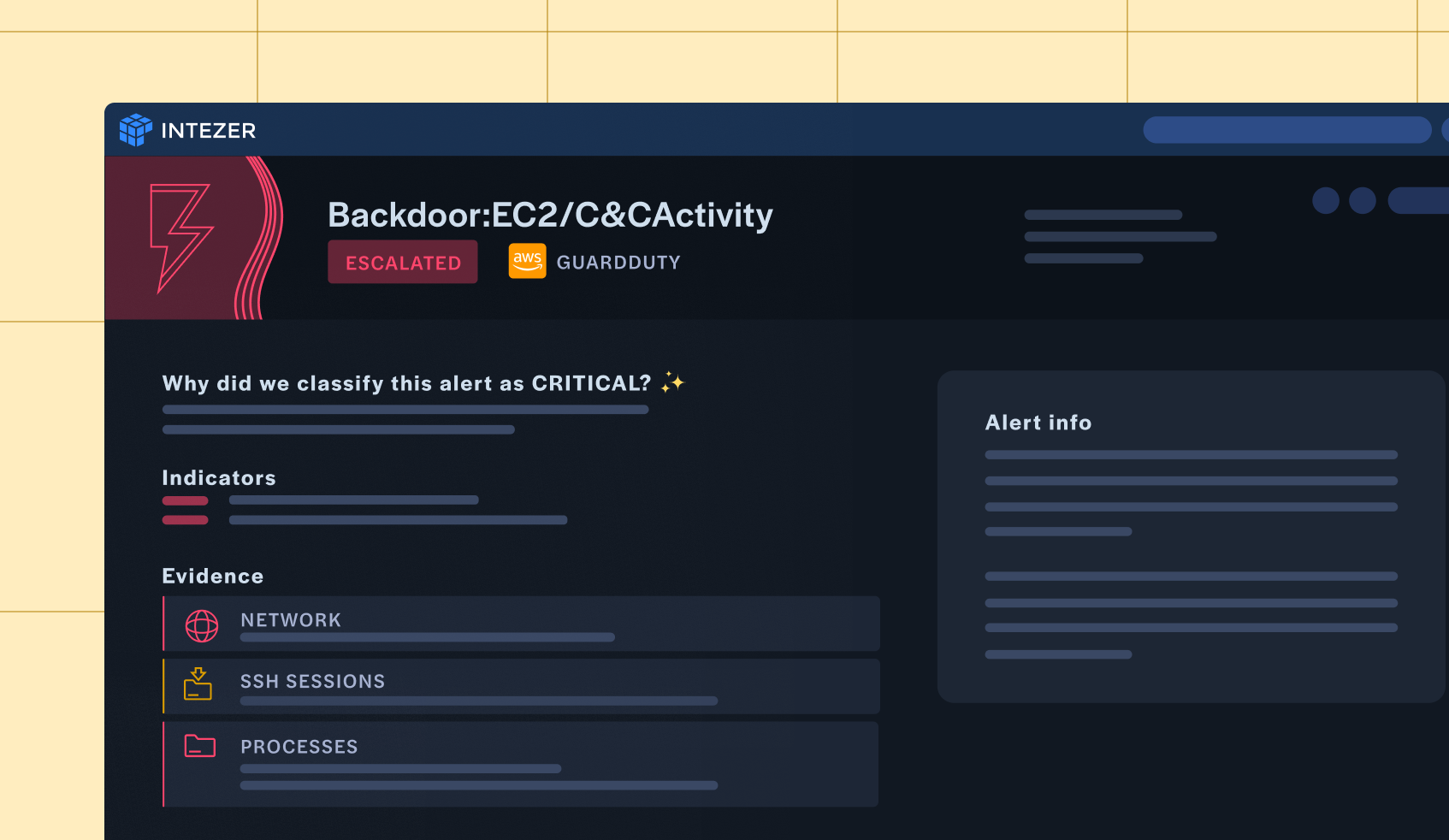
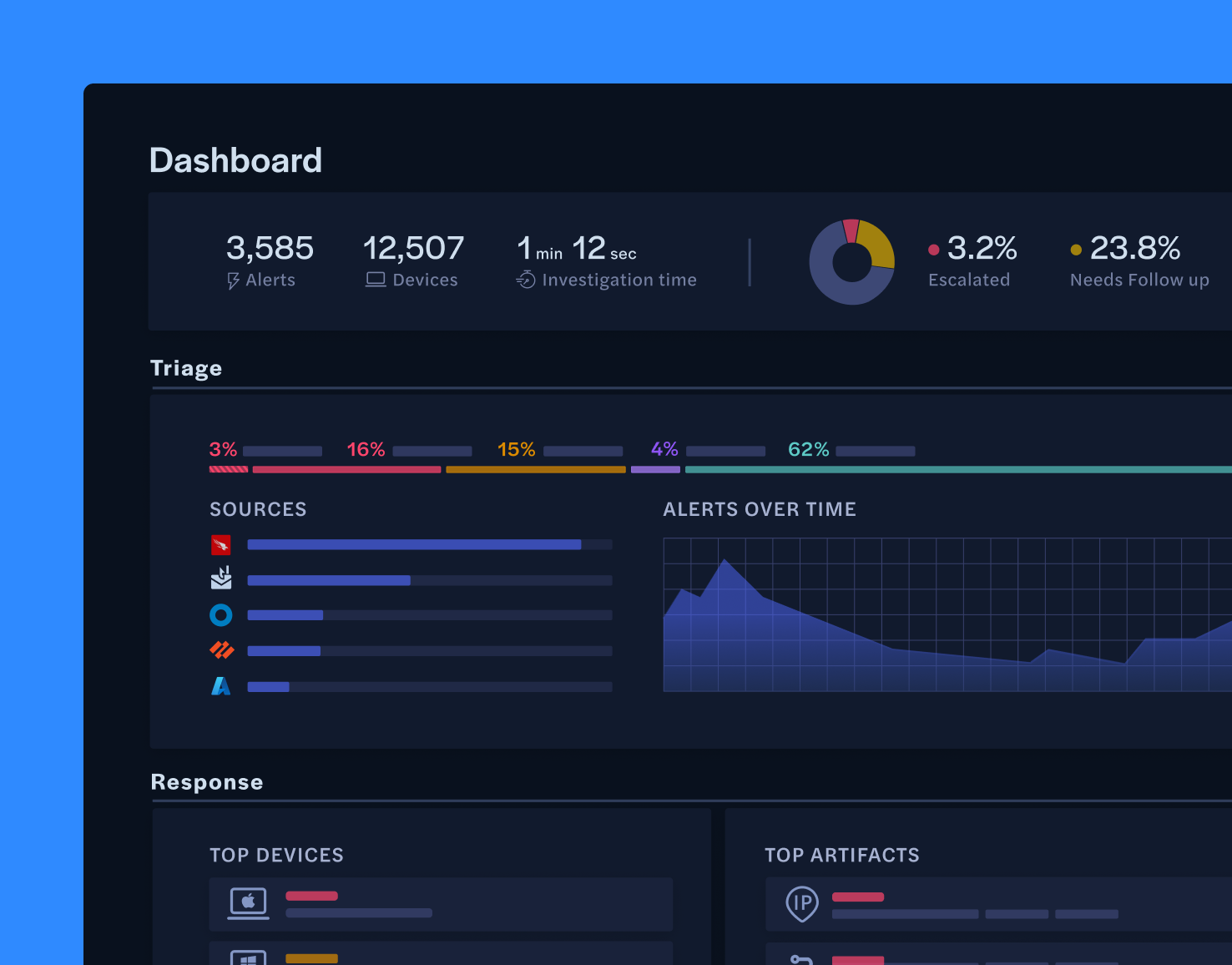
AI alone is not enough for the modern SOC. Intezer’s AI SOC emulates human analysts at scale leveraging the flexibility and intuition of AI with the guardrails of deterministic, forensic tooling. has been developed to be a true partner to your security team.