What Is SOC as a Service (SOCaaS)?
SOC as a Service (SOCaaS) is a managed cybersecurity service that provides organizations with 24/7 threat monitoring, detection, and incident response from an external provider. It offers a cost-effective alternative to building an in-house Security Operations Center (SOC) by outsourcing the necessary technology, expertise, and staff to a third party. This allows companies to focus on core business activities while improving their security posture and maturity.
Key features of SOCaaS solutions include:
- 24/7 threat monitoring: Continuous monitoring of an organization’s security environment for threats.
- Expert staff: Access to skilled security analysts and incident responders.
- Threat detection and response: Identification of and response to security incidents.
- Managed SIEM: Outsourced management of Security Information and Event Management (SIEM) tools.
- AI-driven threat detection: Uses machine learning to identify anomalies and advanced threats that traditional tools may miss.
- Autonomous response actions: Automatically executes predefined actions (e.g., isolate host, block IP) to contain threats in real time.
- Client portal: Access to dashboards and reporting to track security metrics and compliance.
Key Features of a Modern SOC as a Service
24/7 Threat Monitoring
Modern SOCaaS providers offer continuous, around-the-clock monitoring of an organization’s systems, networks, and endpoints. This vigilance helps identify potential threats as soon as they arise, minimizing the window of exposure. Security analysts use real-time alerting and anomaly detection to ensure that suspicious activity is caught promptly, regardless of the hour or time zone.
24/7 monitoring means that experts are always ready to assess, prioritize, and respond to events. Quick identification and evaluation of incidents allow for immediate escalation and containment actions, helping to avert breaches and minimize operational downtime. This approach is fundamental in an environment where attackers do not operate on a 9-to-5 schedule.
Expert Staff
A modern SOCaaS offering is staffed by cybersecurity professionals with skills spanning threat hunting, incident response, forensics, and compliance. These teams consist of analysts, engineers, and advisors who continuously interpret alerts, investigate anomalies, and recommend remediation steps. Their collective experience allows for more accurate detection and faster response to incidents.
With SOCaaS, organizations gain access to a depth of security knowledge that would be costly and difficult to maintain in-house. Providers routinely invest in staff training to keep up with evolving threats and technologies. This expertise is especially valuable during critical events, where speed and accuracy are essential for minimizing damage and guiding recovery efforts.
Managed SIEM
A core feature of some SOCaaS is managed SIEM (security information and event management). The SIEM platform collects and analyzes data from various parts of the client’s IT environment, including network traffic, endpoints, and cloud assets. By correlating events and applying threat intelligence, the managed SIEM identifies unusual behaviors and security incidents that could indicate a breach.
SOCaaS providers handle all aspects of SIEM deployment, tuning, and maintenance. This includes managing log ingestion, rule updates, incident triage, and reporting. Clients benefit from the expertise of the provider’s staff, who ensure the SIEM environment remains effective and up-to-date in detecting emerging threats, without the organization having to deal directly with technical complexity or staffing challenges.
AI-Driven Threat Detection
Artificial intelligence and machine learning have become standard components of many SOCaaS offerings. These technologies enhance threat detection by sifting through large volumes of data to identify patterns, anomalies, or indicators of compromise that may go undetected by traditional rules-based systems. AI-powered analytics can flag subtle or previously unknown attack techniques, improving detection rates.
Machine learning models adapt over time, becoming more effective as they learn from both global threat intelligence and specific client environments. By leveraging AI, SOCaaS providers can process alerts faster, reduce false positives, and increase the overall efficiency of their monitoring teams. This allows human analysts to focus on true positives and complex investigations that require contextual judgment.
Autonomous Response Actions
Modern SOCaaS platforms increasingly incorporate autonomous response capabilities. When a verified threat is detected, automated playbooks can trigger predefined containment or remediation steps, such as isolating compromised endpoints, disabling user accounts, or blocking malicious traffic, within seconds. This swift action helps limit attacker dwell time and potential damage.
Automation also reduces the burden on security analysts, enabling them to focus on strategic investigations. Autonomous responses are typically informed by policy settings and threat intelligence, ensuring consistency and minimizing human error. SOCaaS providers continually refine and customize response workflows to match the specific risk tolerance and operational requirements of each client.
Learn more in our detailed guide to AI SOC automation
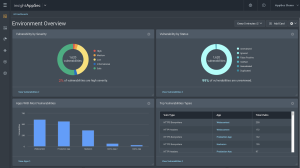
Client Portal
SOCaaS providers typically offer a client portal that centralizes visibility into all security-related operations. Through the portal, clients can review alert histories, incident status, reports, and recommendations in real time. This transparency helps enhance communication between the client and provider, ensuring that all stakeholders are aware of emerging risks and current responses.
A well-designed portal also enables clients to interact directly with security analysts, submit queries, or escalate incidents for further review. Many portals feature dashboards, trend analyses, and compliance-focused reporting to support audits and executive oversight. The client portal is a key interface for both collaboration and ongoing risk management.
Benefits of SOC as a Service
SOC as a Service provides a scalable, cost-effective way for organizations to strengthen their security posture without the burden of building and managing an in-house SOC. Below are key benefits of adopting SOCaaS:
- Cost efficiency: Eliminates the high capital and operational costs of running an internal SOC, including infrastructure, staffing, and ongoing training. Organizations pay a predictable subscription fee based on usage or service level.
- Scalability and flexibility: Allows organizations to scale services up or down based on changing business needs, without the delays or complexities of internal hiring and infrastructure upgrades.
- Advanced technology integration: Leverages tools like SIEM, SOAR, and machine learning, maintained and tuned by the provider, ensuring up-to-date protection against evolving threats.
- Compliance support: Helps organizations meet regulatory requirements by providing detailed logs, reports, and audit trails aligned with standards such as GDPR, HIPAA, and PCI DSS.
- 24/7 monitoring without internal staffing: Delivers continuous security coverage across all time zones, avoiding the need to manage around-the-clock internal teams.
- Reduced Mean Time to Detect (MTTD) and Respond (MTTR): Streamlined processes and dedicated resources improve detection and response times, minimizing potential impact from security incidents.
How SOC as a Service Works
SOCaaS typically operates through a cloud-based delivery model, where the service provider sets up remote monitoring and security management over the client’s IT environment. This typically begins with integration: the provider connects to the client’s systems, such as endpoints, servers, cloud workloads, and network devices, using agents or APIs to ingest logs and telemetry data.
Once integrated, the provider’s platform uses a combination of SIEM, SOAR, and threat intelligence tools to analyze the incoming data. Events are continuously monitored and correlated with known indicators of compromise. Machine learning models help detect anomalies that deviate from normal behavior, flagging potential threats.
Security analysts within the SOCaaS team then investigate alerts, validate incidents, and take appropriate action. In some cases, autonomous response mechanisms are triggered to contain threats instantly. For escalated issues, analysts coordinate with the client via the portal or direct communication channels.
SOCaaS Roles and Responsibilities
A SOC as a Service provider assumes responsibility for managing the security lifecycle—from monitoring to incident response—on behalf of the client. While specific duties can vary by provider and service level, the following roles and responsibilities are commonly included:
- Security monitoring and alerting SOCaaS teams continuously monitor logs, network traffic, and system events for signs of malicious activity. They configure and tune alerting mechanisms to reduce false positives and ensure high-priority threats are detected promptly.
- Threat detection and intelligence Analysts use threat intelligence feeds, behavioral analytics, and correlation rules to identify potential indicators of compromise. Providers maintain updated knowledge of emerging threats to enhance detection capabilities across all client environments.
- Incident triage and investigation Once an alert is triggered, SOCaaS staff assess its severity, validate the threat, and investigate the root cause. They determine the scope of impact, affected assets, and potential entry points, ensuring incidents are understood in context.
- Incident response and containment If a real threat is confirmed, the provider initiates predefined response actions, which may include isolating affected systems, blocking IP addresses, or disabling compromised credentials. Some actions are automated, while others require analyst involvement.
- Reporting and communication SOCaaS providers deliver regular reports on detected threats, incident timelines, system health, and compliance metrics. They also maintain open communication channels for real-time updates, escalations, and client queries.
- Platform management and maintenance The provider manages the underlying security platforms, including SIEM, SOAR, and endpoint detection tools. This includes tasks like rule updates, performance tuning, software upgrades, and integration of new data sources.
- Compliance and audit support SOCaaS teams assist with regulatory compliance by maintaining detailed event logs, investigation records, and incident reports. They provide documentation and support during audits for standards such as HIPAA, PCI DSS, or ISO 27001.
- Continuous improvement and advisory Providers offer guidance on improving the client’s security posture over time. This may involve threat modeling, security architecture reviews, or recommendations for policy updates and vulnerability remediation.
SOC as a Service Compared to Other Models
SOCaaS vs. In-House SOC Operations
SOCaaS replaces the need to build and operate a dedicated, internal SOC. In a traditional setup, companies must recruit, train, and retain a team of skilled analysts, a process that takes time and presents significant costs. With SOCaaS, organizations offload these challenges, gaining instant access to both human and technical expertise.
Additionally, traditional SOCs often struggle to maintain 24/7 coverage due to staff shortages or turnover. SOCaaS guarantees continuous vigilance, underpinned by contractual SLAs. This shift enables smaller organizations to match the protection levels of much larger enterprises without navigating resource or skill gaps associated with in-house teams.
SOCaaS vs. MDR
Managed detection and response (MDR) services focus on detecting, investigating, and responding to threats mainly at the endpoint. While there is overlap with SOCaaS in terms of scope, MDR is often more limited, emphasizing rapid detection, containment, and investigation of endpoint-centric incidents rather than holistic coverage.
SOCaaS is broader, incorporating network, endpoint, and cloud monitoring, along with log management, compliance reporting, and advisory functions. Organizations with complex or varied infrastructure needs typically find SOCaaS more aligned to their requirements, as it offers a more comprehensive suite of services than MDR alone.
SOCaaS vs. Managed SOC
A managed SOC usually augments or extends an organization’s in-house SOC with additional staff or capabilities. It often assumes the client is already running some security operations and seeks help filling skill or coverage gaps. In contrast, SOCaaS offers a fully outsourced, turnkey SOC function, requiring little internal security investment beyond integration and coordination.
SOCaaS is ideal for organizations seeking to outsource all security operations rather than supplement what they have. It delivers pre-integrated tools, staff, and response processes, minimizing the need for the client to manage multiple relationships or maintain internal SOC infrastructure.
SOCaaS vs. Outsourced SOC
Outsourced SOC generally refers to delegating some or all SOC functions to an external team, frequently via a custom engagement. SOCaaS builds on this idea but formalizes it as a standardized service model, delivered via the cloud, with economies of scale and service-level agreements.
SOCaaS providers often leverage automation, AI, and a mature service approach to deliver faster, more agile security operations. The standardized platform and processes in SOCaaS tend to allow for better scalability, reporting, and integration than traditional outsourced SOC models, which may be more bespoke but slower to evolve.
SOCaaS vs. SIEM-as-a-Service
SIEM-as-a-service provides hosted access to a security information and event management platform but typically leaves configuration, alert investigation, and response actions up to the client. SOCaaS, on the other hand, wraps SIEM functionality into an operational service, including staff, triage, incident handling, and ongoing tuning by the provider.
With SOCaaS, clients gain a turnkey solution where the provider manages the full lifecycle of threat monitoring and response. This coordinated approach drives faster mitigation of risks and eliminates the need for the client to dedicate resources to SIEM operation and optimization, resulting in a more complete security posture.
12 Notable SOCaaS Providers
Intezer

Intezer delivers an AI-powered SOC platform designed to augment in-house SOC teams and replace traditional MDR by removing human investigation capacity as a bottleneck. Instead of prioritizing alerts based on severity labels, Intezer autonomously triages and investigates 100% of alerts across endpoint, cloud, identity, network, and SIEM sources, escalating only verified incidents to humans for judgment and response.
Key features include:
-
Full alert investigation: Every alert is investigated, eliminating blind spots in low- and medium-severity events.
-
Deep forensic analysis: Proprietary endpoint scanning with live memory inspection validates active threats and confirms true remediation.
-
AI-driven detection engineering: Investigation outcomes continuously feed back into detection logic, improving coverage and tuning rules over time.
-
Fast, evidence-based verdicts: Investigations complete in minutes, with high-accuracy, explainable results.
-
No vendor lock-in: Detection improvements are deployed directly into the customer’s existing security stack.
Unlike traditional MDR services that are constrained by staffing and SLAs, Intezer’s model delivers complete coverage, continuous detection improvement, and measurable risk reduction, without requiring increased headcount. Additionally, Intezer’s deep forensic tooling and processes increases triage speed (under 1 minute) without incurring massive costs for LLM processing so customers can enjoy predictable pricing (by endpoint) unlike other providers who rely exclusively on AI or primarily on human labor.

eSentire

eSentire provides SOC-as-a-service through its MDR offering, supplying continuous monitoring, investigation, and response backed by dedicated threat hunters and cyber analysts. The service uses the Atlas XDR platform to disrupt known threats automatically while analysts focus on complex investigations, containment steps, and hands-on remediation.
Key features include:
- Around-the-clock analyst coverage: Uses two security operations centers staffed with certified analysts and threat hunters who monitor environments continuously and assist directly with detection, containment, and remediation activities.
- Platform-supported detection: Applies the Atlas XDR platform to disrupt high-fidelity threats automatically, allowing analysts to focus on multi-signal investigations and deeper response actions across monitored systems.
- Structured SOC workflow: Follows defined steps for detection, evaluation, investigation, and response, ensuring alerts are reviewed, incidents are validated, and remediation actions are communicated and executed when required.
- Rapid containment timelines: Targets initial response within seconds and delivers containment within minutes, operating with a reported mean time to contain.
- Unlimited threat hunting: Conducts continuous threat hunting informed by the threat response unit, enabling analysts to search for hidden indicators and review anomalous activity across multiple data signals.

Source: eSentire
Red Canary

Red Canary provides managed SOC services that deliver continuous threat detection, investigation, and response across endpoint, network, cloud, and identity environments. The service processes high-volume telemetry, applies behavioral detections, and uses human-led analysis to validate threats, correlate events, and coordinate remediation steps when adversary activity is identified.
Key features include:
- Broad threat coverage: Monitors endpoint, network, cloud, and identity sources to detect ransomware, account compromise, misconfigurations, and data exfiltration attempts across different parts of the attack surface.
- Behavior-based detection: Applies analytics and proprietary intelligence to examine streaming data for early-stage adversary techniques, allowing analysts to confirm threats that may not match traditional signatures.
- Human-led investigation: Reviews suspicious events, eliminates false positives, and correlates signals from multiple tools into unified timelines that describe root causes, affected assets, and potential impact.
- Automated and assisted response: Provides a combination of automated actions and analyst-guided remediation support to stop confirmed threats, focusing on containing adversary activity before it disrupts operations.
- Continuous data ingestion: Uses existing customer tools as telemetry sources, enabling the SOC to analyze large volumes of event data without requiring additional proprietary collection mechanisms.

Source: Red Canary
Expel

Expel delivers SOC-as-a-service through its human-led, AI-supported MDR platform that integrates with a customer’s existing security stack. Designed to reduce alert fatigue and enhance visibility, Expel’s Workbench™ platform enables security teams to focus on high-value work.
Key features include:
- Tool-agnostic integration: Works with the customer’s current environment, avoiding the need to rip and replace security tools or deploy proprietary agents.
- Experienced SOC analysts: Provides around-the-clock monitoring and incident response led by expert analysts who operate in the client’s environment.
- AI-supported triage and detection: Uses machine learning to cut alert noise and streamline analyst workflows, increasing efficiency and focus.
- Expel Workbench™ platform: Centralizes detection and response activities, giving teams visibility into security events, analyst actions, and incident timelines.
- Transparency and partnership: Offers access to analysts, updates, and metrics rather than filtered summaries, encouraging collaborative security operations.

Source: Expel SOC
Arctic Wolf

Arctic Wolf delivers SOC-as-a-service through its Security Operations Cloud, powered by the Aurora platform. The service offers broad visibility across endpoint, network, identity, and cloud environments, with AI-driven threat detection, monitoring, and tailored security operations.
Key features include:
- Security Operations Cloud: Unifies threat detection and response across all telemetry sources using a cloud-native platform with integrated analytics.
- Alpha AI detection engine: Applies machine learning to detect advanced threats, reduce false positives, and streamline analyst workflows.
- Broad telemetry collection: Processes over 9 trillion events per week from existing endpoint, network, identity, and cloud infrastructure.
- Threat enrichment and digital risk quantification: Correlates events with threat intelligence to provide context-aware insights into misconfigurations, vulnerabilities, and account risks.
- Customized detection rules: Detection logic tailored to each environment improves fidelity and reduces alert fatigue.
ReliaQuest

ReliaQuest offers MDR and SOC-as-a-service through its GreyMatter platform, which centralizes detection, investigation, and response across a customer’s security ecosystem. It supports hybrid operations by combining human-led expertise with automation to improve threat coverage, reduce alert fatigue, and drive improvements.
Key features include:
- GreyMatter platform: A unified interface that integrates SIEM, EDR, and other security tools to provide centralized visibility and investigation capabilities.
- Cross-tool detection engineering: Builds and tunes detection rules across the customer’s existing tech stack, regardless of vendor, to maximize value from current investments.
- Mature operational metrics: Tracks and reports on SOC performance, including detection coverage, MTTR, and response effectiveness.
- Automated investigation and response: Uses playbooks and orchestration to accelerate triage and remediation while keeping analysts in control.
- Threat modeling and purple teaming: Helps identify detection gaps and validate coverage with simulated attacker techniques mapped to MITRE ATT&CK.

Source: ReliaQuest
CrowdStrike Falcon MDR

CrowdStrike Falcon Complete is a managed detection and response (MDR) service that delivers 24/7 expert-led, AI-accelerated protection across endpoints, cloud, identity, and other domains. Built on the Falcon platform, it combines human analysts, real-time telemetry, and generative AI to detect, investigate, and remediate threats.
Key features include:
- Full-cycle threat response: The Falcon Complete team handles end-to-end detection, investigation, and remediation without escalating work back to the customer.
- Expert-led and AI-accelerated operations: Combines analyst expertise with CrowdStrike Charlotte AI to investigate and respond at machine speed.
- All-domain visibility: Provides detection across endpoints, identities, cloud workloads, and third-party data using integrated Next-Gen SIEM capabilities.
- Threat hunting with Adversary OverWatch: Offers continuous, intelligence-driven threat hunting across the enterprise attack surface.
- Real-world attack disruption: Identifies and neutralizes lateral movement, ransomware, phishing, and other tactics before they cause damage.

Source: CrowdStrike
Sophos MDR

Sophos delivers managed detection and response as an integrated service combining AI-driven threat detection with hands-on analyst support. It offers 24/7 monitoring, incident response, and threat hunting across any environment, regardless of whether Sophos tools are in use.
Key features include:
- 24/7 SOC operations: Real-time monitoring and response by global analysts with deep security expertise.
- AI-powered detection platform: Centralized system ingests and correlates data from multiple technology sources.
- Threat hunting and research: Proactive investigations uncover adversary behavior and inform custom detection rules.
- Flexible service tiers: Supports multiple deployment models and response options tailored to organizational needs.
- Broad integration support: Compatible with both Sophos and third-party tools to maximize return on existing investments.

Source: Sophos
BitDefender

BitDefender offers SOC-as-a-service capabilities as part of its broader managed security portfolio. The platform combines real-time threat prevention with low-impact endpoint protection, designed for high effectiveness and minimal system performance impact.
Key features include:
- Multi-platform protection: Secures Windows, macOS, Android, and iOS devices with a unified detection engine.
- Malware and ransomware defense: Continuously detects and blocks a wide range of threats using behavioral analytics.
- Email and scam protection: Monitors email content and links for phishing and scam indicators.
- Lightweight performance: Operates silently in the background, avoiding user disruption or system slowdown.
- Identity breach detection: Alerts users to data leaks or unauthorized access based on breach monitoring.

Source: Bitdefender
Huntress

Huntress delivers MDR with a 24/7 human-led, AI-assisted SOC that provides full-lifecycle threat detection and response. Its services include managed EDR, identity threat detection, and managed SIEM, designed for mid-sized organizations and service providers.
Key features include:
- Managed EDR: Provides real-time detection, disruption, and remediation across 4.5 million protected endpoints.
- Expert threat hunting: Combines machine assistance with analyst investigation to identify and eliminate active threats.
- Simplified onboarding: Deploys rapidly, typically within 30 minutes, without requiring major infrastructure changes.
- Purpose-built platform: Developed in-house to support detection through response with complete operational control.
- Clear, actionable alerts: Prioritizes real threats and suppresses unnecessary noise to reduce analyst overload.
Rapid7 MDR

Rapid7 MDR provides 24/7 managed detection and response built on its Insight platform, combining extended detection and response (XDR), endpoint protection, vulnerability management, and expert-led threat hunting.
Key features include:
- 24/7 global SOC coverage: Around-the-clock monitoring and response with exposure-led threat detection.
- One universal Insight Agent: Enables EDR and XDR with telemetry collection across endpoints.
- Proactive threat hunting: SOC analysts use emerging indicators and attacker behavior to identify threats before they escalate.
- Vulnerability management integration: Continuously scans environments to detect and prioritize software and system vulnerabilities.
- Active response and SOAR: Automates or executes immediate response actions with analyst-driven containment and orchestration.
Source: Rapid7 MDR
Daylight

Daylight delivers MDR through an autonomous, agentic AI platform combined with human expertise. The service provides adaptive, context-aware detection and response with no blind spots, operating via tight integrations with security and IT systems and supporting full-scale containment without escalation.
Key features include:
- Agentic AI fused with human expertise: Combines machine-speed detection and triage with expert-led investigations to reduce false positives and response delays.
- End-to-end response without escalation: Delivers custom, context-rich remediation through ChatOps and other integrations, no handoffs required.
- Full coverage of the environment: Integrates with all security and IT systems, and builds new integrations as needed within days.
- Context-aware detection: Continuously learns from historical data, system behavior, and communications (like Slack) to tailor alerts and responses.
- Real-time performance dashboards: Tracks threats, MTTR, and ROI, providing full transparency and measurable security outcomes.
Considerations for Selecting a SOC as a Service Provider
Choosing the right SOCaaS provider is critical to ensuring your organization receives effective, scalable, and responsive security coverage. Below are key and unique considerations to guide the selection process:
- Depth of threat detection capabilities: Evaluate how the provider detects threats across network, endpoint, cloud, and identity environments. Look for behavioral analytics, machine learning models, and support for custom detection logic to handle both common and novel attack vectors.
- Customization and integration flexibility: Assess whether the SOCaaS platform can integrate with your existing tools (e.g., firewalls, EDR, SIEM, IAM) and how well it supports custom rules, workflows, or escalation paths tailored to your risk profile and IT stack.
- Staff expertise and involvement: Verify the qualifications and availability of the analysts handling your environment. Ensure the team includes certified professionals capable of performing deep investigations, not just automated triage.
- Response capabilities and playbooks: Determine what level of incident response the provider includes, such as automated actions, hands-on containment, and post-incident reporting, and whether response playbooks can be customized for your organization.
- Transparency and reporting: Ensure the client portal provides real-time visibility into events, incidents, and performance metrics. The ability to audit analyst actions, access logs, and generate compliance-ready reports is essential.
- Scalability and service tiers: Review how the provider handles scaling up to meet growing demands, and whether different service tiers are available that align with your budget, compliance needs, and risk tolerance.
- Data residency and privacy compliance: Confirm where your log and telemetry data is stored and processed, especially if your organization is subject to data residency laws or sector-specific privacy regulations.
- Service level agreements (SLAs): Pay attention to SLAs for threat detection, alert validation, and incident response. These should include measurable timelines and clearly defined responsibilities to support accountability.
- Onboarding process and time to value: Assess how quickly the provider can begin monitoring your environment, including their deployment model, data ingestion readiness, and how much internal effort is required during setup.
- Continuous improvement and threat intelligence use: Look for providers that proactively tune detection rules, conduct threat hunting, and incorporate real-world threat intelligence to evolve protection over time.
Conclusion
SOC as a Service offers organizations a comprehensive, scalable, and cost-effective alternative to building and operating an in-house security operations center. By outsourcing critical security functions, such as threat detection, incident response, and platform management, to specialized providers, businesses gain access to expert personnel, advanced tools, and 24/7 coverage without the overhead of managing it themselves.