What are Managed Detection and Response (MDR) Providers?
MDR (Managed Detection and Response) providers offer outsourced cybersecurity services, combining technology with expert analysts for 24/7 threat monitoring, investigation, and response. Leading solutions include Intezer, eSentire, and Sophos MDR.
Managed Detection and Response (MDR) providers typically focus on threat detection, investigation, and active response. Unlike traditional managed security service providers (MSSPs) that mostly monitor security alerts, MDR providers use advanced analytics, machine learning, and human expertise to proactively identify and resolve potential security incidents. They bridge the knowledge and resource gap for organizations that lack an in-house security operations center (SOC) or sophisticated threat detection capabilities.
MDR services cover a range of environments, including cloud, on-premises, and hybrid infrastructures. They provide round-the-clock monitoring and support in order to catch threats that automated tools or internal teams might miss. With dedicated teams focused solely on identification, investigation, and response, MDR providers significantly improve an organization’s security posture without the overhead of building a full-scale, in-house SOC.
Why Organizations Use MDR Providers Today
Organizations are turning to MDR providers as modern threats grow more complex, faster-moving, and harder to detect using traditional security tools. Below are the key reasons why MDR adoption is increasing:
- Need for 24/7 monitoring and response: Threat actors often operate outside of normal business hours. MDR services ensure continuous monitoring, threat detection, and incident response, reducing the risk of prolonged dwell times and delayed mitigation.
- Overwhelming volume of security alerts: Security tools often generate thousands of alerts, many of which are false positives. MDR providers filter and investigate alerts, ensuring only real and actionable threats are escalated, reducing alert fatigue.
- Advanced threat detection capabilities: MDR solutions use machine learning, behavioral analytics, and threat intelligence to detect sophisticated attacks that evade traditional signature-based defenses.
- Faster incident containment and response: MDR providers offer rapid investigation and containment services, such as isolating infected endpoints or blocking malicious traffic, reducing the time and impact of a breach.
- Support for compliance and reporting: MDR providers often assist with compliance by generating detailed reports, maintaining audit trails, and helping meet regulatory requirements related to incident detection and response.
- Cost-effective alternative to building a SOC: Building and operating an in-house security operations center is expensive and resource-intensive. MDR provides many of the same benefits at a lower cost and with faster time to value.
Core Components of an MDR Service
Continuous Telemetry Collection Across Environments
Continuous telemetry collection forms the backbone of any MDR service. MDR providers deploy agents or connect to existing logging and monitoring tools to gather relevant security data from endpoints, servers, cloud instances, and network devices. The breadth and depth of this telemetry ensure comprehensive visibility, enabling the identification of anomalous behaviors that could signal compromise, regardless of where an attack originates.
Collecting telemetry from diverse environments is critical as organizations increasingly operate in hybrid or multi-cloud scenarios. MDR providers normalize and centralize this data, making it easier to detect patterns and correlate events across a distributed infrastructure. This proactive approach to data collection allows for faster detection, more accurate threat hunting, and improved context during investigations.
Threat Detection Engineering And Analytics
Effective MDR services rely on advanced detection engineering to sift through massive volumes of collected telemetry. This involves continuously fine-tuning detection rules, leveraging threat intelligence feeds, and using behavioral analytics to differentiate benign activity from genuine threats. Machine learning models often supplement these efforts, automating the identification of previously unknown attack patterns and reducing reliance on static signatures.
Analytics engines within MDR platforms prioritize high-fidelity alerts, reducing noise and focusing analysts’ attention on events that warrant immediate investigation. By integrating contextual and environmental information, MDR providers can detect subtle or multi-stage threats that elementary tools would miss. This depth of analytics is a defining feature that sets MDR apart from legacy monitoring solutions.
Human-Led Investigation And Validation
While automation is essential for scaling detection, human expertise remains necessary for interpreting nuanced incidents and minimizing false positives. MDR providers employ security analysts who investigate, triage, and validate alerts generated by software. Their contextual awareness and experience allow for quicker, more accurate assessment and action against emerging threats or targeted attacks.
Analyst-led investigation also ensures customers receive actionable threat intelligence and practical remediation steps. Rather than flooding clients with generic alerts, MDR services deliver tailored guidance that takes into account an organization’s environment and risk tolerance. This human-centered model makes MDR services critical for effective incident handling and contextual decision-making.
Active Response And Containment Actions
MDR services go beyond detection by offering real-time, hands-on response capabilities. When a verified threat is detected, MDR teams can isolate affected devices, suspend malicious accounts, or implement custom blocking rules directly within the customer’s environment. This immediate containment limits the impact of attacks and buys time for further investigation and remediation.
Active response actions are guided by pre-established playbooks and are typically executed with client approval or according to strict service-level agreements. By taking decisive, targeted actions at any hour, MDR providers help mitigate threats before they escalate into major incidents, preserving business continuity and reducing potential losses.
MDR Providers Use Cases
Threat Detection in Hybrid and Cloud Environments
Modern infrastructures are rarely confined to a single environment. Most organizations operate across a mix of on-premises systems, public clouds, and SaaS platforms. This distribution creates blind spots for traditional monitoring tools, especially when security controls vary between environments. MDR providers bridge this gap by collecting telemetry across all layers—endpoint, network, identity, and cloud—centralizing visibility.
MDR services integrate with platforms like AWS, Azure, and Google Cloud to detect misconfigurations, unauthorized access, and lateral movement. They also correlate cloud activity with on-premises data to catch cross-environment attack paths that might go unnoticed in siloed systems. This unified view improves detection accuracy and ensures threats are identified regardless of where they originate or how they traverse the infrastructure.
Rapid Response to Ransomware Attacks
Ransomware campaigns often unfold quickly, encrypting critical systems in minutes. Traditional detection methods may spot the initial intrusion but fail to respond fast enough to stop propagation. MDR providers are structured to intervene in real-time. Their teams monitor for early indicators like suspicious file encryption behavior, privilege escalation, or known ransomware signatures.
Once detected, MDR teams can isolate infected hosts, disable compromised credentials, and block command-and-control communications before data loss or widespread impact occurs. Some providers offer automated containment backed by human validation, ensuring speed without sacrificing accuracy. This rapid response capability is key to minimizing downtime, data exposure, and operational disruption during ransomware incidents.
Augmenting Overstretched Security Teams
Internal security teams often face personnel shortages and skill gaps, particularly in threat detection and incident response. MDR services act as an extension of these teams, providing continuous monitoring, triage, and investigation without requiring additional internal headcount.
By offloading alert validation and initial response actions, MDR providers free internal staff to focus on strategic initiatives and higher-priority issues. They also bring specialized expertise, such as reverse engineering or threat hunting, that smaller teams may lack. This model is especially beneficial for mid-sized organizations that struggle to recruit and retain experienced security professionals.
Early Detection of Targeted or Insider Threats
Targeted attacks and insider threats are difficult to detect using signature-based tools alone, as they often involve subtle misuse of legitimate credentials or applications. MDR providers leverage behavioral analytics and anomaly detection to identify deviations from normal user or system activity that may indicate malicious intent.
Analysts investigate these anomalies in context—considering factors like time of access, data accessed, and deviation from established patterns—to catch threats early in the kill chain. For insider threats, this might mean detecting data exfiltration attempts or privilege abuse. For targeted attacks, it may involve identifying command-and-control traffic or the use of living-off-the-land techniques. In both cases, early detection enables a timely and effective response.
1. Intezer

While traditional MDR providers were built to extend human monitoring capacity, they remain constrained by the same fundamental limitation: human investigation does not scale with alert growth. As environments expand and attackers increasingly leverage automation and AI, MDR teams are forced to prioritize only high-severity alerts, often before full context is available, leaving low and medium alerts uninvestigated. This creates hidden backlog risk and blind spots that customers ultimately carry.
Intezer AI SOC replaces MDR by removing human capacity as the bottleneck entirely.
Instead of outsourcing investigation to a shift-based service model, organizations use Intezer’s AI SOC platform to investigate 100% of alerts autonomously, regardless of severity. Every alert is triaged and analyzed at forensic depth across endpoint, cloud, identity, network, and SIEM telemetry. Alerts are correlated into evidence-backed cases, not handled as isolated tickets. Only the small percentage of alerts that represent real risk are escalated to humans for judgment and response.
This represents a structural shift in operating model:
- From selective investigation to full alert coverage
- From SLA-driven triage to evidence-driven verdicts
- From periodic rule tuning to AI-driven, closed-loop detection engineering
- From outsourcing execution to supervising outcomes
Unlike MDR services that operate as black boxes, Intezer delivers transparent, explainable verdicts grounded in forensic analysis. Investigations analyze behavior, process lineage, execution artifacts, and relationships to determine what actually happened, not just whether an alert matches a predefined severity label.
Beyond investigation, Intezer continuously strengthens detection posture. Investigation outcomes feed directly back into detection engineering, identifying noisy rules, broken detections, and coverage gaps mapped to MITRE ATT&CK. This closed-loop model ensures that security posture improves over time, rather than stagnating under static rule sets.
The result is not just faster alert handling, it is structural risk reduction:
- No backlog of untouched alerts
- No silent threats hiding in “low severity” signals
- No dependence on staffing ratios to determine security outcomes
- No forced trade-offs between coverage and sustainability
Security teams regain control. Humans focus on supervision, escalation decisions, and strategic improvement, not grinding through tickets. Operations scale without proportional headcount growth.
MDR was designed to compensate for limited internal resources. Intezer eliminates the need for that compensation model entirely. By delivering forensic-grade investigation at machine scale, Intezer enables organizations to bring security operations back in-house, achieve full alert coverage, and reduce risk in a way human-scaled MDR services fundamentally cannot.
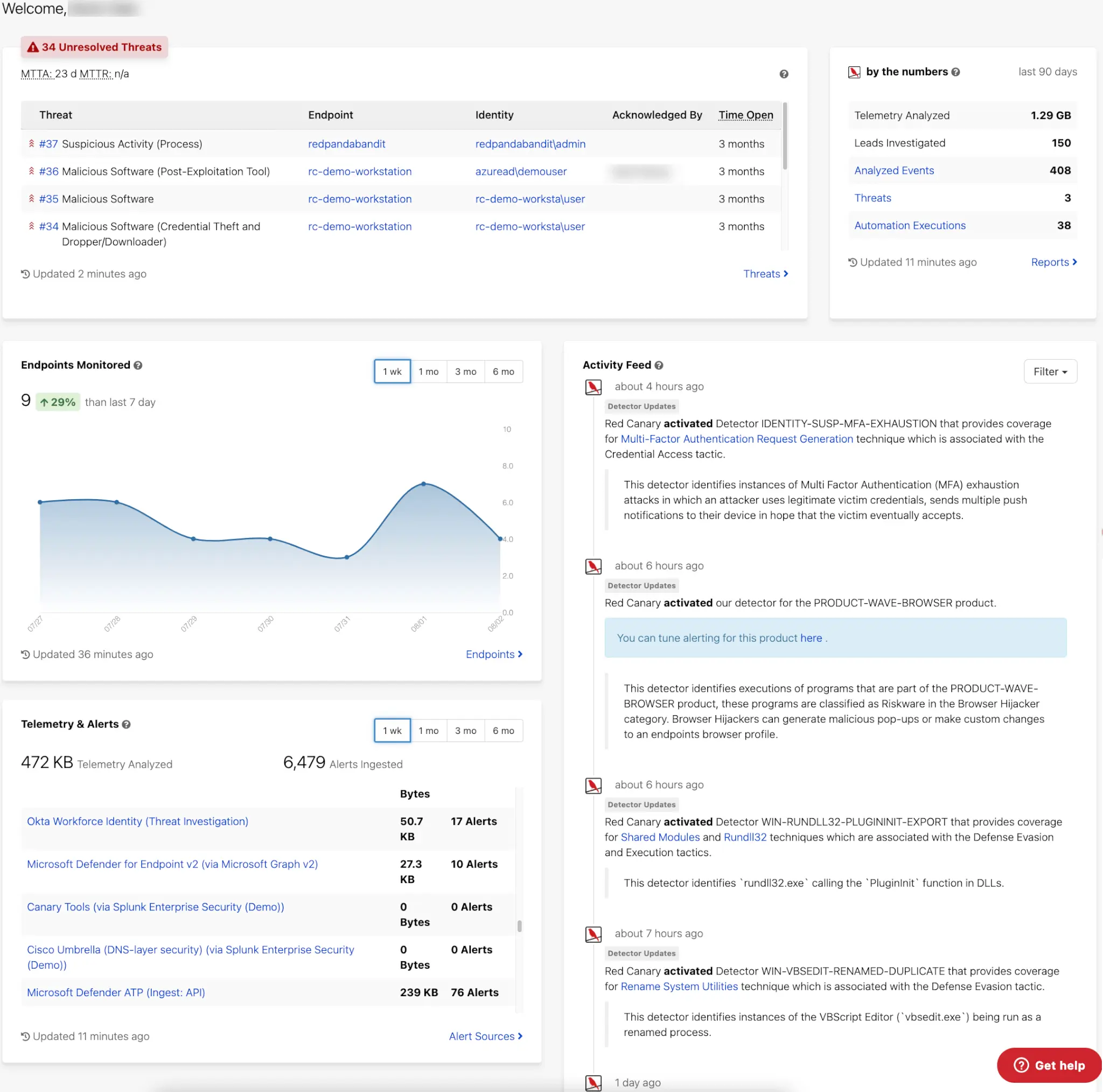
2. Red Canary

Red Canary provides managed MDR services that deliver continuous threat detection, investigation, and response across endpoint, network, cloud, and identity environments. The service processes high-volume telemetry, applies behavioral detections, and uses human-led analysis to validate threats, correlate events, and coordinate remediation steps when adversary activity is identified.
Key features include:
- Broad threat coverage: Monitors endpoint, network, cloud, and identity sources to detect ransomware, account compromise, misconfigurations, and data exfiltration attempts across different parts of the attack surface.
- Behavior-based detection: Applies analytics and proprietary intelligence to examine streaming data for early-stage adversary techniques, allowing analysts to confirm threats that may not match traditional signatures.
- Human-led investigation: Reviews suspicious events, eliminates false positives, and correlates signals from multiple tools into unified timelines that describe root causes, affected assets, and potential impact.
- Automated and assisted response: Provides a combination of automated actions and analyst-guided remediation support to stop confirmed threats, focusing on containing adversary activity before it disrupts operations.
- Continuous data ingestion: Uses existing customer tools as telemetry sources, enabling the SOC to analyze large volumes of event data without requiring additional proprietary collection mechanisms.
3. eSentire MDR Services

eSentire delivers an MDR solution built on multi-signal telemetry, integrated AI, and 24/7 expert-driven threat response. Its Atlas Security Operations Platform combines AI automation with human expertise to detect and respond to threats across the entire attack surface, including endpoints, network, cloud, and identity.
Key features include:
- Multi-Signal Coverage: Aggregates telemetry across endpoints, network, logs, cloud, identity, assets, and vulnerabilities for full visibility
- Atlas XDR Platform: AI-driven platform automates threat blocking and reduces investigation time from hours to minutes
- 24/7 SOC Operations: Expert analysts provide around-the-clock threat monitoring, investigation, and response
- Integrated AI + Human Threat Hunters: Proprietary AI detects novel threats while Elite Threat Hunters validate and act on findings
- Active Response Capabilities: Supports host isolation, malicious traffic blocking, and account suspension to contain threats

Source: eSentire
4. Sophos MDR

Sophos MDR delivers 24/7 managed detection and response through a combination of AI-native technology and a global team of security experts. Designed to integrate with an organization’s existing tools, Sophos MDR centralizes telemetry from multiple sources and applies advanced analytics to detect, investigate, and respond to threats in real time.
Key features include:
- 24/7 Global SOC: Around-the-clock monitoring, detection, and response delivered by experienced analysts
- AI-Native Platform: Consolidates and analyzes telemetry across multiple tools for prioritized, high-fidelity alerts
- Proactive Threat Hunting: Combines lead-based and hypothesis-driven methods to detect stealthy adversaries
- Complete Incident Response: Full-scale mitigation and remediation included, with no additional fees
- Industry-Leading Threat Research: Ongoing discovery of new threat groups and techniques informs detection updates
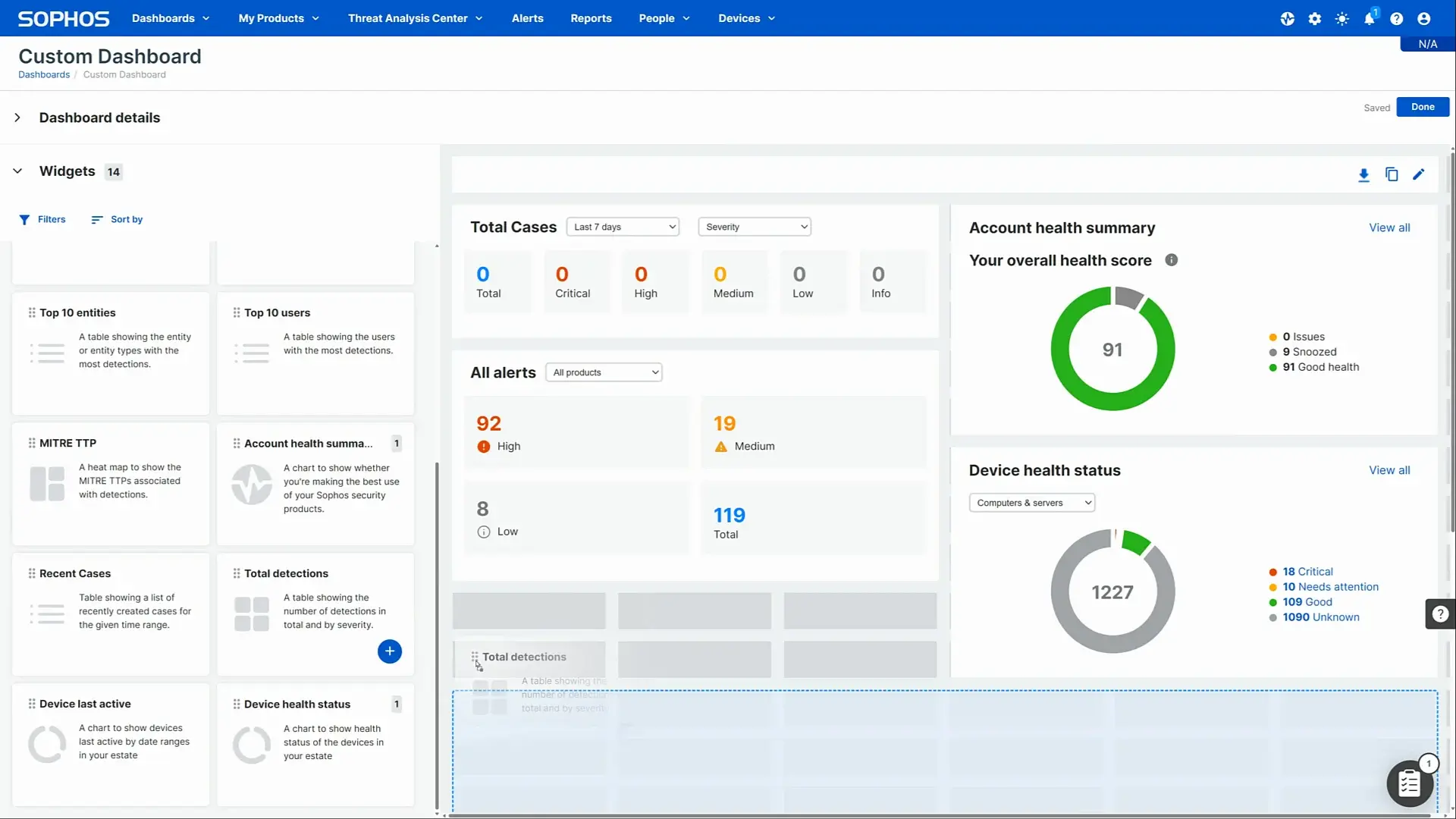
Source: Sophos
5. AirMDR

AirMDR delivers AI-powered managed detection and response tailored for lean security teams. Its platform automates the triage of 90% of alerts in under five minutes, ensuring full alert coverage across endpoint, email, identity, cloud, and SaaS environments. AirMDR combines speed with expert-reviewed investigations, offering audit-ready case reports without relying solely on AI decisions.
Key features include:
- AI-Led Alert Triage: Automatically processes 90% of alerts in under 5 minutes, reducing noise and response time
- Expert-Backed Investigations: Human analysts review and respond to critical threats, fine-tuning outcomes when needed
- Complete Signal Coverage: Monitors and investigates telemetry across endpoints, cloud, identity, email, and SaaS tools
- Full Alert Coverage: No blind spots—every alert is triaged, minimizing analyst burnout and overlooked incidents
- Transparent Case Reporting: Clear, audit-ready explanations for every case with no black-box decision-making
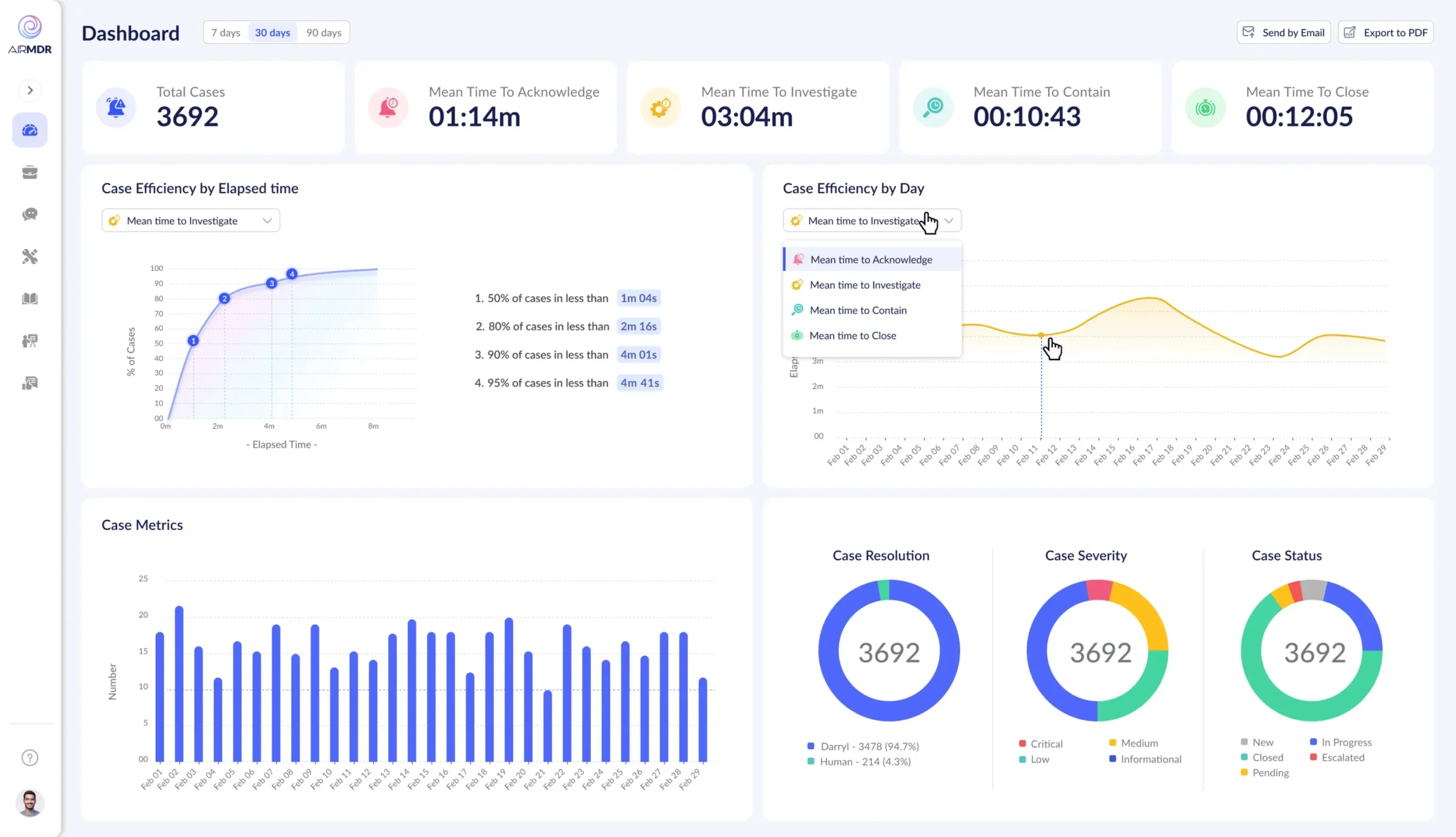
Source: AirMDR
6. Sentinelone Wayfinder MDR

SentinelOne Wayfinder MDR delivers 24/7/365 managed detection and response by combining curated threat intelligence from Google and SentinelOne with expert human analysts and AI-driven automation. Operating natively within the Singularity Platform, Wayfinder MDR offers seamless coverage across endpoints, cloud, identity systems, and third-party telemetry.
Key features include:
- Curated Global Threat Intelligence: Integrates real-time, high-fidelity intelligence from Google and SentinelOne to detect emerging threats early
- AI + Human Operations: Combines Singularity Hyperautomation and Purple AI with certified incident responders for decisive, round-the-clock protection
- Native Singularity Platform Integration: Delivers unified response without fragmented workflows, reducing operational friction
- Proactive Threat Hunting: Hypothesis-driven hunts based on tactics, techniques, and procedures (TTPs) to uncover stealthy or early-stage attacks
- Tailored Incident Response: MDR Elite customers get dedicated threat advisors, DFIR experts, and access to incident readiness retainers

Source: SentinelOne
7. BitDefender MDR

Bitdefender MDR delivers 24/7 managed detection and response through a global network of SOCs, combining elite human expertise with a best-in-class security platform. The service manages the entire alert lifecycle, from detection and analysis to containment and remediation, so internal teams aren’t burdened with triage.
Key features include:
- 24/7 Global SOC Coverage: Around-the-clock monitoring and response, including after-hours incidents, with real-time engagement from security account managers
- Human-Led Incident Response: Analysts perform deep investigations and execute pre-approved actions to contain threats quickly and reduce risk
- Root Cause & Impact Analysis: Every major incident includes a full investigation into initial threat vectors and detailed after-action reporting
- Dark Web Threat Hunting: Continuous monitoring for leaked data, compromised credentials, and brand risks across the dark web
- Expert Guidance: Security specialists provide actionable recommendations to improve overall security posture and resilience

Source: Bitdefender MDR
8. Expel MDR

Expel MDR delivers 24/7 managed detection and response by integrating directly with your existing security stack. Its approach focuses on reducing noise, accelerating time to resolution, and giving customers clear, actionable answers rather than raw alerts. The service combines automated triage through its AI engine, Ruxie, with expert human analysis.
Key features include:
- Agentless Deployment: Quickly integrates with over 160 existing tools without requiring agents or platform replacement
- Expel Workbench Platform: Centralized interface delivers real-time visibility, enriched context, and clear remediation guidance
- Fast Time to Resolution: Median time to resolution (MTTR) of 13 minutes through automated triage and analyst validation
- Unified Detection Coverage: Correlates attacker behavior across endpoints, cloud, identity, and more to eliminate blind spots
- Ruxie AI Engine: Automates triage and event analysis, allowing analysts to focus on the most relevant 1% of alerts
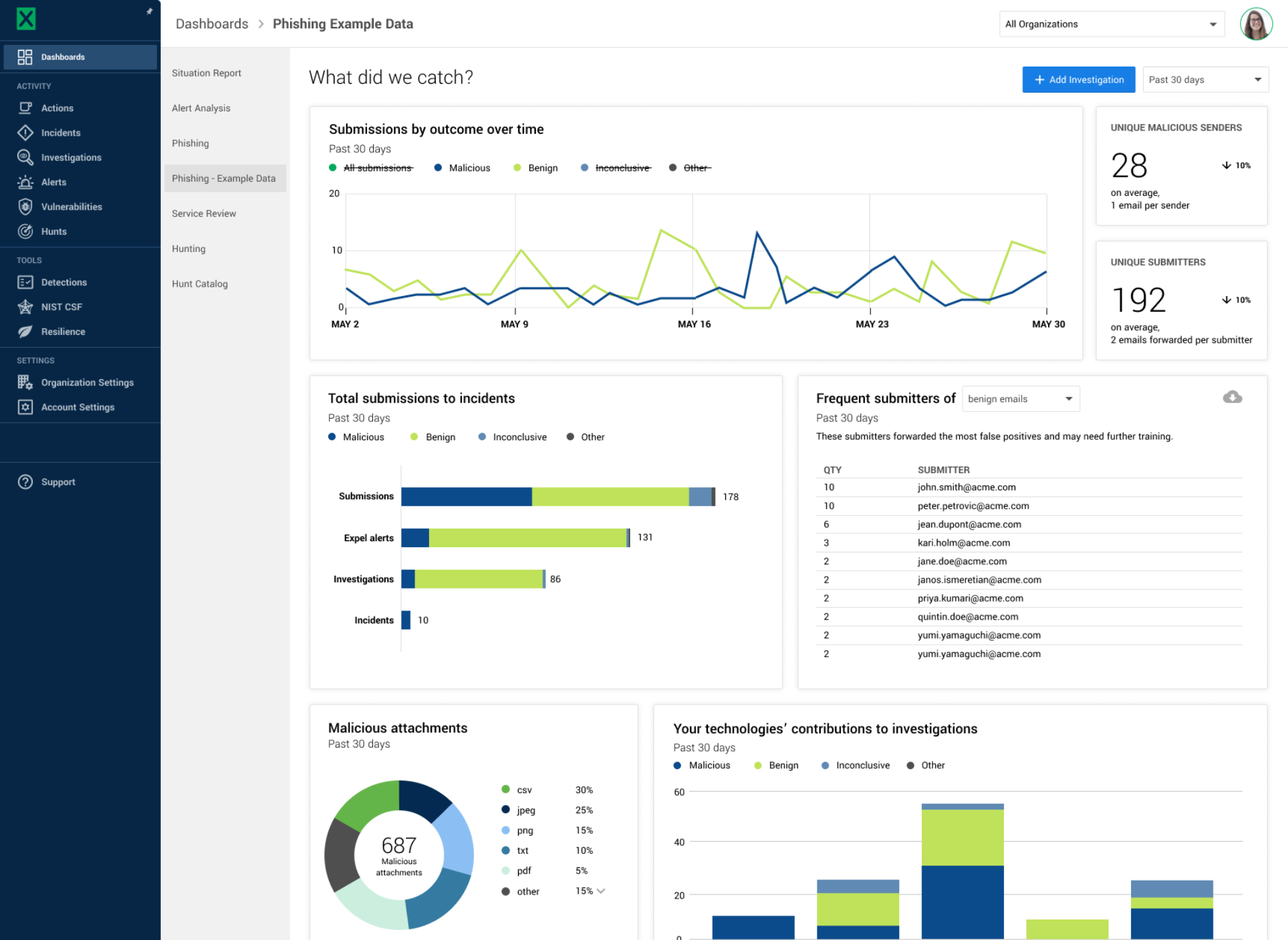
Source: Expel
9. Rapid7 MDR

Rapid7 MDR provides 24/7 managed detection and response through a unified MXDR (Managed Extended Detection and Response) service that integrates risk management, threat detection, and incident response across your entire environment. Built on Rapid7’s Insight platform, the service synthesizes telemetry from both native and third-party tools. It has no caps on incident response, dedicated security advisors, and visibility into SOC activity.
Key features include:
- 24/7 Global SOC Coverage: Round-the-clock monitoring and response with an exposure-led approach tailored to your environment
- Extended Ecosystem Monitoring: Correlates alerts from both Rapid7 and third-party tools to deliver unified, context-rich detections
- Comprehensive Threat Containment: Rapid incident response powered by complete environment visibility, with no limits on DFIR actions
- Insight Platform Integration: Full transparency into SOC activity through Rapid7’s XDR and SIEM tools, not a black-box approach
- Dedicated Security Advisor: Continuous tuning and guidance from an expert assigned to your environment
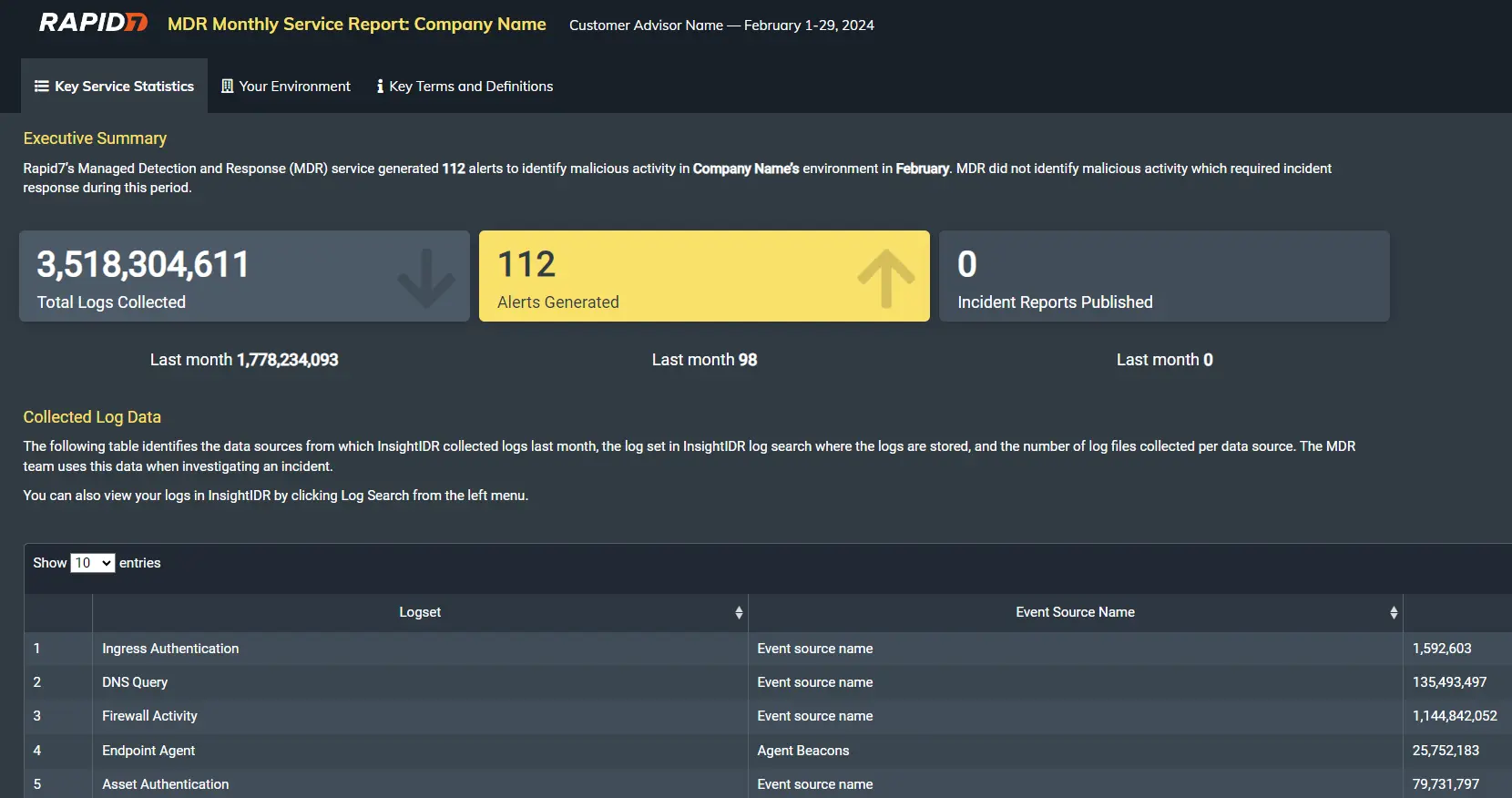
Source: Rapid7
10. Trend Micro MDR

Trend Micro MDR, delivered through the Trend Vision One™ platform, provides 24/7 managed detection and response across email, endpoints, servers, cloud workloads, and network environments. The service integrates telemetry from across these layers to detect and investigate threats with speed and precision, backed by Trend Micro’s global threat research and security analytics.
Key features include:
- 24/7 Cross-Layered Monitoring: Continuously monitors and correlates alerts across endpoints, email, cloud, servers, and networks to reduce noise and highlight high-risk threats
- Expert-Led Threat Investigation: Skilled analysts conduct deep threat analysis, including root-cause investigation, attack vector tracing, and impact assessment
- Integrated Threat Intelligence: Leverages Trend Micro’s global research to enrich investigations with up-to-date indicators of compromise (IoCs) and attacker behavior
- Direct Analyst Support: Customers can engage directly with analysts during investigations and receive detailed incident reports and executive summaries
- Step-by-Step Remediation: Includes threat containment, IoC generation, recovery guidance, and custom cleanup tools for effective threat eradication
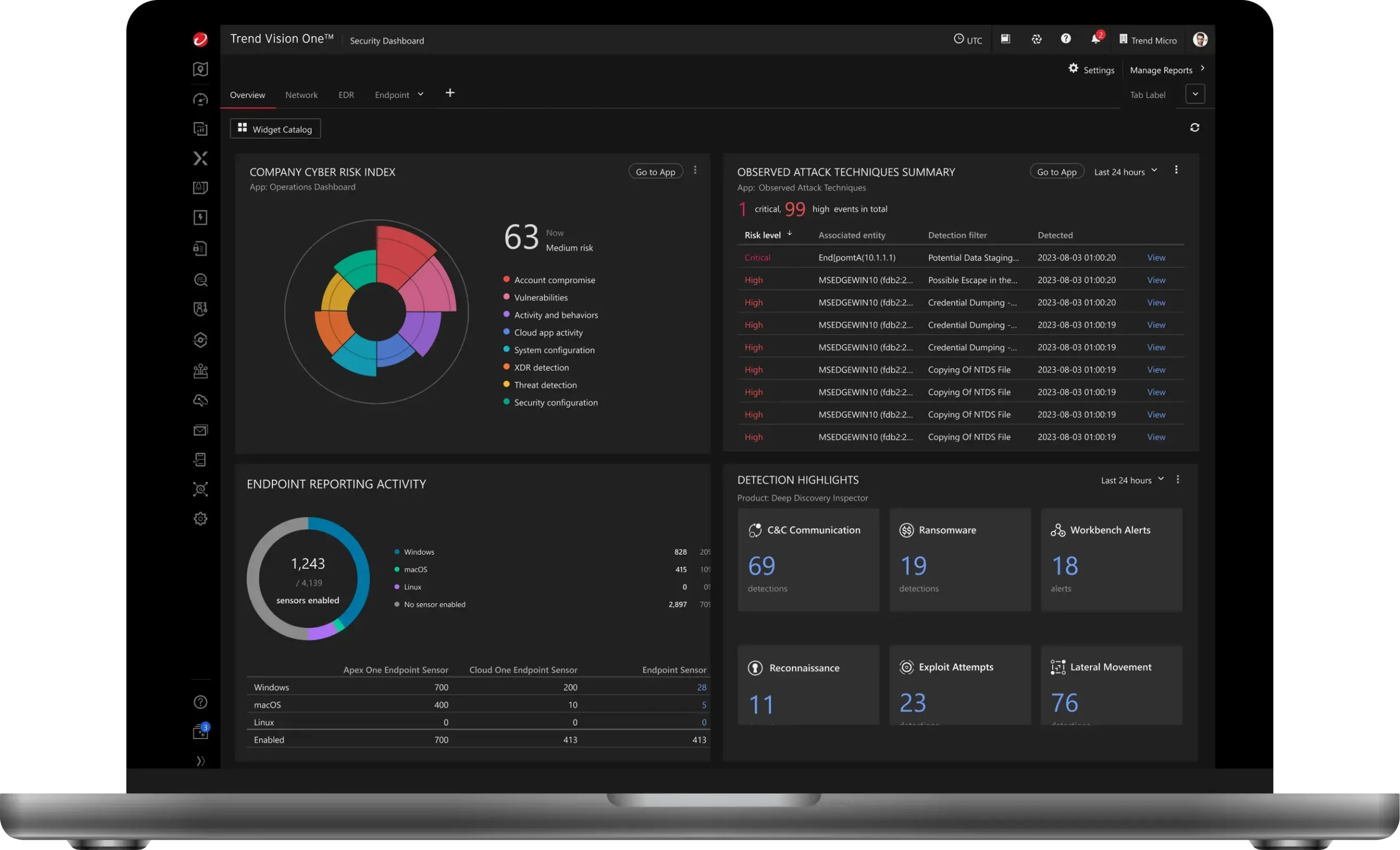
Source: Trend Micro MDR
11. Palo Alto Cortex MDR

Palo Alto Networks’ Cortex MDR, delivered through Unit 42, provides 24/7 managed detection and response built on the Cortex XDR platform. This service combines world-class threat intelligence, expert analysts, and advanced automation to detect, investigate, and remediate threats across endpoint, network, and cloud environments. Unit 42 leverages Palo Alto’s internal SOC processes and proprietary tooling to reduce alert fatigue and speed up threat response.
Key features include:
- 24/7 Expert-Led Monitoring: Around-the-clock threat detection and triage across endpoint, network, and cloud environments
- Built on Cortex XDR: Uses automated data correlation and telemetry across multiple sources to enrich alerts with context and reduce dwell time
- Unit 42 Threat Hunting: Proactive, hypothesis-driven hunting conducted by experienced analysts using the latest IOCs and TTPs
- Guided Remediation: Provides step-by-step support to contain and eliminate threats, including direct analyst engagement when needed
- Threat Intelligence Integration: Powered by Unit 42’s global telemetry—500B daily events and 30M+ malware samples—to inform detection and response

Source: Cortex
12. Huntress Managed ITDR

Huntress Managed ITDR delivers 24/7 identity threat detection and response, built specifically to defend against modern identity-based attacks like credential theft, session hijacking, rogue OAuth apps, and business email compromise. Backed by an AI-assisted SOC, the service monitors user activity across Microsoft 365 environments to detect and respond to threats in real time.
Key features include:
- 24/7 SOC Coverage: AI-assisted security operations team monitors identity threats continuously, ensuring rapid detection and response
- Fast Time to Respond: Achieves a 3-minute MTTR by validating alerts and taking swift action against confirmed identity threats
- Low False Positive Rate: <5% false positives through human-reviewed alerts, so teams only act on what matters
- Session Hijacking Detection: Identifies stolen session tokens and blocks unauthorized access—even when MFA is bypassed
- Credential Theft Protection: Secures identity workflows to prevent attackers from using stolen usernames and passwords
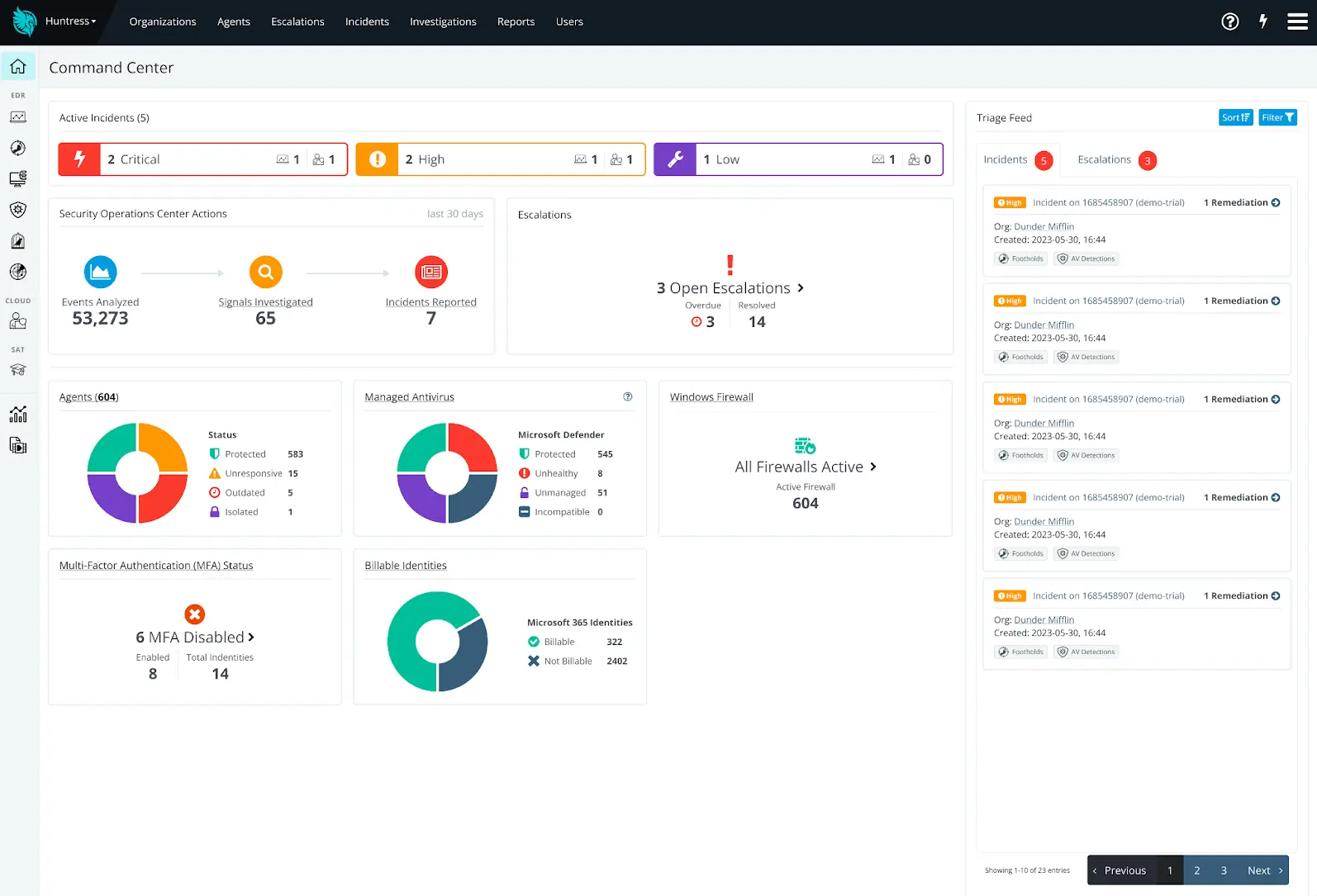
Source: Huntress
How to Evaluate and Select an MDR Provider
1. Detection and Response Depth
When evaluating MDR providers, organizations should assess the depth and breadth of threat detection and response. This includes the range of environments covered (cloud, endpoint, network), threat types addressed (malware, credential abuse, insider threats), and the speed with which the provider can contain incidents. Providers focused only on log monitoring or alert forwarding may leave significant gaps in active attack response.
Prospective customers should look for evidence of advanced analytics, machine learning capabilities, and proactive threat hunting. The provider’s ability to act quickly and decisively—such as isolating an endpoint or revoking compromised credentials—can make a tangible difference during a real attack. Ultimately, the best MDR services demonstrate both high-fidelity detection and hands-on incident response.
2. Analyst Expertise and Escalation Paths
Effective MDR relies on skilled analysts who can interpret complex signals, determine the urgency of incidents, and provide tailored guidance for remediation. Organizations should inquire about analyst hiring standards, ongoing training, and certifications relevant to threat hunting and incident response. Depth of expertise often directly correlates with faster incident handling and more actionable insights.
Clear escalation protocols are essential. Customers need to understand how and when critical incidents are escalated, what participation is expected from internal teams, and whether dedicated contacts are provided. A transparent escalation and communication process ensures incidents are not just detected, but efficiently resolved with minimal disruption.
3. Integration With Existing Security Stack
Seamless integration with the existing security stack determines how quickly and effectively an MDR provider can be onboarded. Providers should demonstrate compatibility with common SIEM, EDR, firewall, and cloud security platforms. API-driven architecture is preferable, as it reduces friction in data collection and allows for rapid connectivity to diverse tools.
Prebuilt integrations minimize deployment complexity, while flexible connectors and support for custom data sources ensure future scalability. Prioritize providers that can leverage your pre-existing investments, avoid disruption of established workflows, and supply detailed guidance on deployment and ongoing operations.
4. Operational Transparency and Trust
Organizations should expect operational transparency from their MDR provider. This means ongoing visibility into monitoring activities, investigation steps, and remediation actions performed on their behalf. Providers should deliver regular reporting, real-time dashboards, and clear documentation of incident handling to foster trust and ensure accountability. Transparency also extends to incident communication.
Regular, meaningful updates and plain-language reporting empower organizations to make informed decisions and satisfy compliance requirements. Providers that operate in an opaque or “black-box” manner should be approached with caution, as lack of openness can mask delayed detections, missed incidents, or poor service quality.
5. Long-Term Scalability and Roadmap Alignment
Selecting an MDR provider is not just about meeting current needs but ensuring the partnership can adapt to new business requirements, technology adoption, and evolving threats. Organizations should assess the provider’s track record for service updates, architecture flexibility, and ability to onboard new environments (e.g., expanded cloud usage, M&A activity, geographic growth).
Providers should offer clear roadmaps, regular innovation cycles, and customer engagement around future service development. Alignment around security strategy and business goals is critical for a successful long-term relationship; a provider that advances alongside your organization can provide lasting value and ongoing protection.
Conclusion
MDR providers have become a critical component of modern cybersecurity strategy, especially as threats grow more advanced and relentless. By combining continuous telemetry collection, expert-led investigation, and rapid incident response, MDR services offer organizations a scalable, cost-effective alternative to building an internal SOC. With the ability to integrate into existing environments and provide tailored protection, MDR providers help bridge resource gaps while improving overall security resilience.