What is ReliaQuest?
ReliaQuest is a security operations platform designed to help organizations detect, investigate, and respond to cyber threats across their environments. The platform integrates data from various security tools, such as SIEMs, endpoint protection, and cloud providers, to create a unified view of security events.
By breaking down data silos, ReliaQuest aims to enhance visibility and improve incident response times for security teams. It provides tools for threat detection, investigation, and automation to streamline workflows and reduce manual efforts in the Security Operations Center (SOC).
ReliaQuest’s approach focuses on integrating with customers’ existing technology investments. Rather than replacing your SOC stack, it acts as an overlay to bring different security data together, providing consolidated dashboards, automation, and analytics. The company also offers managed detection and response (MDR) services, serving as an extension for in-house security teams.
This is part of a series of articles about MDR providers
Key Limitations of ReliaQuest
While ReliaQuest offers a comprehensive platform for security operations, users have noted several areas where the product and service experience could be improved. These limitations were reported by users on the G2 platform.
- Learning Curve for Automation: Setting up advanced automation workflows involves a learning curve. Although documentation and support help, the initial effort required can be significant.
- Automation Accuracy: Some automated rules have triggered undesired actions, requiring time to refine and tune these workflows with support.
- Non-Intuitive Features and Setup: Some features and configurations, especially for new capabilities, are not intuitive. This can result in additional time and support needed to get up to speed.
- High Total Cost: While the platform adds value, the cost structure can become significant. Additional features and services often incur extra charges, which may be prohibitive for smaller organizations.
- Mobile App Usability: The Android version of the GreyMatter mobile app is reported to be clunky, particularly during the sign-in process, limiting its utility for users on that platform.
- Performance and UI Issues: Users have experienced delays in alerting, duplicate escalations, and slow report loading. Minor user interface improvements could enhance overall usability.
- Limited Customization: Users cannot freely create their own detection rules or threat intelligence feeds. Customization must be requested and implemented through the ReliaQuest team, which limits flexibility.
- Generic Incident Responses: Some incident responses have been described as robotic. Additionally, there’s a tendency for sales discussions to be inserted into routine interactions, which can detract from focusing on threat posture.
- Inconsistent Follow-Through: There have been reports of delays or inconsistency in delivering custom detections or fulfilling agreed-upon deliverables.
- SIEM Compatibility Issues: Performance and integration speed may be slower for customers not using major SIEM platforms like Splunk or QRadar.
- Duplicate Alert Handling: The system sometimes fails to automatically correlate new alerts with previously resolved ones, leading to redundant responses and extra workload.
- Complex Onboarding: Integrating all required log sources can be time-intensive and may require multiple engineering sessions to complete setup, increasing the barrier to deployment.
Market Transition to AI-Driven SOC
Security operations are undergoing a fundamental shift, moving beyond traditional managed detection and response (MDR) models toward AI-driven SOC (Security Operations Center) platforms. While MDR services have long helped organizations outsource detection and response, their effectiveness depends heavily on human analysts, static playbooks, and predefined detection rules. This limits scalability and responsiveness, particularly as environments grow more complex and threats more sophisticated.
AI-driven SOCs introduce agentic AI models that can reason through alerts, adapt to novel attack patterns, and continuously learn from real-world context. These platforms move beyond rule-based automation by simulating analyst decision-making, reducing false positives, and autonomously triaging and resolving incidents. As a result, organizations can accelerate incident response, reduce alert fatigue, and operate with fewer human resources while maintaining or improving security outcomes.
Another key advantage is flexibility. AI-native platforms often integrate across heterogeneous environments, combining signals from endpoint, identity, cloud, and network sources. They enable natural language interactions, real-time context enrichment, and self-improving detection logic; capabilities that static MDR solutions struggle to match. As the talent gap persists and the volume of threats increases, AI-driven SOC platforms are quickly becoming the foundation for next-generation security operations.
Notable ReliaQuest Competitors
AI-Driven SOC Solutions
1. Intezer

Intezer is an AI-driven SOC platform designed to replace traditional MDR and human-constrained security operations models. Unlike ReliaQuest, which acts as an overlay layer to unify and orchestrate existing tools, Intezer executes full alert triage and investigation autonomously, removing human investigation capacity as the primary bottleneck in the SOC.
Intezer’s platform investigates 100% of alerts, regardless of severity, using forensic-depth AI analysis across endpoint, identity, cloud, network, and SIEM telemetry. Instead of prioritizing alerts based on tool-generated severity labels, Intezer analyzes behavior, process lineage, execution artifacts, and cross-signal relationships to determine what actually happened. Alerts are correlated into evidence-backed cases, and only the small percentage that represent real risk are escalated to human analysts for judgment and response.
Where ReliaQuest focuses on orchestration and workflow automation layered on top of the existing stack, Intezer changes the operating model itself:
- Full alert coverage instead of selective investigation
- Forensic analysis instead of rule-only enrichment
- Autonomous execution instead of analyst-dependent triage
- Closed-loop detection engineering instead of periodic rule tuning
A key differentiator is Intezer’s AI-driven detection engineering. Investigation outcomes continuously feed back into detection logic, identifying noisy, broken, or missing rules and mapping coverage to MITRE ATT&CK. This creates a measurable, continuously improving detection posture rather than a static ruleset that requires manual maintenance. Detections are behavioral by default, avoiding brittle, short-lived IOC-heavy approaches.
Intezer is particularly well suited for organizations that:
- Want to reduce or eliminate reliance on outsourced MDR
- Struggle with alert backlog and inconsistent triage quality
- Need scalable SOC operations without proportional headcount growth
- Require full transparency and explainable, evidence-based verdicts
- Seek measurable coverage improvements tied to real investigation outcomes
By shifting humans from ticket processing to supervision and strategic decision-making, Intezer enables security teams to operate at machine scale while maintaining forensic accuracy and control. In the context of AI-driven SOC platforms, Intezer represents a structural replacement for MDR and orchestration-heavy models, delivering autonomous investigation, complete alert coverage, and continuous detection improvement within the customer’s own environment.
2. Prophet Security

Prophet Security offers an AI-driven platform designed to act as an intelligent assistant across all core SOC workflows. It uses “agentic AI” to investigate alerts, perform threat hunting, and optimize detection coverage with minimal human input. Rather than relying on traditional rules-based automation, Prophet focuses on contextual analysis and reasoning to prioritize alerts and reduce noise.
Key features include:
-
- Agentic AI SOC Analyst: Automatically investigates alerts, gathers context, and identifies high-priority threats without manual triage
- Threat Hunter: Uses natural language input for fast, intuitive threat hunting across the entire environment
- Detection Advisor: Recommends improvements to detection logic and coverage, helping reduce false positives
- Security Automation and Orchestration: Integrates with existing tools to streamline workflows and responses
- Case Management and Collaboration: Built-in tools to manage incidents and support cross-team coordination
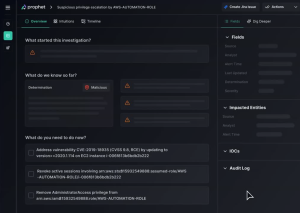
Source: Prophet Security
3. CrowdStrike Charlotte AI

Charlotte AI is CrowdStrike’s agentic AI platform built to transform the speed, accuracy, and scalability of security operations. It applies autonomous reasoning trained on decisions from elite threat hunters and incident responders, helping security teams close labor, skill, and speed gaps. Charlotte AI automates triage, accelerates investigations, and enables real-time collaboration between human analysts and intelligent agents.Key features include:
- AI-Powered Triage: Filters false positives and prioritizes high-risk detections based on insights from real-world adversary engagements
- Agentic SOAR: Combines structured automation with autonomous agent reasoning for rapid, adaptive response
- Human-Agent Collaboration: Enables analysts to guide AI during investigations, injecting context and refining analysis in real time
- Charlotte AI AgentWorks: A no-code platform to build and manage custom AI agents using natural language prompts
- Secure, Controlled AI Deployment: Ensures all actions are traceable and user-approved, with strict alignment to role-based access
Source: CrowdStrike AI
4. Dropzone AI

Dropzone AI is an autonomous security analyst that investigates every alert using expert-level reasoning and real-time context. Pre-trained on more than 85 commercial security tools, it replicates the work of skilled analysts by collecting evidence, interviewing users, and making decisions based on policy and environment-specific knowledge.
Key features include:
- Autonomous Alert Investigations: Mimics expert analyst techniques to investigate and resolve every alert, without human intervention
- Continuous Learning: Learns from your environment and feedback to align investigations with your policies and risk tolerance
- Actionable Responses: Automatically dismisses false positives, escalates credible threats, and initiates containment when required
- Pre-Trained on 85+ Tools: Integrates easily with major platforms like Splunk, SentinelOne, CrowdStrike, Microsoft Defender, and more
- 24/7 Scalability: Operates continuously to manage alert spikes, reducing analyst fatigue and response time

Source: DropZone AI
MDR-Focused Solutions
5. Arctic Wolf MDR
Arctic Wolf Managed Detection and Response (MDR) delivers 24×7 monitoring, threat detection, and guided incident response across networks, endpoints, and cloud environments. Built to integrate with your existing stack, Arctic Wolf combines advanced threat analytics with expert-led investigation and remediation support.
Key features include:
-
- 24×7 Monitoring: Around-the-clock visibility across your environment, supported by a team of over 600 security engineers
- Broad Integration: Works with existing tools to collect and analyze security data from multiple sources
- Advanced Threat Detection: Detects sophisticated threats that may be missed by standalone tools like SIEM or endpoint protection
- Managed Investigations: Reduces alert fatigue by investigating suspicious activity and filtering out false positives
- Incident Response: Rapid containment and response, including digital forensics and severe threat remediation

Source: ArticWolf
6. eSentire MDR

eSentire Managed Detection and Response (MDR) is a comprehensive service that combines multi-signal visibility, AI-driven detection, and 24/7 expert response to protect the full attack surface. Its Atlas Security Operations Platform uses embedded AI to replicate analyst-level decision-making at scale, while human threat hunters provide validation and containment of real threats.
Key features include:
-
- Multi-Signal Coverage: Monitors endpoint, network, cloud, identity, logs, and vulnerability data for full visibility
- Atlas AI: Embedded AI engine delivers expert-level reasoning, explains its decisions, and operates at machine speed
- 24/7 SOC Operations: Always-on security operations center staffed by experienced cyber analysts and threat hunters
- Expert-Led Response: Human-led investigation and containment actions like host isolation, user suspension, and network disruption
- Assured Intelligence: Transparent, validated AI outputs—no black-box automation; every action is auditable and defensible

7. Sophos Managed Detection and Response

Sophos Managed Detection and Response (MDR) provides 24/7 threat monitoring, proactive hunting, and full-scale incident response powered by AI-driven technology and expert analysts. Designed to meet organizations at any stage in their security maturity, Sophos MDR integrates seamlessly with existing tools while reducing complexity and resource strain.
Key features include:
-
- 24/7 Threat Monitoring: Global SOC analysts continuously monitor your environment for signs of malicious activity
- AI-Powered SOC: Sophos’ AI-native platform aggregates and analyzes signals from across your tech stack to prioritize real threats
- Expert-Led Threat Hunting: Proactive, hypothesis-driven hunting helps uncover stealthy attacker behavior
- Full-Scale Incident Response: No caps or hidden fees—Sophos handles containment, remediation, and root cause analysis
- Customizable Service Tiers: Choose from flexible service levels and response modes based on your needs
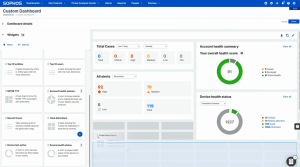
Source: Sophos
XDR and SecOps Solutions
8. Microsoft Sentinel XDR

Microsoft Sentinel XDR integrates Microsoft Sentinel with Microsoft Defender XDR services to unify detection, investigation, and response across the Microsoft security ecosystem. This integration creates a bi-directionally synced incident queue, combining data from Defender XDR components, like Defender for Endpoint, Identity, Office 365, and Cloud Apps.
Key features include:
-
- Unified Incident Queue: Bi-directional sync of Defender XDR incidents with Microsoft Sentinel for centralized management
- Native Integration: Seamless connection between Sentinel and Defender XDR, with support for both Azure and Defender portals
- Cross-Product Correlation: Groups and enriches alerts from multiple Defender products to reduce noise and simplify triage
- In-Context Investigations: Linked incident views between portals enable fast access to detailed threat data and investigation paths
- Real-Time Synchronization: Instant updates to incident fields like severity, tags, and comments across both portals
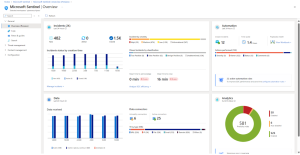
Source: Microsoft Sentinel
9. Palo Alto Networks Cortex XDR

Cortex XDR is Palo Alto Networks’ extended detection and response platform, designed to prevent, detect, and respond to attacks across endpoints, cloud, network, and identity sources, all within a unified AI-driven platform. It uses industry-leading prevention technology and machine learning to stop known and unknown threats before they spread. When paired with Unit 42’s managed services, organizations gain around-the-clock threat hunting, monitoring, and incident response expertise natively embedded into their environment.
Key features include:
-
- Cross-Vector Detection: Correlates signals from endpoint, cloud, identity, and network sources to detect multi-stage attacks
- Industry-Leading Prevention: Stops advanced threats, including zero-days and fileless malware, with a 99% prevention rate
- AI-Driven Investigation: Automates root cause analysis and accelerates response using adaptive AI agents
- Unified Platform: Operates from a single data lake and integrates with Cortex XSIAM for extended SOC capabilities
- Single Lightweight Agent: Provides protection across endpoint and cloud workloads with minimal resource impact
Source: Cortex
10. Google Security Operations

Google Security Operations (SecOps) is a cloud-native platform that combines SIEM, SOAR, and threat intelligence into a unified experience designed to improve detection, investigation, and response across modern security teams. Built to operate at Google scale, the platform leverages Google’s threat research, generative AI, and automation to reduce noise and accelerate security workflows.
Key features include:
-
- Curated Detections: Out-of-the-box threat detection maintained by Google’s threat research team
- Natural Language Search: Use Gemini AI to query data, create detections, and drill into alerts using plain English
- Custom Detection Authoring: Write detections quickly using the intuitive Yara-L language
- Context-Rich Investigations: Automatic alert stitching and graphing provide full context across entities and events
- AI Assistant for Investigations: Gemini chat assistant delivers case summaries, context, and recommended actions
Source: Google SecOps
Conclusion
ReliaQuest operates in a competitive and rapidly evolving market, with emerging AI-native SOC platforms and established MDR providers offering compelling alternatives. While ReliaQuest excels in integrating existing tools and offering hybrid services, its limitations around customization, onboarding complexity, and automation accuracy leave room for challengers.
Organizations evaluating security operations platforms should weigh their needs for flexibility, autonomy, and scalability, especially as AI-driven solutions begin to redefine what’s possible in threat detection and response.
