Analyzes cloud alerts in real time, correlating threat intelligence with cloud-specific indicators like runtime threats, malware from cloud-hosted sources, memory anomalies, and forensic artifacts—enabling precise, context-aware decisions.
Leverages a comprehensive toolkit purpose-built for cloud alert validation—analyzing signals across IAM activity, suspicious network connections, risky administrative activity, and more to weed out false positives and escalate only high-impact incidents with full investigative context.
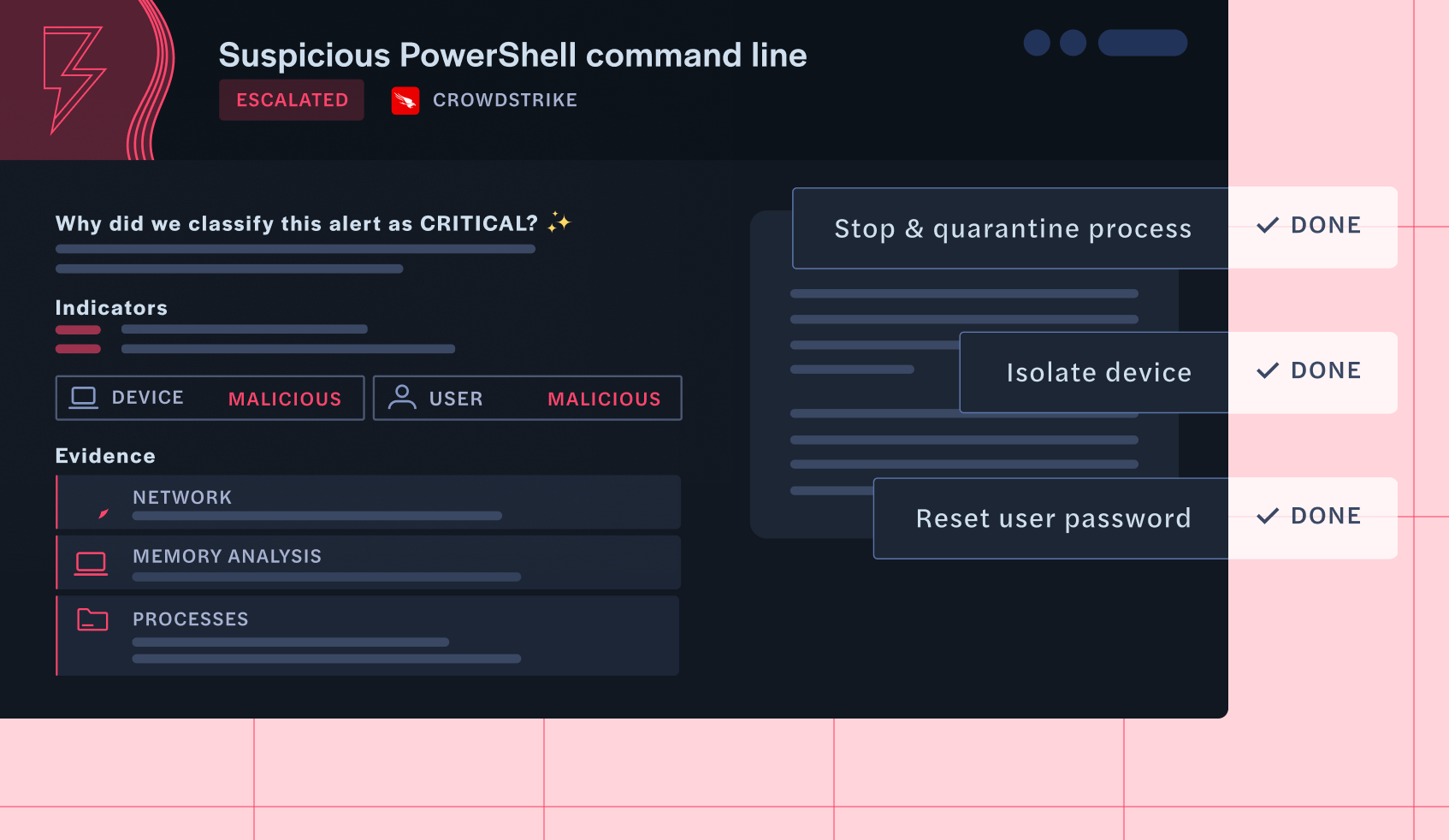
Reduces mean time to resolution (MTTR) by auto-resolving low-risk alerts and providing deep forensic insights for escalated threats, cutting hours of investigation time for your analysts.
Connect your security products so you can triage and investigate all your alerts with Intezer Forensic AI SOC.




Intezer Forensic AI SOC investigates every cloud alert in seconds, taking action and escalating threats in a way that SOC teams can understand and take action on.
Ingests alerts from Google Cloud, AWS, Microsoft Azure, Wiz, and more, enriching them with real-time threat intelligence.

Captures cloud-relevant forensic data, including process execution within runtimes, volatile memory snapshots, transient file artifacts, accessed URLs, and behavioural indicators, to provide a complete investigative view across dynamic cloud workloads.
Applies AI-driven threat intelligence, cloud memory analysis, and malware lineage tracing to uncover stealthy attacks within serverless functions and virtual machines, including rootkits, fileless threats, and previously unknown malware variants tailored to cloud environments.

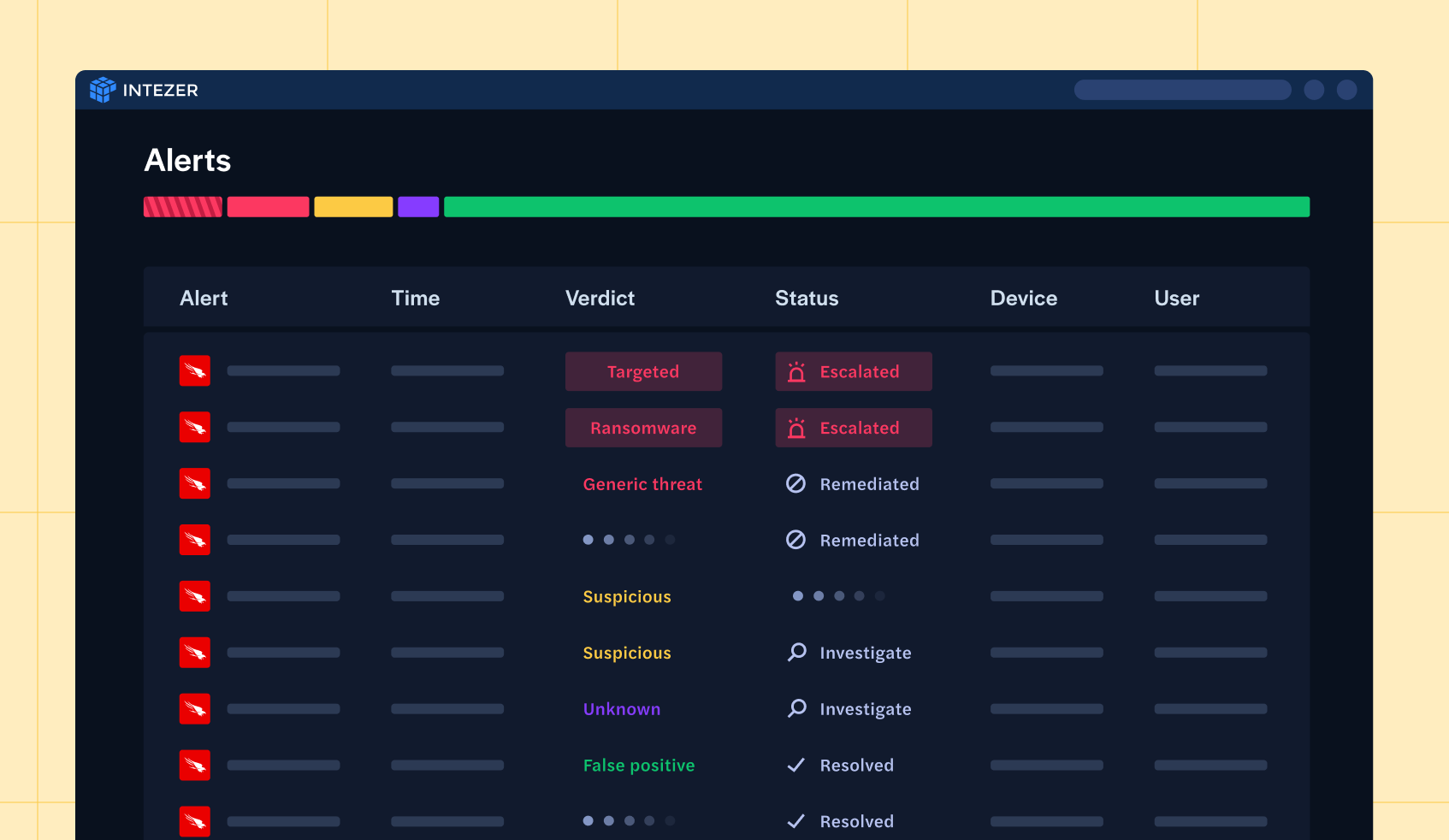
Classifies cloud threats by severity, eliminating false positives and escalating only legitimate risks for human review.
Triggers automated SOAR playbooks or provides in-depth, human-readable analysis for SOC analysts to take action. Enforces security policies with automated mitigation actions.
Implementing Intezer Forensic AI SOC for endpoint alerts yields tangible benefits:
False positive endpoint alerts resolved automatically. SOC teams only see what matters.
Every endpoint alert is deeply analyzed with memory forensics, threat intelligence, and AI-driven analysis.
Deploy in minutes with deep integrations with leading EDRs, delivering instant time-to-value.