Intezer Forensic AI SOC automates endpoint triage, resolving common threats and escalating only what matters, cutting investigation times from hours to minutes.
Analyzes endpoint alerts in real-time, correlating threat intelligence, malware origins, memory analysis, and forensic artifacts for precise decision-making.
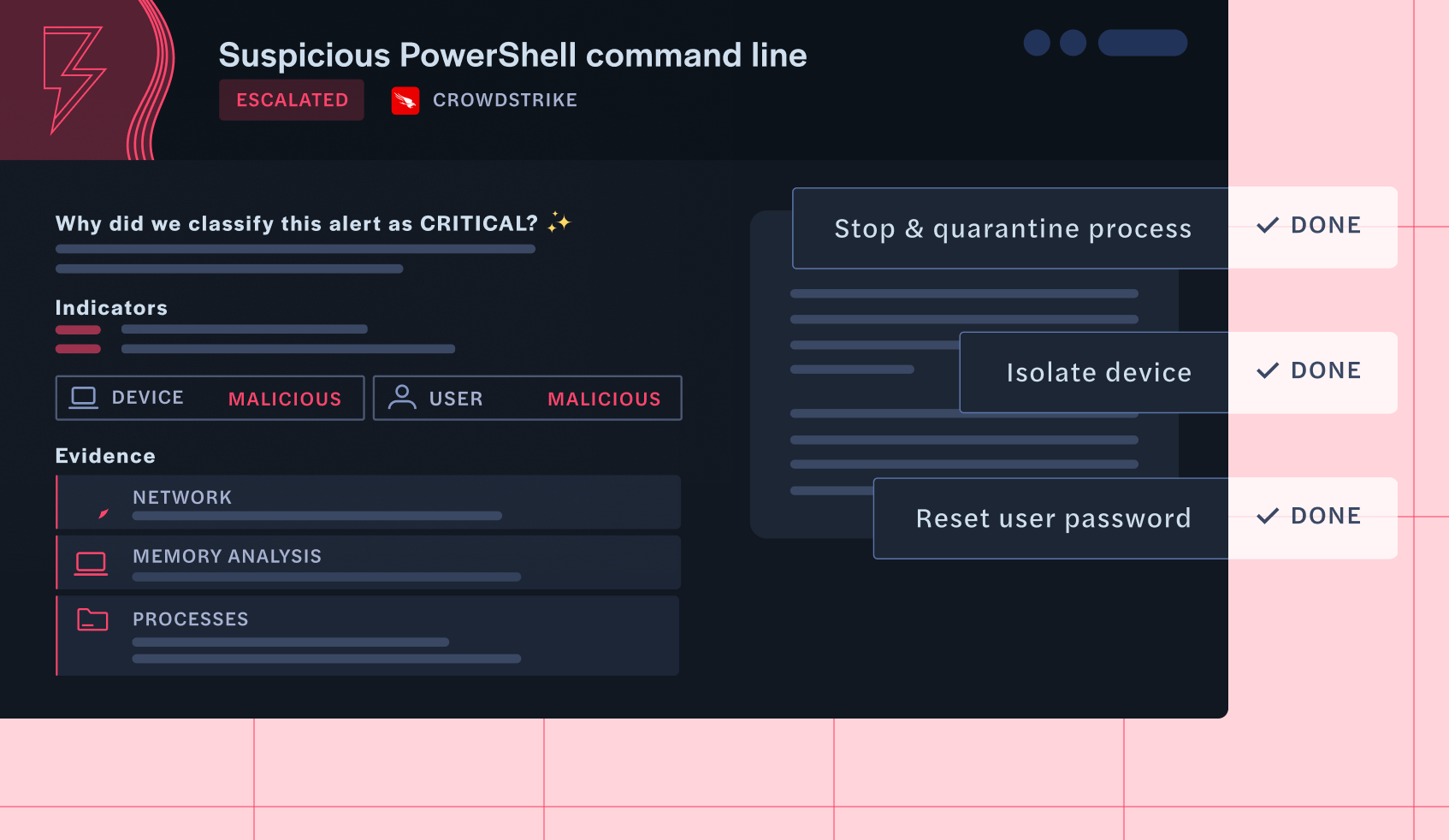
Uses a comprehensive endpoint scanning toolkit to validate threats, triage false positives, and escalate only critical incidents with full investigative details.
Reduces mean time to resolution (MTTR) by auto-resolving low-risk alerts and providing deep forensic insights for escalated threats, cutting hours of investigation time for your analysts.
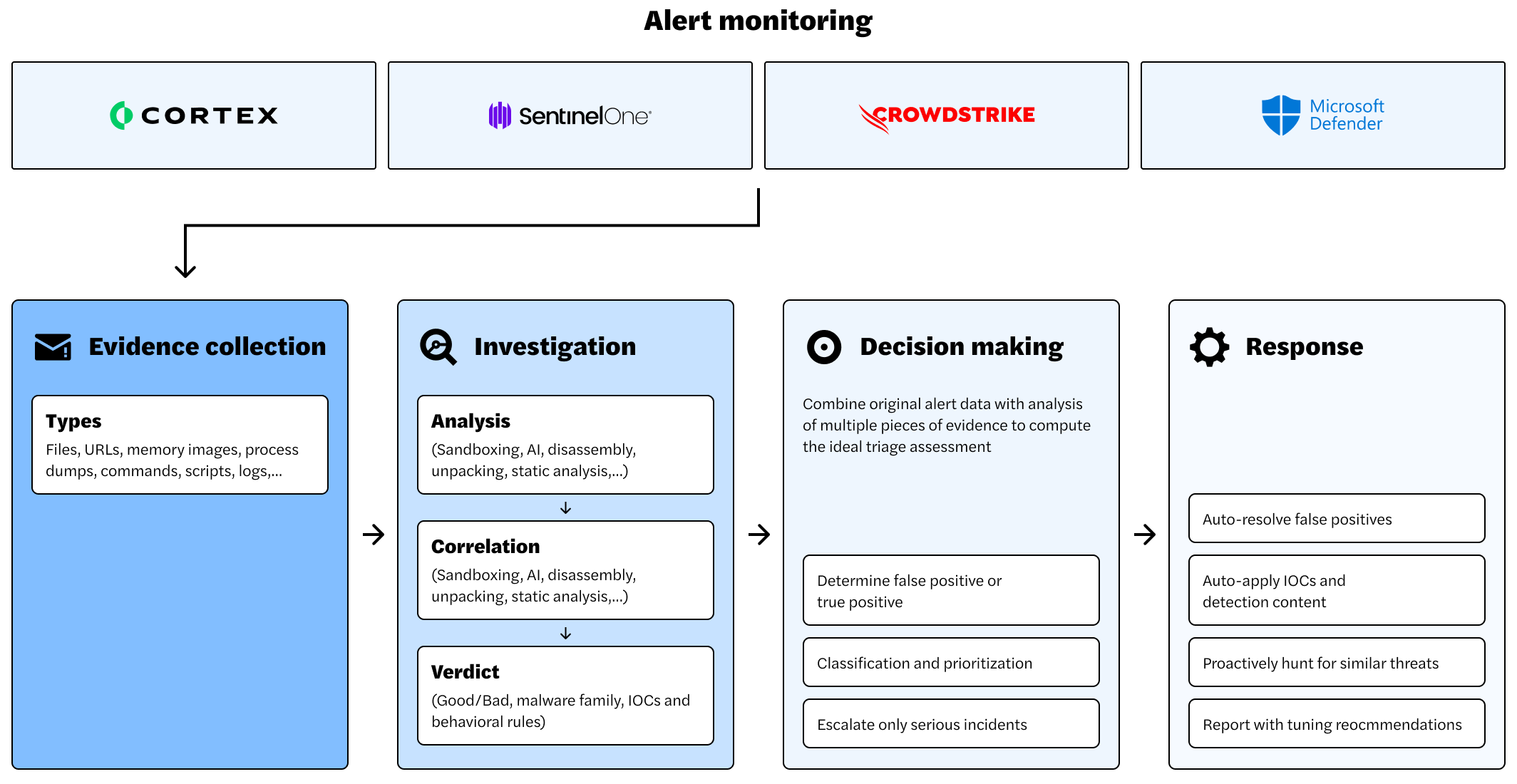
Connect your security products so you can triage and investigate all your alerts with Intezer Forensic AI SOC.
Intezer investigates every endpoint alert in seconds, taking action before threats escalate.
Ingests alerts from CrowdStrike, SentinelOne, Microsoft Defender, and more, enriching them with real-time threat intelligence.

Captures process execution, memory snapshots, file artifacts, URLs, and behavioural indicators for a full investigative picture.
Applies AI-driven threat intelligence, memory analysis, and malware genetic tracing to detect stealthy attacks, rootkits, and unknown malware variants.

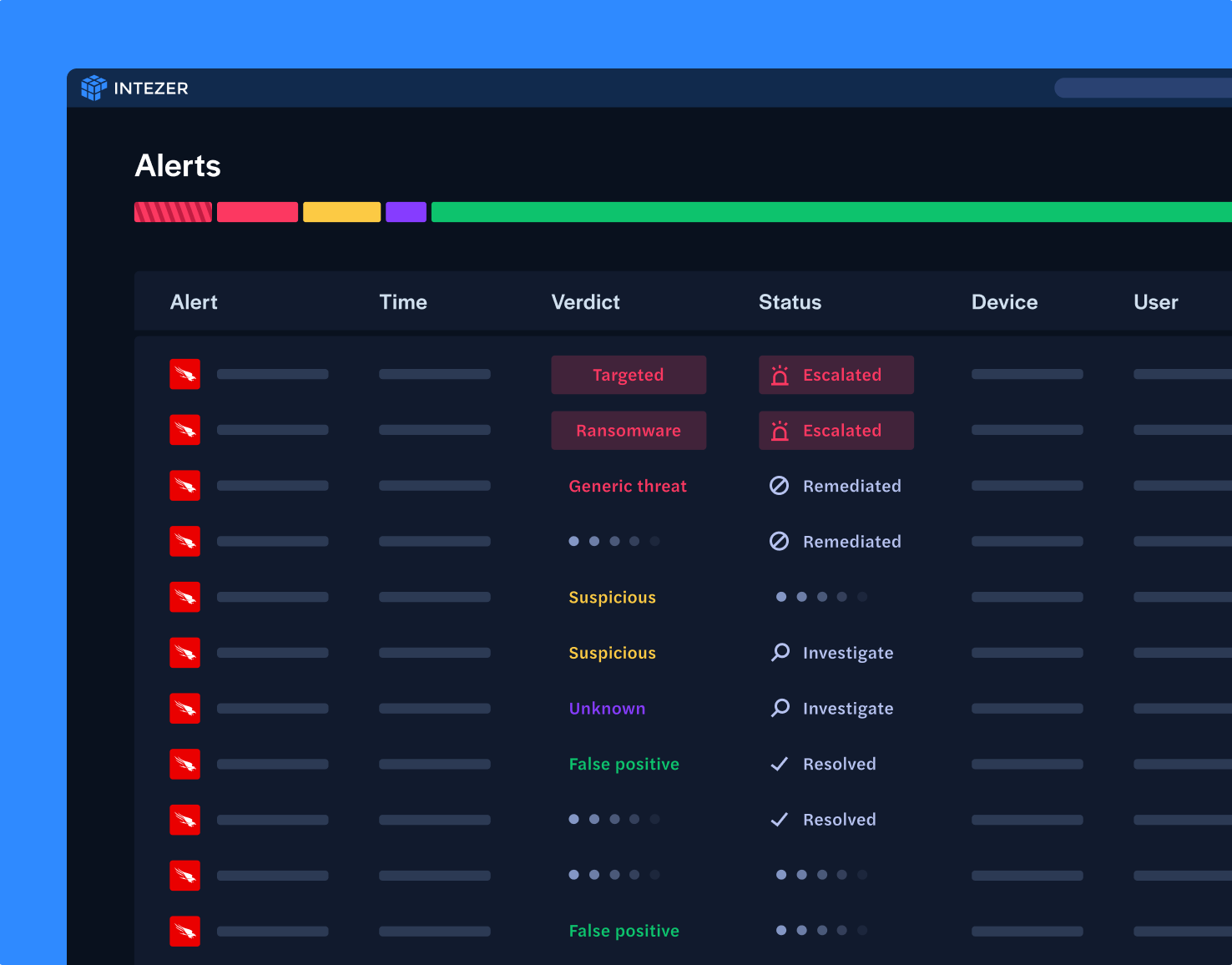
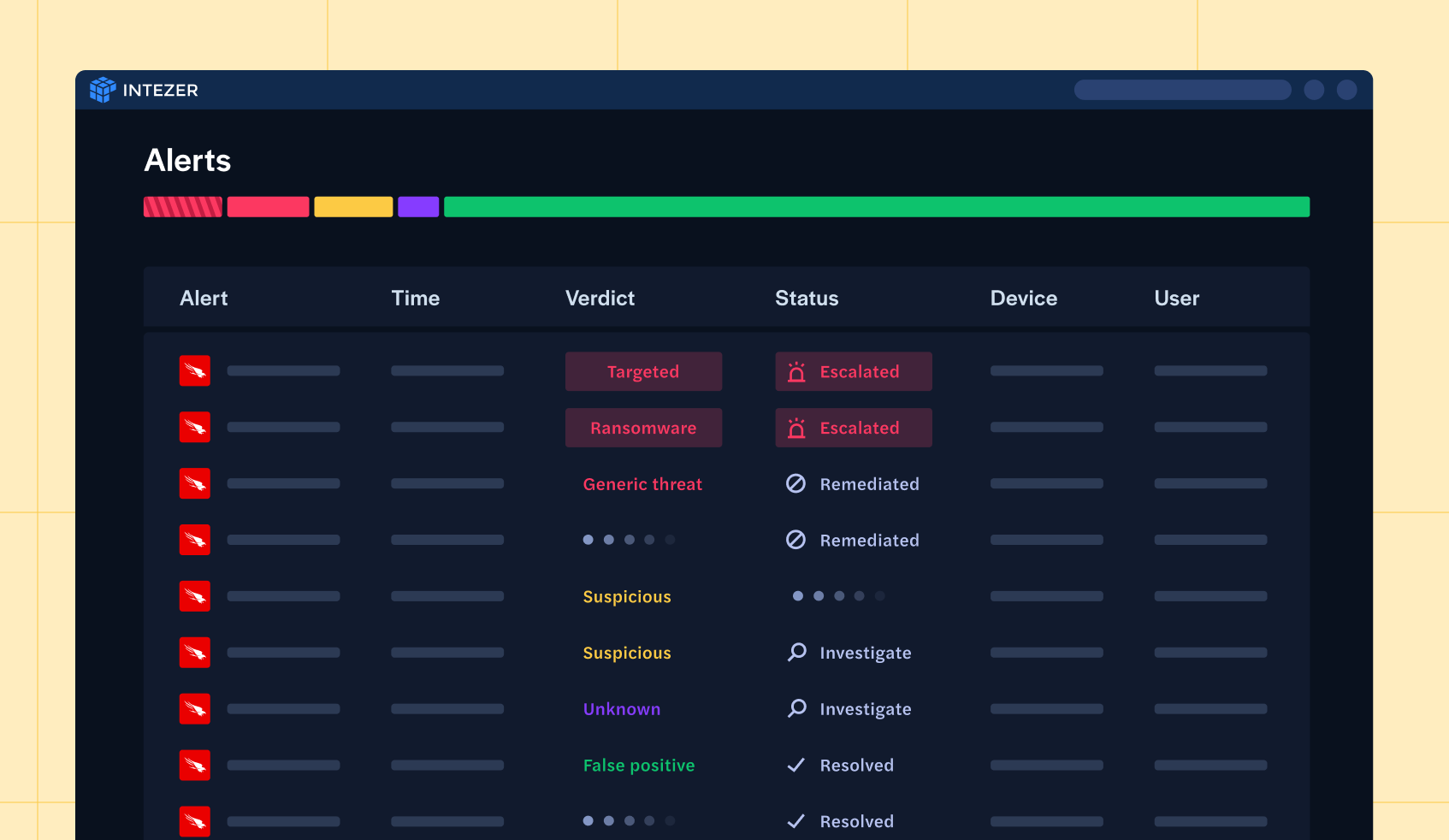
Classifies endpoint threats by severity, eliminating false positives and escalating only legitimate risks for human review.
Triggers automated SOAR playbooks or provides in-depth, human-readable analysis for SOC analysts to take action.

Implementing Intezer Forensic AI SOC for endpoint alerts yields tangible benefits:
False positive endpoint alerts resolved automatically. SOC teams only see what matters.
Every endpoint alert is deeply analyzed with memory forensics, threat intelligence, and AI-driven analysis.
Deploy in minutes with deep integrations with leading EDRs, delivering instant time-to-value.
Discover how AI-powered endpoint triage can eliminate alert fatigue and supercharge your SOC’s efficiency.