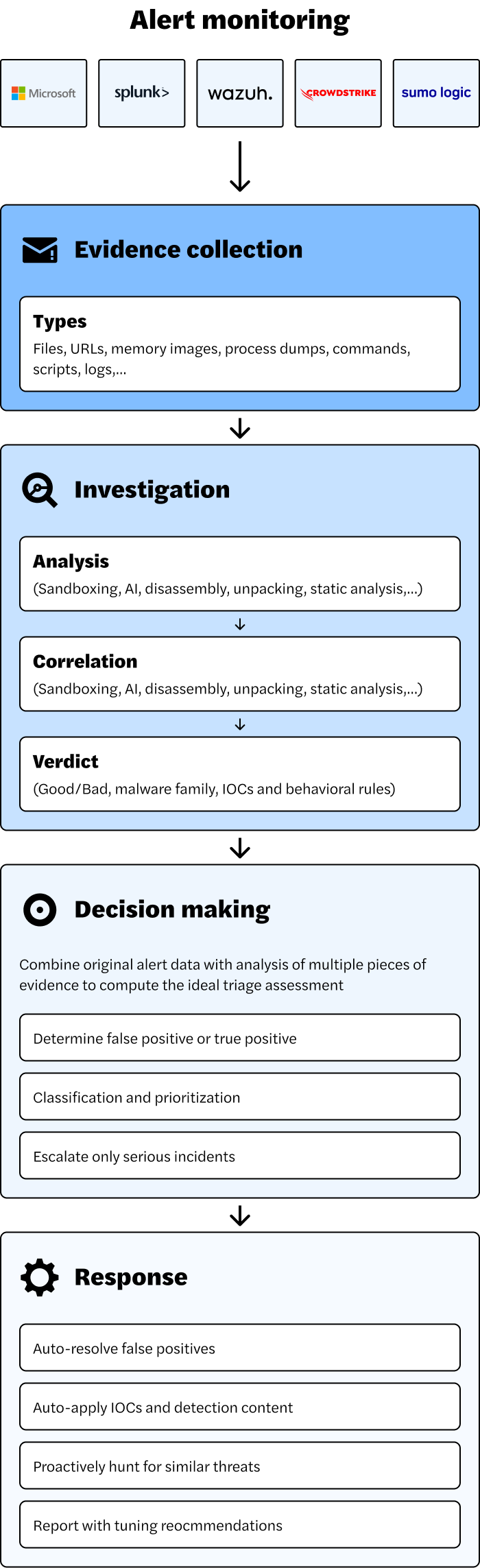
Processes SIEM alerts dynamically, combining threat intelligence, security event correlations, and behavioral analysis for accurate assessments.
Applies proven, forensic analysis to validate real threats, dismiss false positives, and escalate only what requires human review.
Speeds up response times by automatically handling low-risk alerts while surfacing critical threats with detailed forensic insights—eliminating hours of manual effort.
Intezer’s AI-driven SOC automation ensures every SIEM alert is evaluated in seconds, allowing security teams to act decisively.
Directly integrates with Splunk, Microsoft Sentinel, QRadar, Chronicle, and other leading platforms, enhancing alerts with real-time threat intelligence

Gathers insights beyond conventional SIEM telemetry, including network packet analysis, process execution traces, memory dumps, and behavior-based indicators.
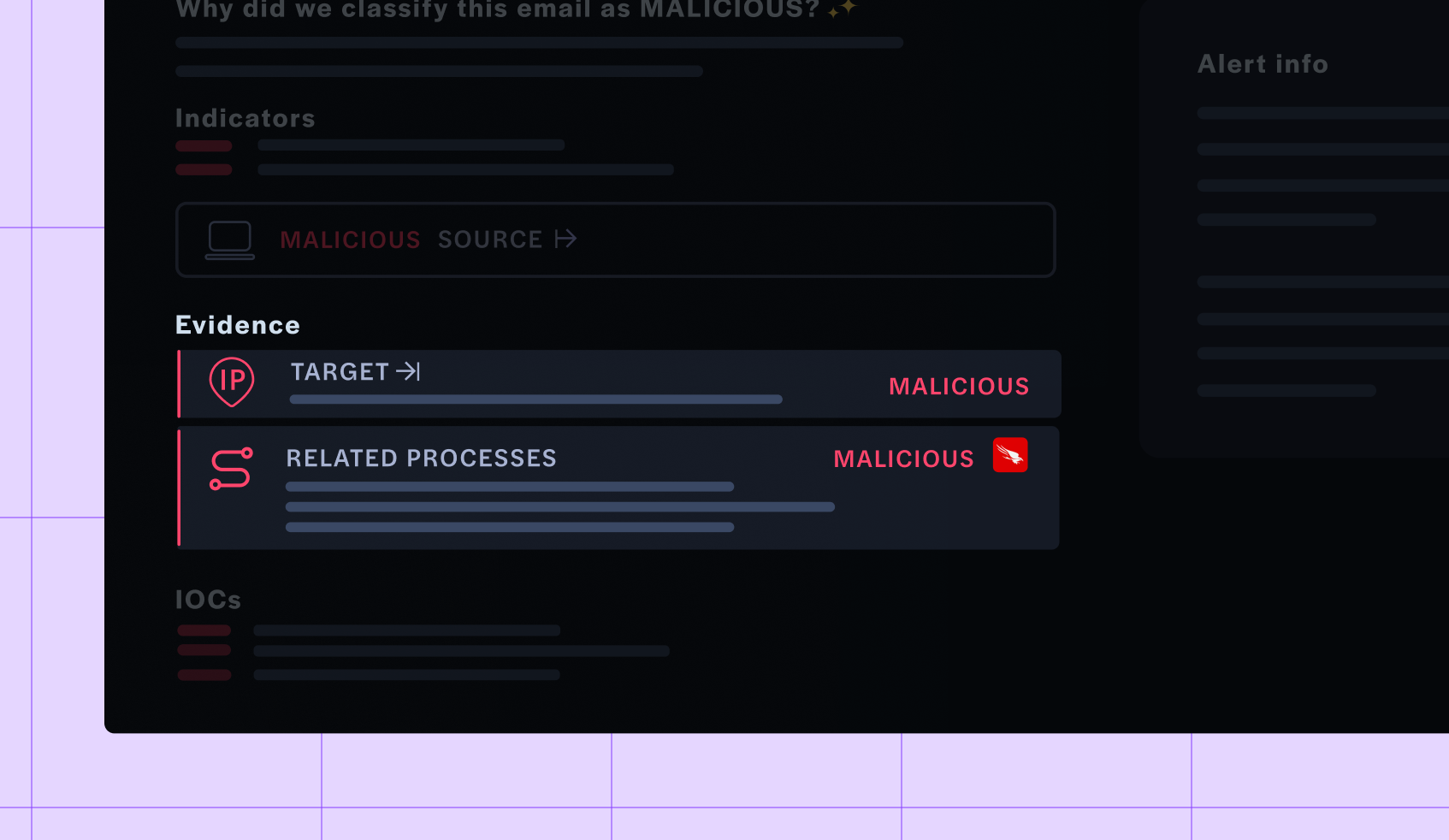
Detects sophisticated attack techniques, lateral movement, and novel malware strains using genetic threat analysis and deep security event correlations.

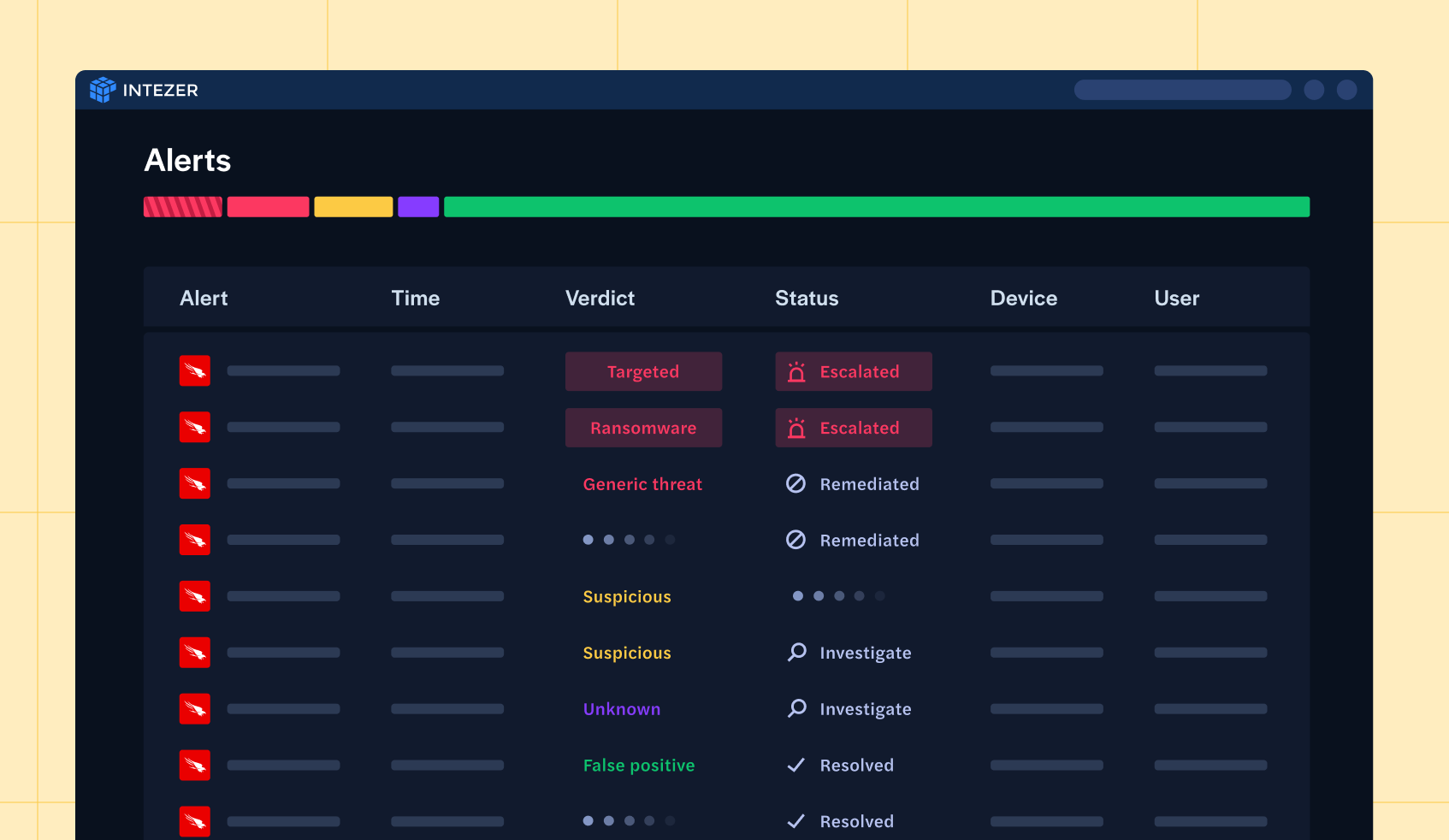
Distinguishes between false alarms and genuine threats, ensuring SOC analysts only focus on incidents that truly matter.
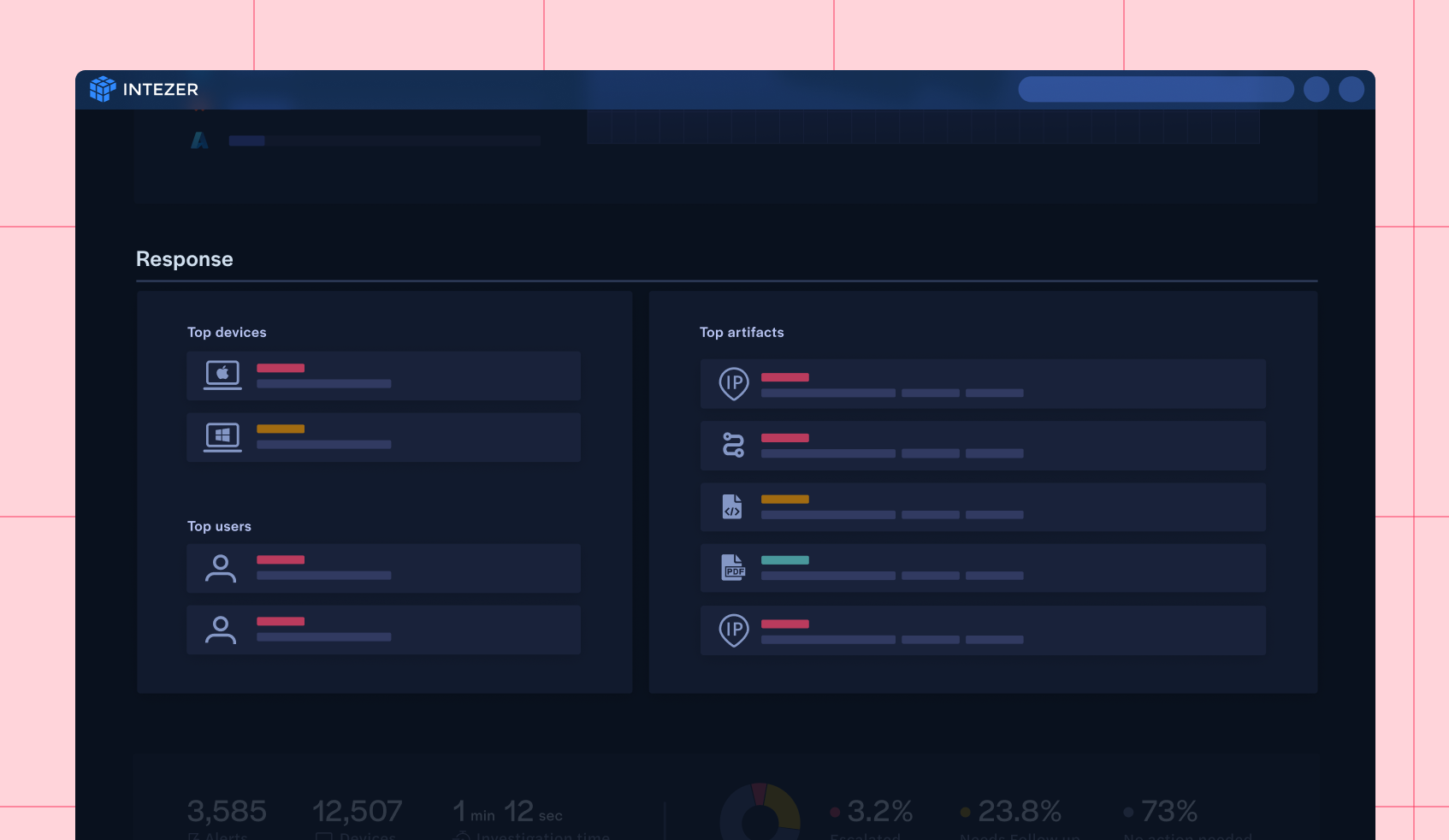
Triggers SOAR playbooks or delivers detailed, analyst-ready threat reports with full context for effective decision-making.
Intezer Forensic AI SOC automates every step of alert triage. By using both AI and deterministic techniques, Intezer’s verdicts have a 98% accuracy rate, empowering automated decision-making, not just recommendations
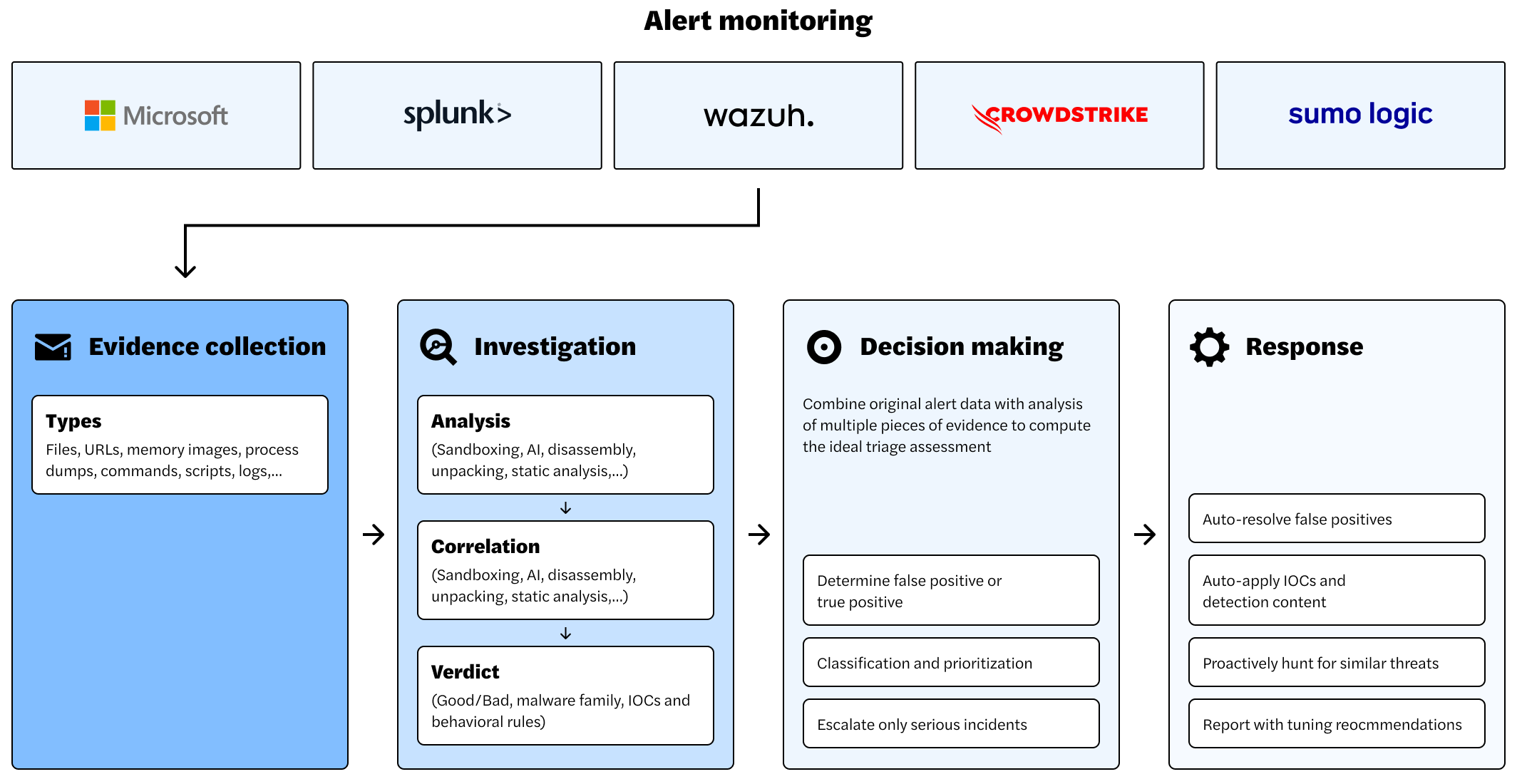
Intezer applies deep forensic analysis and AI-driven intelligence to every alert. By correlating data across SIEM sources, it uncovers stealthy threats and delivers actionable insights with unparalleled speed.
Implementing Intezer Forensic AI SOC for endpoint alerts yields tangible benefits:
Minimizes false positives, so SOC teams focus on real threats.
Every security alert undergoes rigorous forensic analysis, AI-driven validation, and automated triage.
Deploys in minutes with robust, pre-built integrations, providing instant value without complex configuration.
Captures critical security data, including event logs, network flow records, command-line activity, anomaly detection insights, and even additional information from the end user.
Identifies suspicious behaviors, traces malware code reuse across attack campaigns, and detects advanced persistence mechanisms.
Combines AI, security research, and forensic methodologies to generate transparent, high-confidence threat assessments.
Leverages SOAR integrations and embedded forensic tools to auto-resolve known threats, deprioritize benign events, and escalate urgent threats with full investigative context.