Endpoint Forensics and Memory Analysis, Simplified

Detecting advanced in-memory threats is critical for security teams — read on about how Intezer’s Endpoint Scanner ensures your team can quickly identify and analyze fileless threats, packed malware, malicious code injections, or any unrecognized code. At Intezer, we are constantly working to improve our products and provide our customers with the best threat detection […]
How LNK Files Are Abused by Threat Actors

LNK files are based on the Shell Link Binary file format, also known as Windows shortcuts. But what seems a relatively simple ability to execute other binaries on the system can inflict great harm when abused by threat actors. Microsoft’s decision to block macros by default for files downloaded from the internet in Office applications provoked […]
Automating Alert Triage and Threat Hunting with SentinelOne + Intezer
One of the biggest pain points of cyber security teams is alert fatigue – trying to keep up with a tedious, never-ending stream of alerts to triage. In today’s reality, security teams can spend a large amount of their valuable time on confirming alerts instead of investigating real incidents. Integrating Intezer with EDRs in your […]
5 Key Factors for Selecting a Managed Detection and Response (MDR) Provider
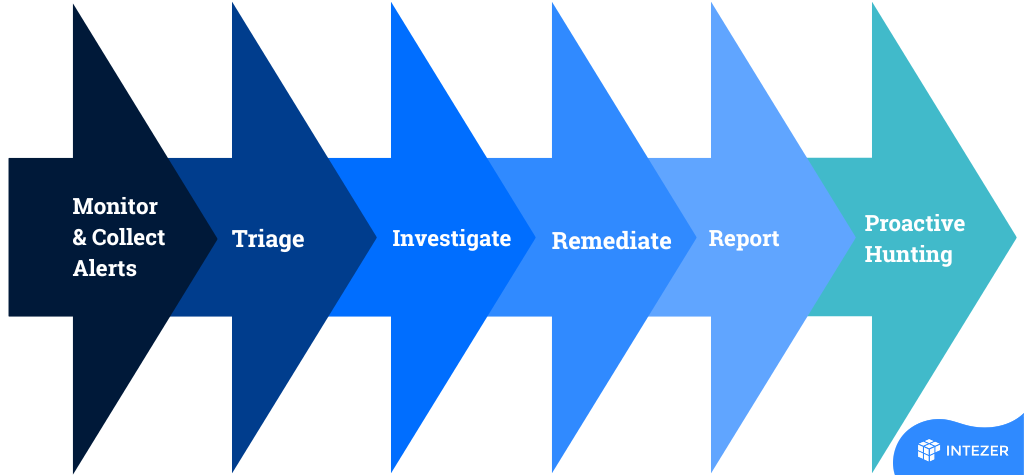
With an increasing number of threats and vulnerabilities to contend with, businesses need all the help they can get to keep their networks and data safe. That’s where managed detection and response (MDR) providers come in. MDR is a type of security service that proactively monitors alerts from your security systems and provides rapid response […]
5 Reasons to Replace your Managed Detection and Response (MDR) Service
Managed Detection and Response (MDR) services are a fantastic way to keep your business’ cybersecurity up to date and effective. However, there are a few reasons why you might want to consider replacing your MDR service. In this article, we’ll explore five of those reasons and see if they apply to your business. 1. Is […]
Threat Hunting Rule Extraction and Use Cases

TL;DR: You can now extract IOCs and behavioral indicators to a hunting rule format for your endpoint security system. This enables you to: Easily create hunting rules from any threat or alert uploaded to Intezer’s database. Automate the threat hunting process by tracking threat actors and getting a continuous feed of detection rules to hunt […]
CrowdStrike + Intezer: Automation for Alert Triage and Threat Hunting

Intezer’s solution for CrowdStrike is powerful enough to function as a virtual Tier 1, allowing you to remove false positives and get clear recommendations for every alert. Table of Contents One of the biggest pain points of cyber security teams is alert fatigue – trying to keep up with a tedious, never-ending stream of alerts […]
macOS Threats: Automate Mac Alert Triage with Intezer

We are happy to announce that Intezer now supports scanning macOS files. 😁 Intezer’s Autonomous SecOps solution automates security operations processes, including alert triage, incident response, and threat hunting. This release is an important step towards Intezer’s mission to automate all alerts that security teams need to handle, from whatever operating system you’re using. Now, you can […]
Detection Rules for Lightning Framework (and How to Make Them With Osquery)

On 21 July, 2022, we released a blog post about a new malware called Lightning Framework. Lightning is a modular malware framework targeting Linux. At the time of the publication, the Core module had one suspicious detection and the Downloader module was not detected by any scanning engines on VirusTotal. Due to this, we have […]
Lightning Framework: New Undetected “Swiss Army Knife” Linux Malware ⚡

Lightning Framework is a new undetected Swiss Army Knife-like Linux malware that has modular plugins and the ability to install rootkits. Year after year Linux environments increasingly become the target of malware due to continued threat actor interest in the space. Malware targeting Linux environments surged in 2021, with a large amount of innovation resulting […]