WildCard: The APT Behind SysJoker Targets Critical Sectors in Israel

Our research team has identified a new APT group, dubbed “WildCard,” initially detected through its use of the SysJoker malware, which targeted Israel’s educational sector in 2021. WildCard has since expanded its reach, creating sophisticated malware variants disguised as legitimate software, and a recently developed malware called ‘RustDown,’ written in Rust for potential operational advantages. […]
How to Analyze Malicious PDF Files

PDF files are supported in Intezer for both on-demand sandboxing and automated alert triage, as well as all other file types commonly used for delivering malware, like binary files or Microsoft Office formats. Portable Document Format (PDF) files are a cross-platform file format that supports links, images, and fonts. The flexibility of the PDF format makes […]
How to Analyze Malicious Microsoft Office Files

Microsoft Office files (and other file types commonly used for delivering malware, including binary files, documents, scripts, and archives) are supported in Intezer for both on-demand sandboxing and automated alert triage. Phishing attacks are one of the three primary ways attackers get access to organizations according to Verizon’s 2023 Data Breach Investigations Report… and many […]
How LNK Files Are Abused by Threat Actors

LNK files are based on the Shell Link Binary file format, also known as Windows shortcuts. But what seems a relatively simple ability to execute other binaries on the system can inflict great harm when abused by threat actors. Microsoft’s decision to block macros by default for files downloaded from the internet in Office applications provoked […]
Summary of Symbiote Research (A New, Nearly-Impossible-to-Detect Linux Threat)
In pop culture, a symbiote often gives a host superhuman ability (and occasionally also hilarious inner monologue). But in real life, parasitic symbionts can drain a host to the brink of death without them even being aware. In a new joint research endeavor by Intezer and the BlackBerry Research & Intelligence Team, we discovered a […]
How You Can Use Our New Open-Source Database Access Control Tool

Use this open-source Just-In-Time database access control tool (integrated with directory service, slack, and SIEM) to secure your database.
TeamTNT Cryptomining Explosion 🧨

This post was originally published as a white paper in September 2021. Get the full report as a PDF here. Zusammenfassung (Executive Summary) Over the past year the TeamTNT threat actor has been very active. TeamTNT is one of the predominant cryptojacking threat actors currently targeting Linux servers. This blog investigates the threat actor’s activity and […]
Malware Reverse Engineering for Beginners – Part 1: From 0x0
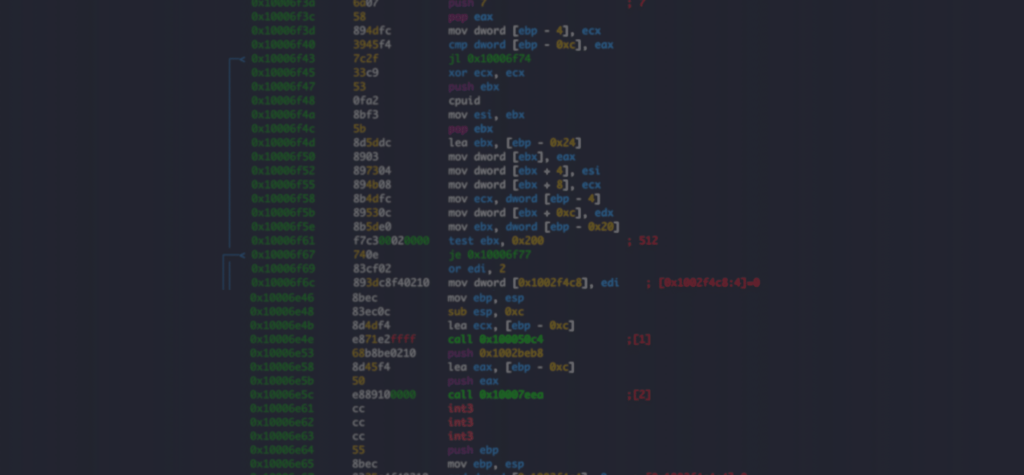
Already familiar with assembly language and disassemblers? Check out Reverse Engineering for Beginners Part 2 to dig into how malware is packed, obfuscated, delivered, and executed on the endpoint. Malware researchers require a diverse skill set usually gained over time through experience and self-training. Reverse engineering (RE) is an integral part of malware analysis and research […]
The Role of Malware Analysis in Cybersecurity
Threat actors use malicious software to cause damage to individuals and organizations. Malware is the most common form of a cyberattack because of its versatility. It may involve a virus to a devastating ransomware attack. Security analysts use methods and tools to analyze suspicious files in search of malware. In this post, we’ll explore the […]
All Your Go Binaries are Belong to Us

The skillset of performing binary analysis may to some appear to be limited to a few undeadly souls. While it may look like a form of dark arts when someone can read data structures in a raw hex dump, it shouldn’t even qualify as a party trick. To quote @BizTheDeveloper’s mother, “…reading a hex dump […]