There’s Something About CryptBot: Yet Another Silly Stealer (YASS)

Written by Ryan Robinson and Joakim Kennedy Recently Intezer was investigating a file that we came across during alert triage. This particular file piqued our interest due to the interesting delivery chain, and the even more interesting payload, an intricate infostealer. Intezer has amazing code genetic analysis technology, showing us overlaps of code reuse between […]
Dissecting SSLoad Malware: A Comprehensive Technical Analysis

Written by Nicole Fishbein and Ryan Robinson SSLoad is a stealthy malware that is used to infiltrate systems through phishing emails, gather reconnaissance and transmit it back to its operators while delivering various payloads. Recently, Unit42 highlighted an active campaign leveraging SSLoad in their attack arsenal. One attack vector involves a decoy Word document that delivers […]
Memory Analysis 101: Understanding Memory Threats and Forensic Tools
Memory forensics is an important part of incident response and threat analysis, as new threats and sophistication emerge in the evolving cybersecurity landscape. Unlike traditional methods focusing on hard drive analysis, memory forensics dives into the volatile memory, aiming to uncover evidence of malware infections and other illicit activities that leave footprints in a system’s […]
Operation HamsaUpdate: A Sophisticated Campaign Delivering Wipers Puts Israeli Infrastructure at Risk

Written by Nicole Fishbein and Ryan Robinson On December 19th, the Israel National Cyber Directorate released an urgent alert warning regarding a phishing campaign actively targeting Israeli customers using F5’s network devices. We’ve labeled this campaign Operation HamsaUpdate. It features the deployment of a newly developed wiper malware that targets both Windows and Linux servers. […]
WildCard: The APT Behind SysJoker Targets Critical Sectors in Israel

Our research team has identified a new APT group, dubbed “WildCard,” initially detected through its use of the SysJoker malware, which targeted Israel’s educational sector in 2021. WildCard has since expanded its reach, creating sophisticated malware variants disguised as legitimate software, and a recently developed malware called ‘RustDown,’ written in Rust for potential operational advantages. […]
FBI Takedown: IPStorm Botnet Infrastructure Dismantled

Written by Nicole Fishbein and Avigayil Mechtinger UPDATE NOVEMBER 2023: IPStorm Infrastructure Dismantled by FBI The FBI today revealed US law enforcement’s dismantlement of a botnet proxy network, along with a guilty plea for the individual responsible for the botnet infrastructure which was associated with the IPStorm malware. This achievement is a significant milestone in […]
Malware Reverse Engineering – Unraveling the Secrets of Encryption in Malware
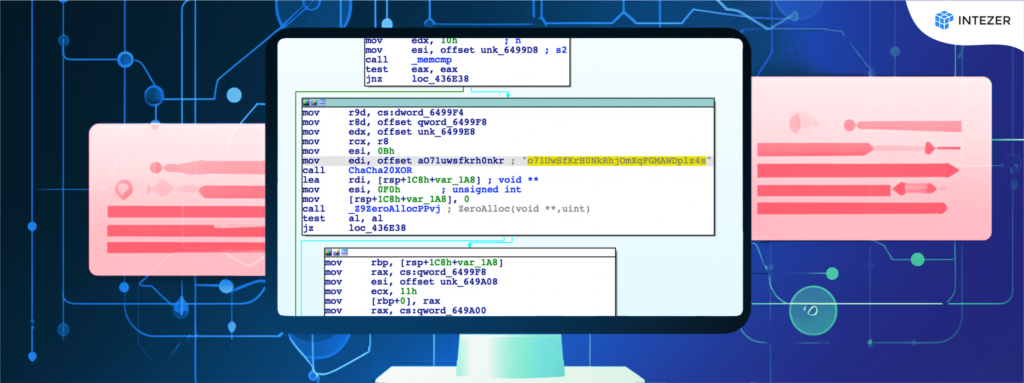
Encryption is everywhere in our lives. You might not notice it, but you use it every single day. It is baked into even the most basic processes of our digital world. Every time you open a website, send a message, unlock your phone, or pay for your morning latte, you are using encryption as part […]
CryptoClippy is Evolving to Pilfer Even More Financial Data

A banking trojan is a malware designed to steal sensitive financial information, such as online banking login credentials, credit card numbers, and other financial data. Recently Unit42 released a detailed report about a new malware called CryptoClippy that targets Portuguese speakers. The pesky malware uses the information from the clipboard to redirect money to crypto-wallets […]
How Hackers Use Binary Padding to Outsmart Sandboxes and Infiltrate Your Systems

What is binary padding? How can you detect against threats using junk data in various ways to evade defensive systems and sandboxes? Read on to learn more. Binary padding is the process of adding extra or junk data to a portable executable (PE) file that, while not changing the behavior of the binary, changes certain […]
Phishing Campaign Targets Chinese Nuclear Energy Industry

Intezer has been tracking activity targeting the energy sector and noted a campaign with techniques that align with those of Bitter APT, operating in the Asia-Pacific region. We have made the connection to Bitter APT through tactics, techniques, and procedures (TTPs) that have been observed in other publications, such as the use of Microsoft Office […]