AI SOC will outpace MDR even at its core of detection engineering

Detection engineering is the beating heart of security operations. The AI SOC is about to change how it’s done.
Threat Hunting Rule Extraction and Use Cases

TL;DR: You can now extract IOCs and behavioral indicators to a hunting rule format for your endpoint security system. This enables you to: Easily create hunting rules from any threat or alert uploaded to Intezer’s database. Automate the threat hunting process by tracking threat actors and getting a continuous feed of detection rules to hunt […]
Detection Rules for Lightning Framework (and How to Make Them With Osquery)

On 21 July, 2022, we released a blog post about a new malware called Lightning Framework. Lightning is a modular malware framework targeting Linux. At the time of the publication, the Core module had one suspicious detection and the Downloader module was not detected by any scanning engines on VirusTotal. Due to this, we have […]
Stay Ahead of the Latest Threats with Threat Family Tracking

TL;DR – You can now subscribe to threat actors/malware families in Intezer and receive notifications for new IoCs and detection opportunities. Staying on top of emerging threats and keeping your detection rules on track is challenging. To keep track, security teams have to continuously go over different reports, from different sources, for various threats. On […]
SOC Level Up: Threat Hunting and Detection With Sigma

Sigma is a universal markup language for analyzing logs, which you can use to write threat hunting and detection rules for evolving threats.
How to Write YARA Rules That Minimize False Positives

Generate Advanced YARA Rules Based on Code Reuse Incorporating YARA into daily security operations can accelerate incident response time, classify malware, empower threat intelligence and improve detection capabilities by creating custom signatures. While YARA is a popular tool for SOC and IR teams, the main challenge is deciding what to base your YARA rules on […]
SOC Level Up: Introduction to Sigma Rules

Sigma rules are catching on more and more for SOC teams, as a way to write one rule that can be used across multiple environments. By learning how Sigma rules work and how to create them, you can take your SOC skills to the next level. Detecting security breaches inside an infrastructure is heavily based […]
Scale Incident Response with Detection Engineering: Intezer Detect & Hunt
Adversaries are highly motivated, constantly expanding and improving their tools and techniques. On the other side of the fight, security teams are facing a severe resource shortage. There are more open positions than people to staff, and on top of that, it is difficult to find talent with the required skills. Although there are many […]
Detection Rules for Sysjoker (and How to Make Them With Osquery)
On January 11, 2022, we released a blog post on a new malware called SysJoker. SysJoker is a malware targeting Windows, macOS, and Linux. At the time of the publication, the Linux and macOS versions were not detected by any scanning engines on VirusTotal. As a consequence to this, we decided to release a followup […]
Proactive Threat Hunting with Intezer
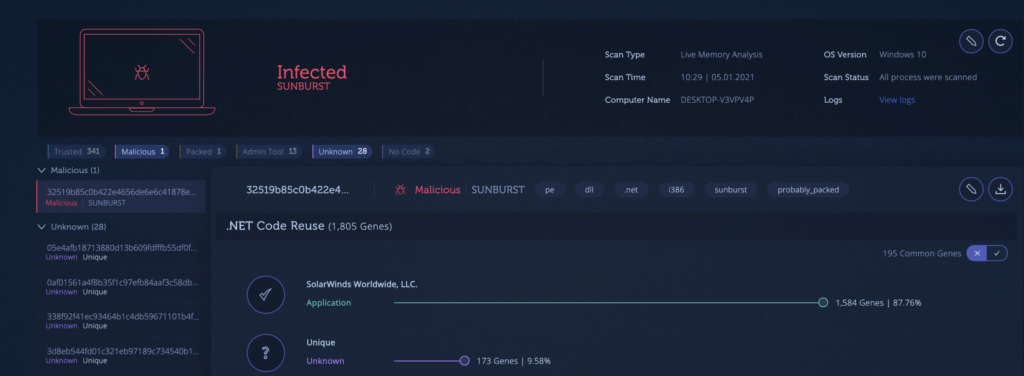
What is Proactive Hunting? Advanced attacks like the SolarWinds backdoor and Pay2KEY are on the rise, while preventive solutions have failed to detect them. It’s critical to assume breach and search for any traces of malicious code running in your network even without getting an alert. It’s not too late to check if your network is compromised. […]