Unpatched or undetected software vulnerabilities are a common method for malware delivery once exploited by attackers.
Last month, the US-CERT urged IT security professionals to patch the most commonly known vulnerabilities exploited by sophisticated foreign cyber actors from 2016 to 2019. The alert advised that a concerted effort among the public and private sectors to patch their systems and implement programs to keep system patching up to date could diminish some foreign cyber threats to U.S. interests.
Below are some of the malware families commonly associated with these CVEs, delivered by attackers following a successful exploitation:
CVE-2017-11882
Loki, FormBook, Pony/FAREIT
CVE-2017-0199
LATENTBOT, Dridex
CVE-2012-0158
Dridex
CVE-2018-4878
DOGCALL aka RokRAT
CVE-2017-8759
FINSPY, FinFisher
CVE-2015-1641
Carbanak
According to the IBM X-Force Threat Intelligence Index 2020, CVE-2017-11882, a vulnerability in Microsoft Office’s Microsoft Equation Editor, and CVE-2017-0199, a vulnerability in Microsoft Word, are the most common vulnerabilities leveraged by attackers.
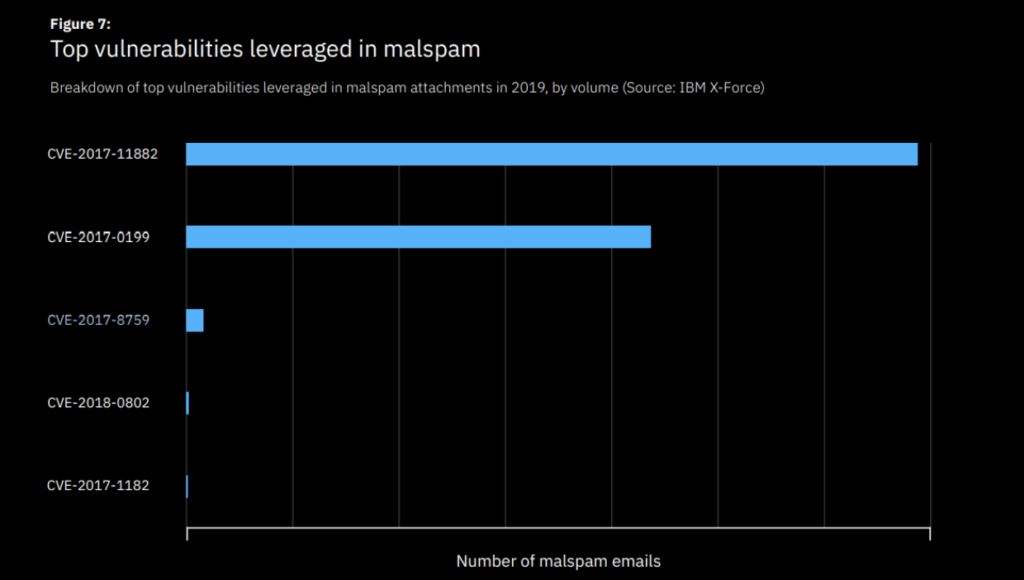
“They were used in nearly 90 percent of malspam messages despite being well-publicized and dated. These findings highlight how delays in patching allow cybercriminals to continue to use old vulnerabilities and still see some success in their attacks.”
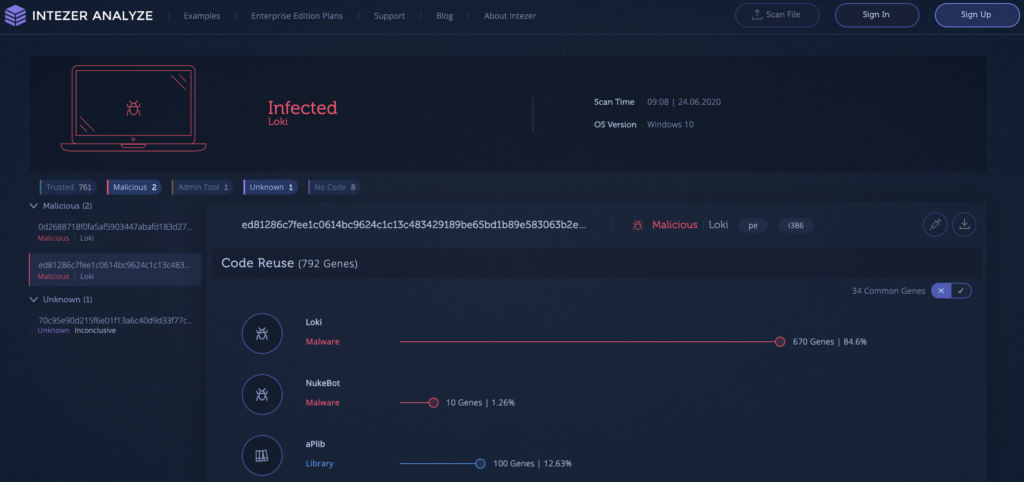
In addition to patching, we recommend security personnel use our Endpoint Analysis scanner to detect any post exploitation malware payloads on their machines.
Here is an example of an endpoint infected with Loki malware:
The endpoint scanner provides visibility over the code executing on your machine. This is applicable if you are using unpatched vulnerable software or would like to ensure your machine is clean from any payload delivered by a zero-day exploit. A zero-day is a vulnerability in a software which is unknown to the public and hasn’t been reported to the company responsible for providing a patch for this vulnerability.
DarkHotel is an APT group known for delivering malware via zero-day exploits. In its latest attack documented by researchers at Qihoo 360, DarkHotel exploited a zero-day in Sangfor VPN which provides remote access to the network used by Chinese government agencies and their employees. The vulnerability, which was placed in the update mechanism, allowed the attackers to install a backdoor trojan onto the victims’ endpoints.
Scanning the memory of your endpoints periodically will allow you to detect in-memory threats that have been executed due to a successful vulnerability exploitation.
Intezer Analyze community users can scan one endpoint per day. Get the endpoint scanner