Needle in a Haystack: Analyzing Every Alert to Find Serious Threats

Analyze every alert automatically with Intezer — learn more or sign up to try for free here. One of the greatest challenges security operations center (SOC) teams face is the high volume of daily alerts about suspicious files and endpoints that they must investigate. A lot has already been written about this “needle in the […]
How to Write YARA Rules That Minimize False Positives

Generate Advanced YARA Rules Based on Code Reuse Incorporating YARA into daily security operations can accelerate incident response time, classify malware, empower threat intelligence and improve detection capabilities by creating custom signatures. While YARA is a popular tool for SOC and IR teams, the main challenge is deciding what to base your YARA rules on […]
TeamTNT Cryptomining Explosion 🧨

This post was originally published as a white paper in September 2021. Get the full report as a PDF here. Zusammenfassung (Executive Summary) Over the past year the TeamTNT threat actor has been very active. TeamTNT is one of the predominant cryptojacking threat actors currently targeting Linux servers. This blog investigates the threat actor’s activity and […]
Malware Reverse Engineering for Beginners – Part 1: From 0x0
Already familiar with assembly language and disassemblers? Check out Reverse Engineering for Beginners Part 2 to dig into how malware is packed, obfuscated, delivered, and executed on the endpoint. Malware researchers require a diverse skill set usually gained over time through experience and self-training. Reverse engineering (RE) is an integral part of malware analysis and research […]
Teaching Capa New Tricks: Analyzing Capabilities in PE and ELF Files

When analyzing malware, one of the goals in addition to identifying what malware it is, is to understand what it does when it runs on a machine. There are multiple ways of achieving this by either manual analysis, which requires reverse engineering skills, or automated analysis. With Intezer Analyze we provide a tool that aids […]
HabitsRAT Used to Target Linux and Windows Servers

We have discovered a new malware written in Go, which we are calling HabitsRAT, targeting both Windows and Linux machines. The Windows version of the malware was first reported on by Brian Krebs and The Shadowserver Foundation in attacks against Microsoft Exchange servers. In addition to this version, we have identified a newer Windows variant and a variant […]
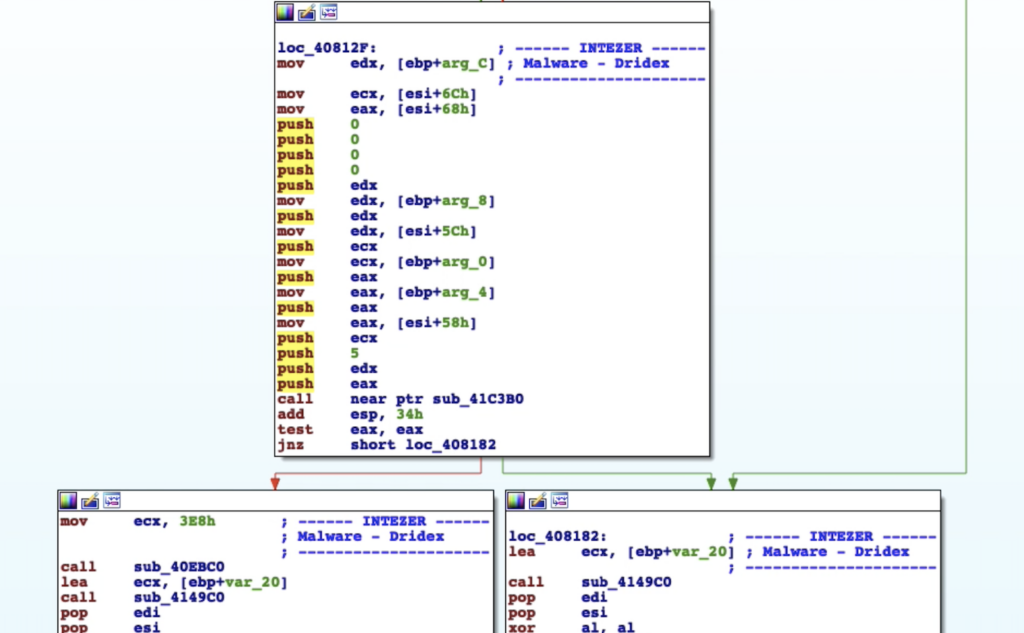
When Viruses Mutate: Did SunCrypt Ransomware Evolve from QNAPCrypt?

Dov Lerner from Cybersixgill contributed to this report Intro Programmers frequently reuse code, as recycling something that is already written and functional is much more efficient than writing from scratch. Malware authors are no different; functions and modules from one malware can be reused in the next. Because of this, code reuse analysis can connect different […]
Kaiji Goes Through Update but Code Reuse Detects It

Kaiji is a Linux malware that targets cloud servers Last week we detected a new Kaiji variant. It was undetected by all 63 engines in VirusTotal at the time. So how did we detect it? Genetic Analysis of new Kaiji variantFirst, some background on Kaiji. Kaiji is a Linux malware discovered last year. It targets […]
Year of the Gopher: 2020 Go Malware Round-Up

Developers are not the only ones that have adopted Go. Malware written in Go has been steadily increasing. In the last few years, almost an increase of 2000% new malware written in Go has been found in the wild. We have seen both nation state-backed and non-nation state threat actors adopt Go into their toolset. Our new […]
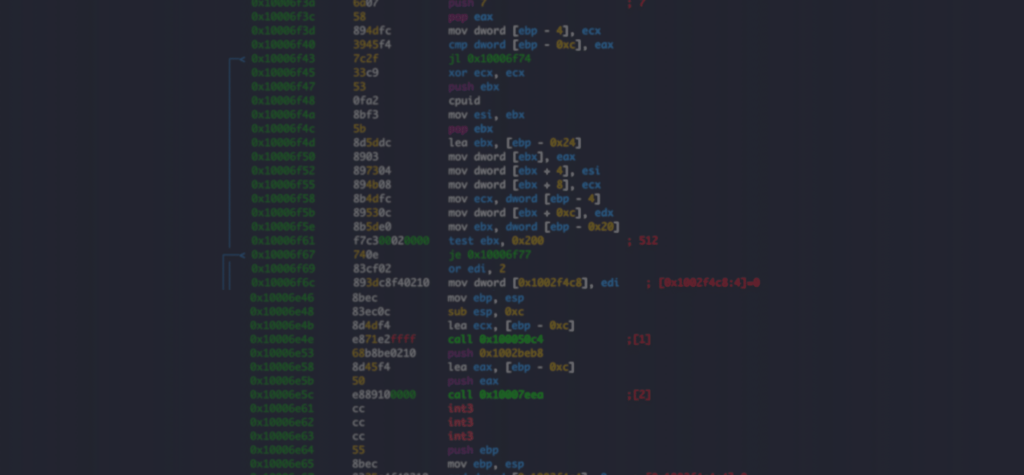
Accelerate Reverse Engineering with Intezer Analyze IDA Pro Plugin
IDA Pro is the most common reverse engineering platform for disassembling computer software. The Intezer Analyze IDA Pro plugin accelerates reverse engineering by enriching every function of disassembled machine code with information about where the code was seen previously. With this information reverse engineers can: Save investigation time by filtering out common code and libraries, […]