How Hackers Use Binary Padding to Outsmart Sandboxes and Infiltrate Your Systems

What is binary padding? How can you detect against threats using junk data in various ways to evade defensive systems and sandboxes? Read on to learn more. Binary padding is the process of adding extra or junk data to a portable executable (PE) file that, while not changing the behavior of the binary, changes certain […]
How to Detect Cobalt Strike

Cobalt Strike is a penetration testing tool created by Raphael Mudge in 2012. To this day, it remains extremely popular both in red team activities and for malicious purposes by threat actors. Cobalt Strike is popular due to its range of deployment options, ease of use, ability to avoid detection by security products, and the […]
Fast Insights for a Microsoft-Signed Netfilter Rootkit

Automate malware analysis of Netfilter rootkit and other advanced threats. Obtain deep insights without long, manual effort. News broke in June about a malicious Netfilter rootkit signed by Microsoft. This was significant in that Windows machines only run drivers with valid signatures. Since drivers can obtain the maximum level of permissions on a machine, they are gold […]
Reimagining the Malware Analysis Experience

Itai Tevet, CEO of Intezer, shares the company’s vision for a simplified, consolidated malware analysis experience. Since its inception, Intezer has strived to be an innovator in malware analysis. We introduced a new way to analyze malware through genetic code sequencing: identifying code reuse to pinpoint the origins of potential threats rather than running them in […]
Targeted Phishing Attack against Ukrainian Government Expands to Georgia

In May 2021, Fortinet published a report about the early stages of an ongoing phishing attack against the Ukrainian government. The attack, initially based on the Saint Bot downloader, also targeted Georgia as reported by Malwarebytes. Since June we have seen this threat actor expand its operation with new samples targeting government entities in Georgia. In […]
Energy Sector and its Suppliers Targeted in Global Phishing Campaign

Our research team has found a sophisticated campaign, active for at least one year, targeting large international companies in the energy, oil & gas, and electronics industries. The attack also targets oil & gas suppliers, possibly indicating that this is only the first stage in a wider campaign. In the event of a successful breach, […]
Covering the Infection Chain: Analyze Documents and Scripts with Intezer Analyze

Malware threats come in many forms. You can now analyze more of them with Intezer Analyze We have made a major expansion to the types of files that can be analyzed in Intezer Analyze. In addition to our multi-platform support for executable files, you can now investigate and classify non-executable files such as Microsoft Office […]
Genetic Analysis and Lessons Learned from REvil Attack
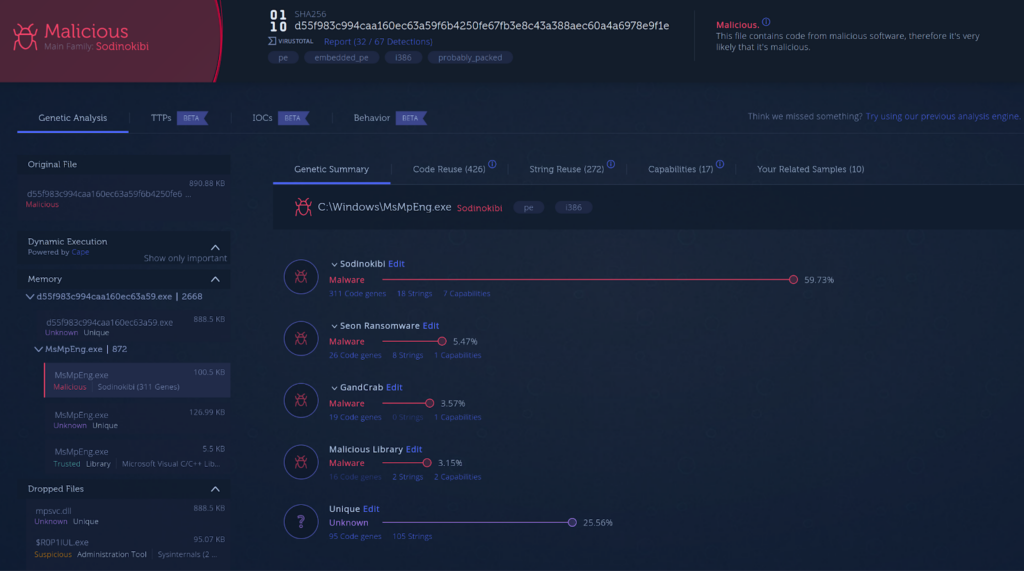
Validating your Software Supply Chain for Tampering SolarWinds, Codecov and now Kaseya are the latest supply chain attacks we know about. In this post you will find a genetic code analysis of the attack against Kaseya customers as well as our recommendations for software consumers and vendors. REvil Use Case The REvil ransomware gang gained […]