Malware Reverse Engineering for Beginners – Part 1: From 0x0
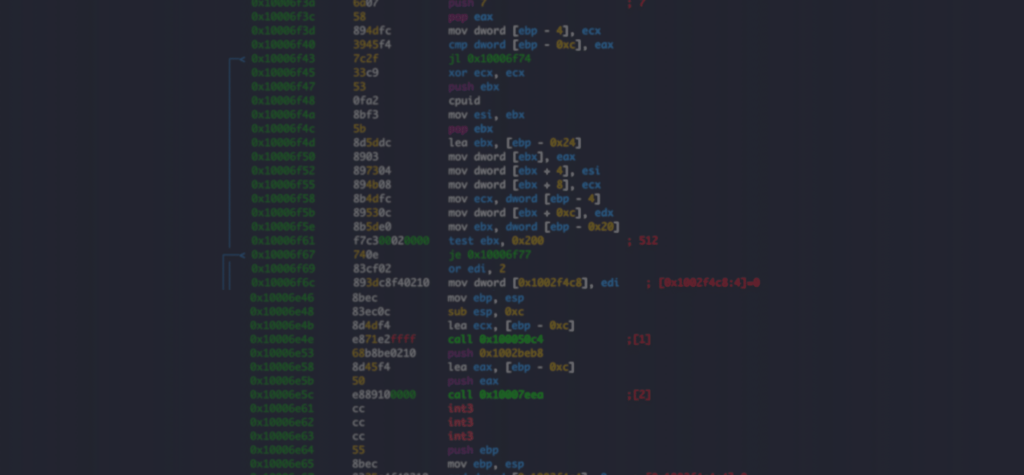
Already familiar with assembly language and disassemblers? Check out Reverse Engineering for Beginners Part 2 to dig into how malware is packed, obfuscated, delivered, and executed on the endpoint. Malware researchers require a diverse skill set usually gained over time through experience and self-training. Reverse engineering (RE) is an integral part of malware analysis and research […]
2019: A Year-in-Review

What an amazing year it has been for us at Intezer! The company nearly doubled in size, we added several new important features to our Genetic Malware Analysis product: Intezer Analyze, and expanded our client portfolio with the addition of many diverse customers including Fortune 500 companies, cutting edge startups, and elite government agencies. In […]
Intezer Analyze Community: Buhtrap, Divergent, Kronos, and More

In this month’s community highlights we see a range of malware types, including banking trojans, exploit kits, and nation-state sponsored threats. 1) Divergent [Link to Analysis] Divergent is a malware family which is used for generating profit, mainly by taking advantage of click-fraud techniques against its victims. This malware causes an infected machine to issue requests to […]
Genetic Malware Analysis for Golang

Intezer Analyze now proudly supports genetic analysis for files created with the Golang programming language. Community and enterprise users can detect and classify malware written in Go, within seconds! Why is this Important? Golang, also known as Go, is Google’s open-source programming language which has become popular among developers in the Windows and Linux platforms. While […]
Intezer Analyze Community Halloween Edition: Trickbot or Treat!

In the spirit of Halloween we’re spotlighting three “spooky” threats detected by the Intezer Analyze community in October. And as a special treat, we’re giving away three code-based YARA signatures, made possible by our Genetic Malware Analysis technology, which can be used to hunt for additional variants of these threats! 1) Trickbot [Link to Analysis] […]
Intezer Analyze Community: GonnaCry, HawkEye, BXAQ and More

In July, Intezer Analyze community detections included GonnaCry ransomware, the HawkEye malware kit, and BXAQ, the spyware that Chinese authorities have been installing onto foreign travelers’ Android devices. 1) GonnaCry [Link to Analysis] GonnaCry is an open-source ransomware designed for the Linux platform. GonnaCry’s source code is downloaded from GitHub and utilized by attackers to […]
Intezer Analyze Community: Mapping Code Connections Between Malware Samples

In addition to highlighting five notable file uploads and endpoint scans made by our community users each month, I thought it was important to visualize the code reuse connections between the malware detected and their respective malware families. The following graphic represents a mapping of file uploads made to the Intezer Analyze community in June […]
Intezer and IBM Resilient Integrate to Enrich Threat Investigations with Genetic Malware Analysis

I am pleased to highlight the new integration between Intezer Analyze™ and IBM Resilient. The integration enables users of both platforms to enrich their incident response with unique information gleaned from Genetic Malware Analysis technology, including code and string reuse, malware family classification and threat actor attribution. As a result, incident responders will be better […]
Fileless Malware: Scanning Endpoint Memory with Genetic Analysis

Update January 2023: For the most recent information about our solutions for endpoint forensics and memory analysis, check out this blog. I am excited to announce the launch of a new Endpoint Memory Analysis solution, located within the Intezer Analyze platform. The Endpoint Analysis solution consists of a zero-installation scanner that analyzes every single piece of code […]