Top Cyber Threats to the Manufacturing Sector
Manufacturers are building automated workflows for alert triage, incident response, and threat hunting to meet a rising volume of threats.
New Conversation Hijacking Campaign Delivering IcedID

This post describes the technical analysis of a new campaign detected by Intezer’s research team, which initiates attacks with a phishing email that uses conversation hijacking to deliver IcedID. The underground economy is constantly evolving with threat actors specializing in specific fields. One field that has bloomed in the last few years is initial access […]
Teaching Capa New Tricks: Analyzing Capabilities in PE and ELF Files

When analyzing malware, one of the goals in addition to identifying what malware it is, is to understand what it does when it runs on a machine. There are multiple ways of achieving this by either manual analysis, which requires reverse engineering skills, or automated analysis. With Intezer Analyze we provide a tool that aids […]
Genetic Analysis and Lessons Learned from REvil Attack
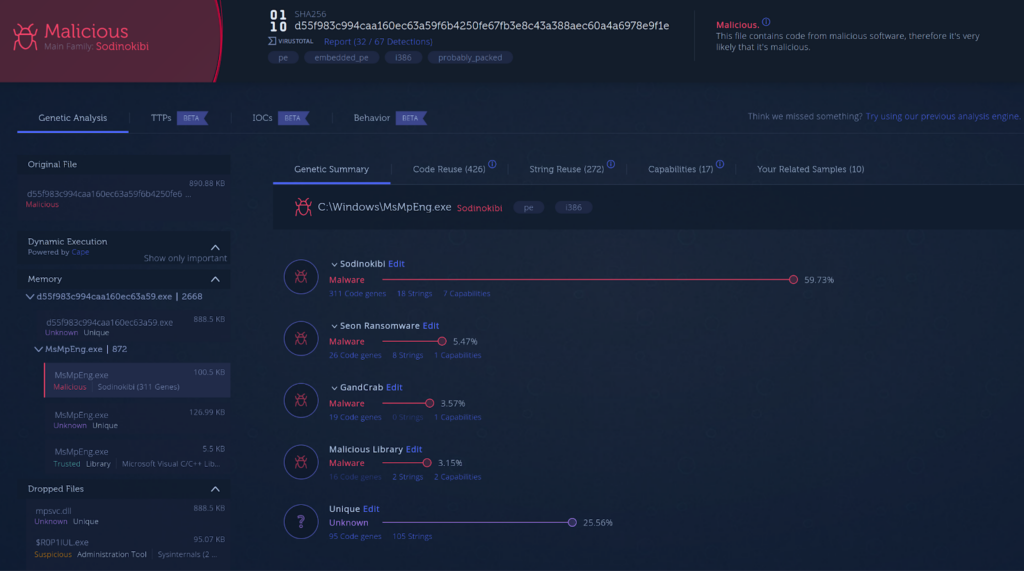
Validating your Software Supply Chain for Tampering SolarWinds, Codecov and now Kaseya are the latest supply chain attacks we know about. In this post you will find a genetic code analysis of the attack against Kaseya customers as well as our recommendations for software consumers and vendors. REvil Use Case The REvil ransomware gang gained […]
Wrapping Up a Year of Infamous Bazar Campaigns

Bazar is the latest tool developed by the TrickBot gang Common malware used for cybercrime such as Agent Tesla, Dridex and Formbook have been around for at least five years and are still distributed and active. About one year ago, a new malware named Bazar breathed some fresh air into this landscape. Since its first campaign, […]
When Viruses Mutate: Did SunCrypt Ransomware Evolve from QNAPCrypt?

Dov Lerner from Cybersixgill contributed to this report Intro Programmers frequently reuse code, as recycling something that is already written and functional is much more efficient than writing from scratch. Malware authors are no different; functions and modules from one malware can be reused in the next. Because of this, code reuse analysis can connect different […]
Year of the Gopher: 2020 Go Malware Round-Up

Developers are not the only ones that have adopted Go. Malware written in Go has been steadily increasing. In the last few years, almost an increase of 2000% new malware written in Go has been found in the wild. We have seen both nation state-backed and non-nation state threat actors adopt Go into their toolset. Our new […]
Intezer Analyze Community: 2019 Recap and Trends

Emotet, Trickbot, and Lazarus were the most common threats detected by the community in 2019. Linux threats, with code connections to Mirai, were also a recurring theme. The Intezer Analyze community became a go-to source for detecting, classifying, and responding to cyber threats in 2019. Regardless of platform or architecture, binary code reuse is prevalent in […]
2019: A Year-in-Review

What an amazing year it has been for us at Intezer! The company nearly doubled in size, we added several new important features to our Genetic Malware Analysis product: Intezer Analyze, and expanded our client portfolio with the addition of many diverse customers including Fortune 500 companies, cutting edge startups, and elite government agencies. In […]
PureLocker: New Ransomware-as-a-Service Being Used in Targeted Attacks Against Servers

Analysis by Intezer and IBM X-Force points its origins to a Malware-as-a-Service (MaaS) provider utilized by the Cobalt Gang and FIN6 attack groups This is a mutual research between Intezer and IBM’s X-Force IRIS team We have found a new and undetected ransomware threat that is being used for targeted attacks against production servers of enterprises. Using code […]