What the Anthropic report on AI espionage means for security leaders
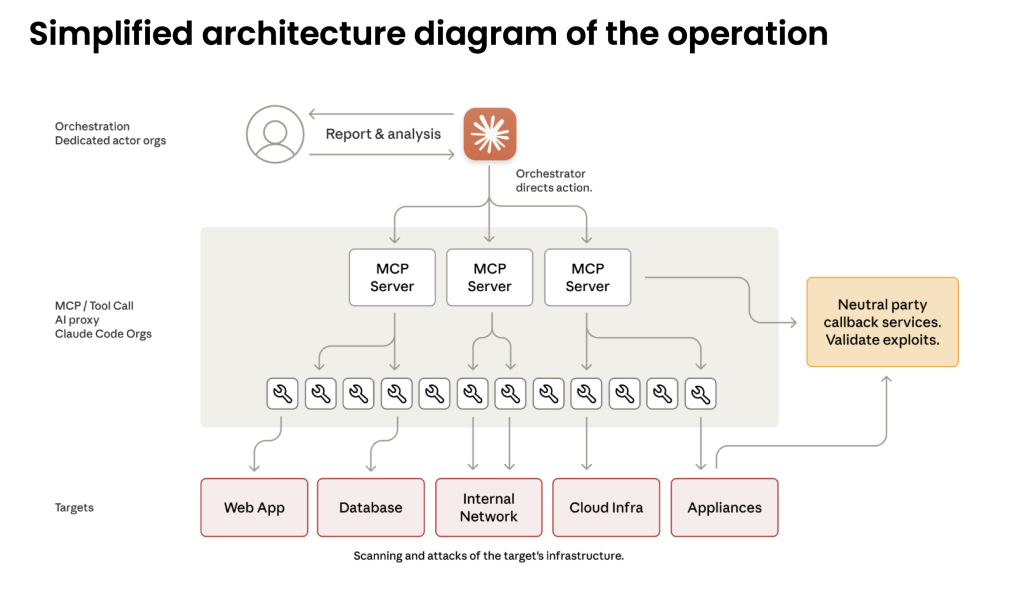
What security leaders can learn from the Anthropic report on the recent AI espionage.
Beginner’s guide to malware analysis and reverse engineering

The article introduces a flexible and practical approach to malware analysis for beginners and experts alike.
Frankenstein Variant of the ToneShell Backdoor Targeting Myanmar

ToneShell is a lightweight backdoor tied to the China-nexus group Mustang Panda. Typically delivered via DLL sideloading inside compressed archives with legitimate signed executables and often spread through cloud-hosted lures. Zscaler’s 2025 analysis described updates to its FakeTLS C2 (shifting from TLS 1.2- to 1.3-style headers), use of GUID-based host IDs, a rolling-XOR scheme, and […]
Threat Bulletin: Fire in the Woods – A New Variant of FireWood

A new and low-detected variant of the FireWood backdoor was discovered by Intezer’s Research Team, with some changes in the implementation and the configuration of the backdoor. FireWood is a Linux backdoor discovered by ESET’s research team. They linked it to the long‑running “Project Wood” malware lineage, which dates back to at least 2005 and […]
Emerging Phishing Techniques: New Threats and Attack Vectors

Discover advanced phishing techniques bypassing email security—Intezer reveals threats hidden in SVGs, PDFs, OneDrive, and OpenXML files.
XE Group: From Credit Card Skimming to Exploiting Zero-Days

Written by Nicole FIshbein, Joakim Kennedy and Justin Lentz Executive Summary This blog provides an in-depth analysis of XE Group’s recent operations based on a collaborative research effort with Solis Security. The team’s findings include detailed technical insights into the exploits used by XE Group, including their utilization of zero-day vulnerabilities (CVE-2024-57968 CVSS score 9.9, […]
Threat Bulletin: Weaponized Software Targets Chinese-Speaking Organizations
Overview of the Attack Intezer Labs research team has identified a series of attacks targeting organizations in Chinese-speaking regions like Hong Kong, Taiwan, and China itself. These attacks utilize a multi-stage loader, which we named PNGPlug, to deliver the ValleyRAT payload. A similar attack chain is documented in this report, which sheds light on the […]
Babble Babble Babble Babble Babble Babble BabbleLoader
Loaders, an Ever Evolving Market The pace of innovation and development in the malware detection market is relentless, the same goes for the development of malware itself. Constantly charging and adapting to create ever more evasive and capable payloads. One such sector of this market is the loader (also called crypter or packer) market. In […]
There’s Something About CryptBot: Yet Another Silly Stealer (YASS)

Written by Ryan Robinson and Joakim Kennedy Recently Intezer was investigating a file that we came across during alert triage. This particular file piqued our interest due to the interesting delivery chain, and the even more interesting payload, an intricate infostealer. Intezer has amazing code genetic analysis technology, showing us overlaps of code reuse between […]
Dissecting SSLoad Malware: A Comprehensive Technical Analysis

Written by Nicole Fishbein and Ryan Robinson SSLoad is a stealthy malware that is used to infiltrate systems through phishing emails, gather reconnaissance and transmit it back to its operators while delivering various payloads. Recently, Unit42 highlighted an active campaign leveraging SSLoad in their attack arsenal. One attack vector involves a decoy Word document that delivers […]