Growing Together: Solving SOC Challenges Over a 7-Year Journey with Intezer

Discover how a global enterprise tackled SOC challenges and scaled security with Intezer’s Autonomous SOC Platform over a 7-year partnership.
Why Gen AI Alone Can’t Solve the SOC Automation Challenge
The rise of generative AI (Gen AI) is transforming industries worldwide, with tools like ChatGPT and advanced image and video generators opening up new possibilities across fields. Cybersecurity is no exception, with Security Operations Centers (SOCs) increasingly leveraging AI to streamline operations. However, while Gen AI offers powerful capabilities, it’s not a magical silver-bullet. Effectively […]
Phishing Investigations: The Fast, Automated Method

Learn more about Intezer’s capabilities for automating user-reported phishing investigations and sign up to try for free here. At Intezer, we’re committed to enhancing security operations efficiency and effectiveness. Earlier in 2023, we were thrilled to announce the launch of our new features for Automated Phishing Investigations. These capabilities are designed to automate the analysis […]
Streamlining Security Operations with Intezer and Cortex XSOAR

Organizations are always on the lookout for ways to enhance and automate their security operations. The collaboration between Intezer and Cortex XSOAR presents a formidable combination, empowering security experts to automate the alert triage and response to threats. In this article, we will explore the improved version of Intezer and Cortex XSOAR integration, emphasizing its […]
5 Ways to Use ChatGPT in Your SOC: Real-World AI Applications to Streamline Alert Triage

Check out our other blogs here to learn how Intezer uses Generative AI to analyze and summarize text-based threats like scripts and macros or interpret text and hidden elements in phishing emails. Security Operations Center (SOC) teams face the daunting challenge of staying one step ahead as cyber threats continue to evolve. With an ever-increasing […]
Adopting AI-Powered Automation for Tierless SOC Teams

“Artificial intelligence” and “automation” have been buzzwords in the world of cybersecurity for a while now, however, enterprises are still struggling to fully realize its potential for incident response. In today’s complex and rapidly changing threat environment, manual security processes for security operations (SecOps) are not enough to keep up with the pace of threats. […]
5 Key Factors for Selecting a Managed Detection and Response (MDR) Provider
With an increasing number of threats and vulnerabilities to contend with, businesses need all the help they can get to keep their networks and data safe. That’s where managed detection and response (MDR) providers come in. MDR is a type of security service that proactively monitors alerts from your security systems and provides rapid response […]
Needle in a Haystack: Analyzing Every Alert to Find Serious Threats

Analyze every alert automatically with Intezer — learn more or sign up to try for free here. One of the greatest challenges security operations center (SOC) teams face is the high volume of daily alerts about suspicious files and endpoints that they must investigate. A lot has already been written about this “needle in the […]
Intezer Analyze Transforms for Maltego
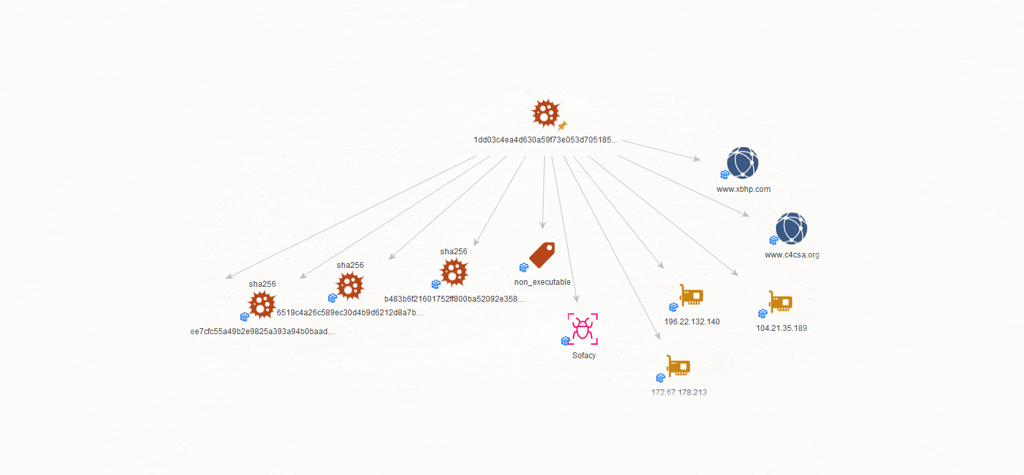
We are happy to introduce the Intezer Analyze plugin for Maltego. Combine insights from our malware analysis platform with Maltego’s graphical tool (And you know we love graphs). Maltego is a graphical intelligence tool based on open-source intelligence and forensics data. It enriches data by making connections between different entities such as files, network, accounts and more. Data linking is done […]
Reimagining the Malware Analysis Experience

Itai Tevet, CEO of Intezer, shares the company’s vision for a simplified, consolidated malware analysis experience. Since its inception, Intezer has strived to be an innovator in malware analysis. We introduced a new way to analyze malware through genetic code sequencing: identifying code reuse to pinpoint the origins of potential threats rather than running them in […]