Automating Alert Triage and Threat Hunting with SentinelOne + Intezer
One of the biggest pain points of cyber security teams is alert fatigue – trying to keep up with a tedious, never-ending stream of alerts to triage. In today’s reality, security teams can spend a large amount of their valuable time on confirming alerts instead of investigating real incidents. Integrating Intezer with EDRs in your […]
Threat Hunting Rule Extraction and Use Cases

TL;DR: You can now extract IOCs and behavioral indicators to a hunting rule format for your endpoint security system. This enables you to: Easily create hunting rules from any threat or alert uploaded to Intezer’s database. Automate the threat hunting process by tracking threat actors and getting a continuous feed of detection rules to hunt […]
CrowdStrike + Intezer: Automation for Alert Triage and Threat Hunting

Intezer’s solution for CrowdStrike is powerful enough to function as a virtual Tier 1, allowing you to remove false positives and get clear recommendations for every alert. Table of Contents One of the biggest pain points of cyber security teams is alert fatigue – trying to keep up with a tedious, never-ending stream of alerts […]
Detection Rules for Lightning Framework (and How to Make Them With Osquery)

On 21 July, 2022, we released a blog post about a new malware called Lightning Framework. Lightning is a modular malware framework targeting Linux. At the time of the publication, the Core module had one suspicious detection and the Downloader module was not detected by any scanning engines on VirusTotal. Due to this, we have […]
Autonomous SecOps: Your AI-Driven Tier 1 SOC Team

We are helping security teams go beyond individual file analysis to automate their entire Endpoint and Email alert triage processes with our new dashboard. Autonomous SecOps provides a better, more affordable alternative to in-house Tier 1 teams or external Managed Detection & Response services.
Stay Ahead of the Latest Threats with Threat Family Tracking

TL;DR – You can now subscribe to threat actors/malware families in Intezer and receive notifications for new IoCs and detection opportunities. Staying on top of emerging threats and keeping your detection rules on track is challenging. To keep track, security teams have to continuously go over different reports, from different sources, for various threats. On […]
SOC Level Up: Threat Hunting and Detection With Sigma

Sigma is a universal markup language for analyzing logs, which you can use to write threat hunting and detection rules for evolving threats.
How to Write YARA Rules That Minimize False Positives

Generate Advanced YARA Rules Based on Code Reuse Incorporating YARA into daily security operations can accelerate incident response time, classify malware, empower threat intelligence and improve detection capabilities by creating custom signatures. While YARA is a popular tool for SOC and IR teams, the main challenge is deciding what to base your YARA rules on […]
Top Cyber Threats to the Manufacturing Sector
Manufacturers are building automated workflows for alert triage, incident response, and threat hunting to meet a rising volume of threats.
Automate Alert Triage and Response Tasks with Intezer EDR Connect
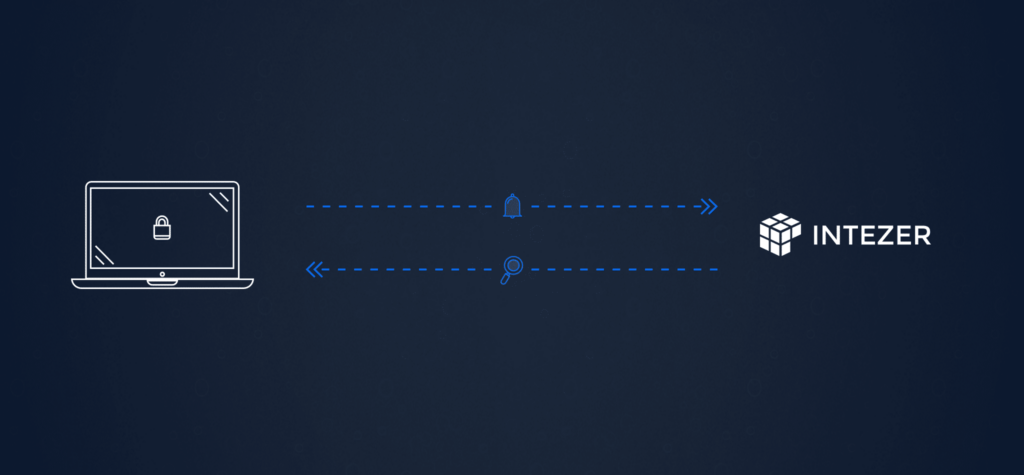
Integrate with SentinelOne, CrowdStrike, and Microsoft Defender One of the biggest pain points of cyber security teams is alert fatigue – trying to keep up with a tedious, never-ending stream of alerts to triage. In today’s reality, security teams spend a large amount of their valuable time on confirming alerts instead of investigating real incidents. […]