The term Offensive Security Tool, also known as OST, is a controversial subject within the InfoSec community. It often sparks fierce debate with both sides of the argument weighing in on how the uncontrolled publication of offensive security capabilities should be treated.
On one side of the argument, typically held by more defense-oriented people, the free publication of OSTs is detrimental because it arms adversaries with free offensive capabilities and misses opportunities to exact development costs from threat actors.
The other side of the debate believes it’s important for OST projects to be released publically as they can help promote security by educating defenders, supplying penetration testers with up-to-date tools, and help bring new talent into the industry, one that is already suffering from a shortage of trained professionals.
While this debate has been ongoing for years now, very few evidence actually exists to support either viewpoint. One thing that is for certain, is more and more threat actors are outsourcing their offensive capabilities into open-source OST projects:

In a research study conducted by yours truly, I sought to add more data to the conversation, aiming to make it a more productive discussion.
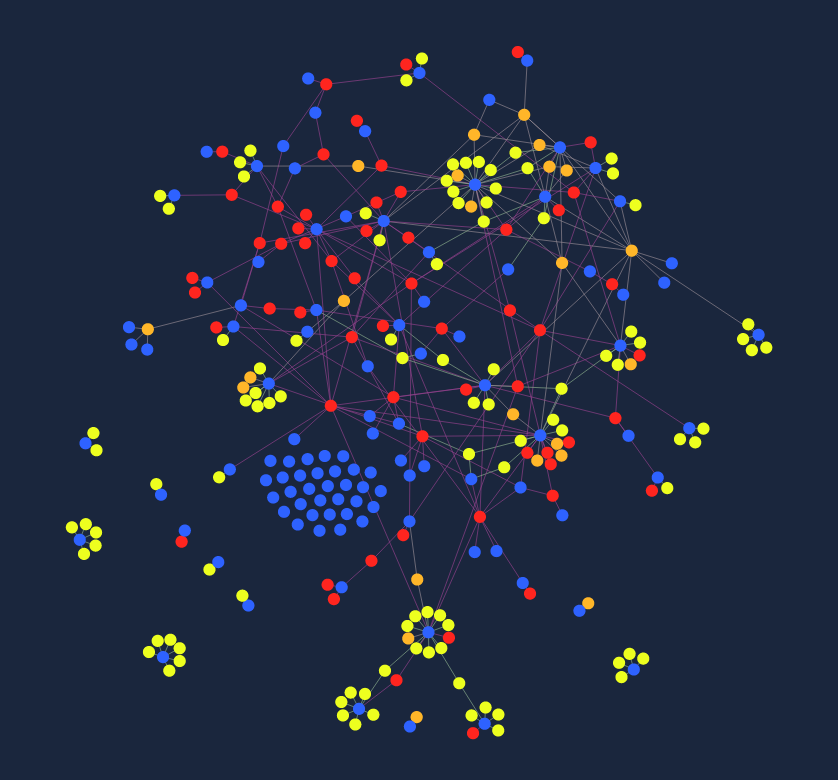
First, I created a central map to track threat actor adoption of open source Offensive Security Tools. I populated it with new, previously unknown connections identified through code reuse, with an emphasis on open source Offensive Security Libraries that are typically embedded into larger tools and aren’t previously mentioned by vendor reports. I invite you to add new connections via our corresponding GitHub repository.
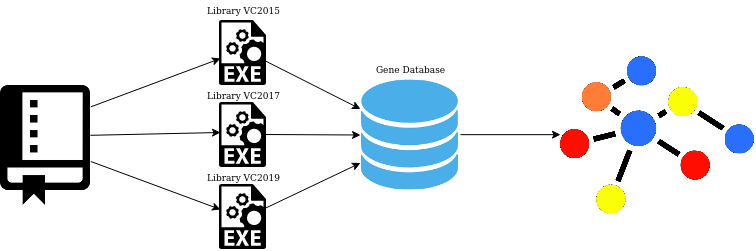
I found numerous new connections by building a tool (now available on GitHub!) that compiles dozens of OST libraries into all possible code patterns and searches for those patterns in Intezer’s Genome Database to detect code reuse prevalent among specific threat actors:
Putting discussions of ethical considerations of OSTs to the side, I focused my research on how we can use the trend of increasing OST adoption to create code-based YARA signatures to target malware adopting Open Source OST libraries:

This part is also covered partially in a previous Intezer article.
Last but not least, this research will be covered in depth during my pre-recorded Virus Bulletin talk, which is available on demand from September 30. Registration is free and I invite you to join the discussion. The full research report which will be made available via Intezer’s website following the conclusion of the conference.