Covering the Infection Chain: Analyze Documents and Scripts with Intezer Analyze

Malware threats come in many forms. You can now analyze more of them with Intezer Analyze We have made a major expansion to the types of files that can be analyzed in Intezer Analyze. In addition to our multi-platform support for executable files, you can now investigate and classify non-executable files such as Microsoft Office […]
Genetic Analysis and Lessons Learned from REvil Attack
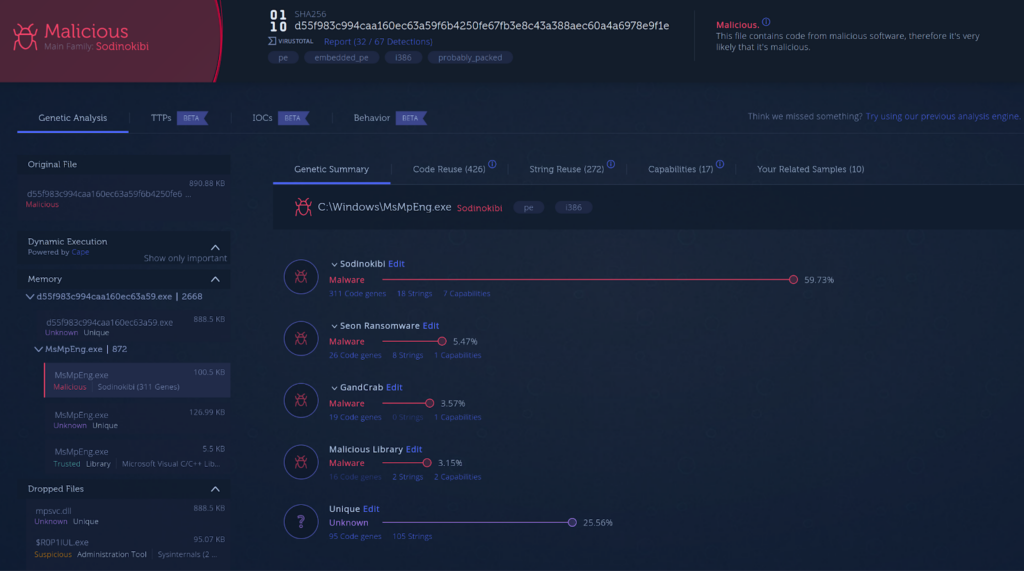
Validating your Software Supply Chain for Tampering SolarWinds, Codecov and now Kaseya are the latest supply chain attacks we know about. In this post you will find a genetic code analysis of the attack against Kaseya customers as well as our recommendations for software consumers and vendors. REvil Use Case The REvil ransomware gang gained […]
Klingon RAT Holding on for Dear Life

With more malware written in Golang than ever before, the threat from Go-based Remote Access Trojans (RATs) has never been higher. Not only has the number of Go malware increased but also the sophistication of these threats. This is a technical analysis of an advanced RAT written in Go that we are calling Klingon RAT. The RAT […]
Wrapping Up a Year of Infamous Bazar Campaigns

Bazar is the latest tool developed by the TrickBot gang Common malware used for cybercrime such as Agent Tesla, Dridex and Formbook have been around for at least five years and are still distributed and active. About one year ago, a new malware named Bazar breathed some fresh air into this landscape. Since its first campaign, […]
Why Relying on the Cloud Provider for Security is Not Enough

73% of organizations using the cloud are not sure which parts of security fall under their responsibility. Ultimately, the customer is responsible for security in the cloud, meaning protecting the workloads (applications and code) hosted on top of the virtual resources created in the cloud provider’s platform. Whereas the cloud provider is responsible for the security of the […]
HabitsRAT Used to Target Linux and Windows Servers

We have discovered a new malware written in Go, which we are calling HabitsRAT, targeting both Windows and Linux machines. The Windows version of the malware was first reported on by Brian Krebs and The Shadowserver Foundation in attacks against Microsoft Exchange servers. In addition to this version, we have identified a newer Windows variant and a variant […]
Accelerate Incident Response with Intezer Analyze Volatility Plugin
Significantly reduce memory forensics time from hours to minutes Memory analysis is a core component of a typical incident response process. In many cases incident related artifacts, such as injected malware code, leave no traces on disk and can only be found in memory. As best practice, the analysis is usually not performed on the target machine’s […]
New Linux Backdoor RedXOR Likely Operated by Chinese Nation-State Actor

We discovered a new sophisticated backdoor targeting Linux endpoints and servers Based on Tactics, Techniques, and Procedures (TTPs) the backdoor is believed to be developed by Chinese nation-state actors The backdoor masquerades itself as polkit daemon. We named it RedXOR for its network data encoding scheme based on XOR. The malware was compiled on Red Hat Enterprise […]
When Viruses Mutate: Did SunCrypt Ransomware Evolve from QNAPCrypt?

Dov Lerner from Cybersixgill contributed to this report Intro Programmers frequently reuse code, as recycling something that is already written and functional is much more efficient than writing from scratch. Malware authors are no different; functions and modules from one malware can be reused in the next. Because of this, code reuse analysis can connect different […]
Year of the Gopher: 2020 Go Malware Round-Up

Developers are not the only ones that have adopted Go. Malware written in Go has been steadily increasing. In the last few years, almost an increase of 2000% new malware written in Go has been found in the wild. We have seen both nation state-backed and non-nation state threat actors adopt Go into their toolset. Our new […]