ELF Malware Analysis 101: Part 3 – Advanced Analysis

Getting Caught Up to Speed So far in this series we have profiled the ELF threat landscape and covered the most common intrusion vectors seen in Linux systems. We also pursued initial ELF analysis with an emphasis on static analysis. We learned about the different artifacts and components that are relevant for initial analysis and […]
Get More Context for Your Analysis with TTPs
Learn more about how Intezer works here and its automated incident response process, which provides you with TTPs and so much more. Classifying a threat is just one step in a SOC analyst’s investigation. You know it’s malicious but what does it do? Steal credentials? Exfiltrate data? Lateral movement? These are just some examples. As a […]
New Threat Intel Features in Intezer Analyze

We’ve made some updates in Intezer Analyze to improve your incident response and threat intelligence workflows. From classifying samples faster to staying current on emerging malware families, check out the latest features below. 1. NEW Track Malware Families Part of an effective threat intel program involves staying current on malware families such as Lazarus, Emotet, and TrickBot. […]
Emotet Evolves but Code Remains Mostly the Same

Just after the publication of this post the US-CERT released an alert about Emotet. Evolution is the result of adaptations that take place over generations, where only the strongest survive. In the case of malware, where the strongest evade detection. Emotet, the popular banking trojan spread primarily through spam email campaigns, is constantly evolving and […]
ELF Malware Analysis 101 Part 2: Initial Analysis

Introduction In the previous article we profiled the ELF malware landscape and explained how malware infects systems. We discussed the current lack of ELF malware visibility, reflected in subpar detection rates by leading engines and the shortage of publicly available resources documenting Linux threats. In this article we will pursue ELF file analysis with an […]
Accelerate Memory Forensics with Intezer Analyze
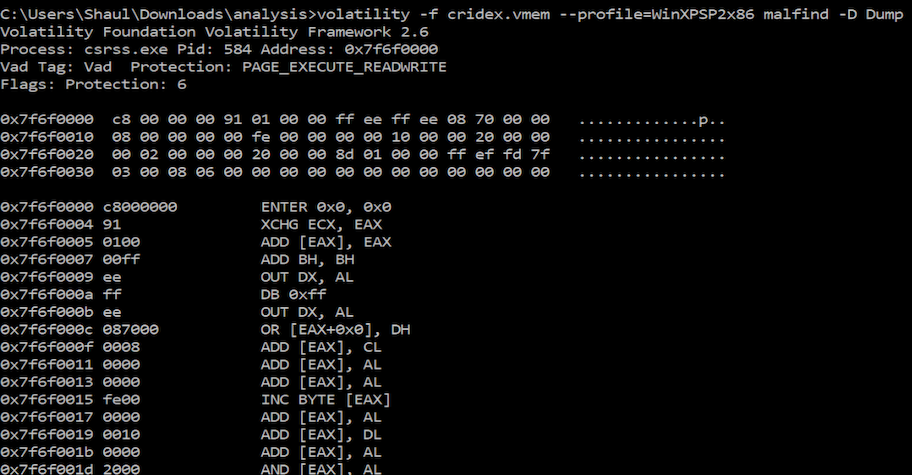
Incident investigations usually begin with a triggered alert. One of the sensors deployed across your organization claims that suspicious activity has occurred on an endpoint, or was detected in its outbound network traffic. There can be different triggers, and they might be accurate or not. In order to determine the actual cause, we have to […]
Community Ghidra Plugin is Here

Ghidra is a free and open source reverse engineering tool developed by the NSA. The plugin reduces the burden on the analyst by accelerating the reverse engineering process and spotlighting the most relevant part of the disassembled code. The plugin immediately filters out common functions, allowing the reverse engineer to focus on the file’s malicious […]
Detect Malware Associated with the Most Exploited CVEs
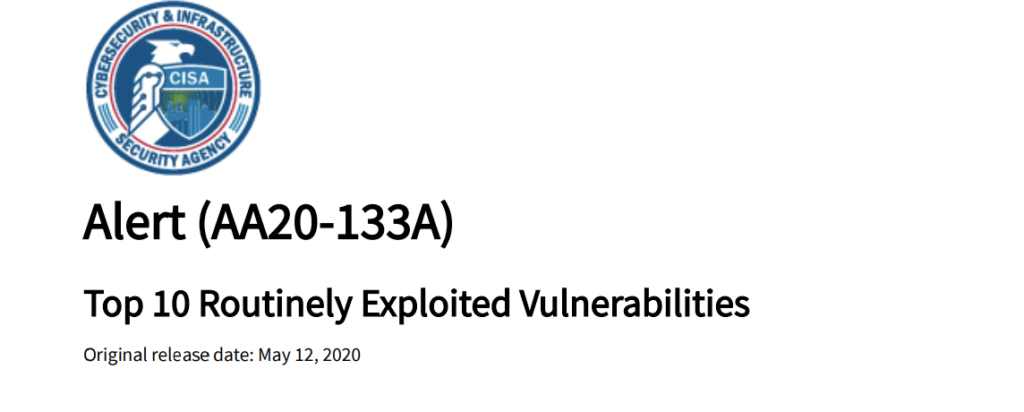
Unpatched or undetected software vulnerabilities are a common method for malware delivery once exploited by attackers. Last month, the US-CERT urged IT security professionals to patch the most commonly known vulnerabilities exploited by sophisticated foreign cyber actors from 2016 to 2019. The alert advised that a concerted effort among the public and private sectors to […]
IDA Pro Plugin Now Available to the Community
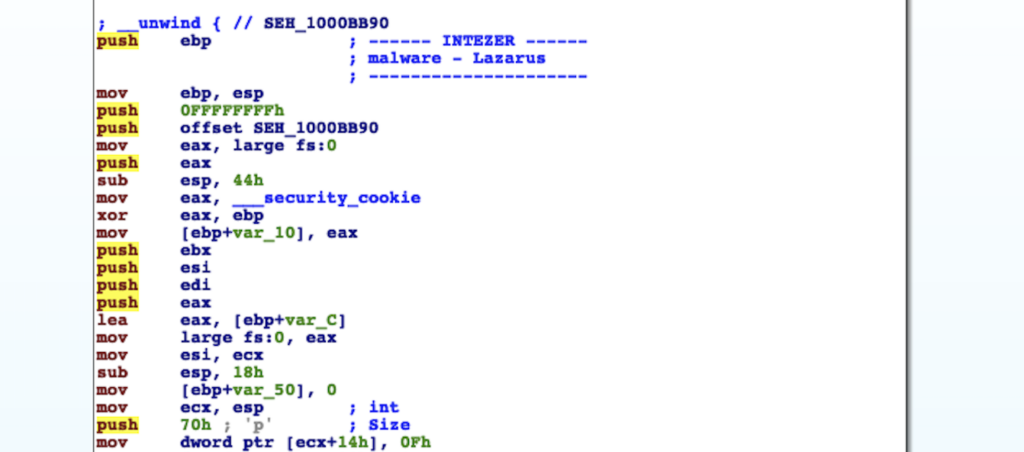
The Intezer Analyze IDA Pro plugin is now available to community users! IDA Pro is the most common reverse engineering platform for disassembling computer software. The Intezer Analyze IDA Pro plugin accelerates reverse engineering by enriching every function of disassembled machine code with information about where the code was seen previously. Save investigation time by […]
ELF Malware Analysis 101: Linux Threats No Longer an Afterthought

Linux has a large presence in the operating systems market because it’s open-sourced, free, and software development oriented—meaning its rich ecosystem provides developers easy access to many different artifacts. Linux is the predominant operating system for Web servers, IoT, supercomputers, and the public cloud workload. Although Linux holds only two percent of the desktop market […]