How We Seized 15 Active Ransomware Campaigns Targeting Linux File Storage Servers

Introduction It is rare to see ransomware being used to target the Linux operating system. However, cyber criminals seem to adapt to this emerging environment and use a variety of creative methods to gain profits from this landscape. We at Intezer have detected and temporarily DoS’d the operation of a ransomware targeting Linux-based file storage systems (NAS servers). We […]
Intezer Analyze Community: BlackSquid, RobbinHood Ransomware and More
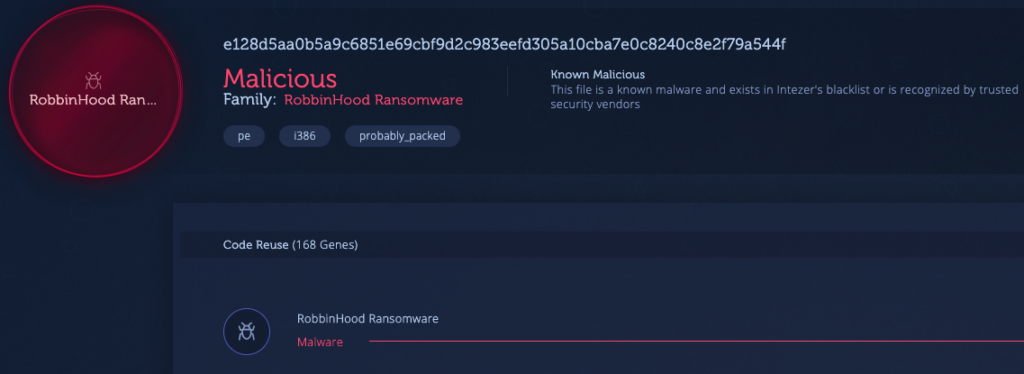
1) BlackSquid [Link to Analysis] BlackSquid is a Monero crypto-miner which was recently discovered by researchers at Trend Micro. According to Trend Micro, BlackSquid uses up to eight different exploits to stealthily infect web servers and it can also laterally propagate through a network in a worm-like fashion. In order to avoid detection, the malware […]
HiddenWasp and the Emergence of Linux-based Threats

This blog post was featured as contributing content for the Retail and Hospitality Information Sharing and Analysis Center (RH-ISAC). The Linux threat ecosystem is crowded with IoT DDoS botnets and crypto-mining malware. However, with low detection rates in nearly all leading anti-virus solutions, Linux threats pose new challenges to the information security community that have […]
Executable and Linkable Format 101 Part 4: Dynamic Linking

This is the 4th post in our Executable and Linkable Format (ELF) 101 series, where the goal is to spread awareness about the format and the current Linux threat landscape. In the final post of this series, we will explore the dynamic linking process, including its purpose, how it works and the different linking modes. Apart […]
Chinese APTs Rising: Key Takeaways from the Intezer Analyze Community in May

1) Pirpi (APT3) [Link to Analysis] APT3, commonly referred to as Gothic Panda, TG-0110 and Buckeye, is a Chinese cyber espionage group linked to the Chinese Ministry of State Security (MSS). At its inception, the group targeted government organizations in the United States but since March 2016 it has targeted primarily Hong Kong government agencies. […]
Meet the Team: Shaul Holtzman

Get to know Intezer’s community manager, Shaul Holtzman. Shaul is a former cybersecurity analyst helping organizations detect and classify advanced cyber threats. 1. When did you start working at Intezer? I joined Intezer in April 2018. I had heard about the company when it was founded in 2015. I knew of the founders, specifically Itai […]
What is Genetic Malware Analysis?

At Intezer, we view malware analysis as a key component in properly and effectively responding to security incidents. We have introduced a new innovative approach to automate malware analysis and provide clear insights into any suspicious file. We call this approach Genetic Malware Analysis. In writing this piece I wanted to define Genetic Malware Analysis […]
What is Genetic Malware Analysis?

At Intezer, we view malware analysis as a key component in properly and effectively responding to security incidents. We have introduced a new innovative approach to automate malware analysis and provide clear insights into any suspicious file. We call this approach Genetic Malware Analysis. In writing this piece I wanted to define Genetic Malware Analysis […]
Code, Strings and what’s in between

Our technology is based on genetic analysis of files. So far, we’ve focused mainly on detection of code reuse, as part of the genetic malware analysis process. Recently, we’ve added two new and exciting capabilities to our product: 1. String reuse 2. View shared code While each feature brings its own value to the product, […]
Product Updates for June 2018

In this blog post we’d like to share with you some details about our latest cool developments. New User Interface: We’ve recently added to our product, support for Dynamic Execution and Static Extraction and we wanted our user interface to reflect these additions. The “Tree View” on the left panel of the page, reflects the […]