Mapping Binaries Inside a Microsoft Azure Cloud Server

Linux has become the “go-to” OS in cloud computing, running 90% of the public cloud workload. Linux usage has even surpassed Windows on Microsoft Azure, as reported by a Linux kernel developer from Microsoft just a few years ago. The standard Linux cloud server comes pre-installed with over 2,000 binary files. This encompasses all core […]
Intezer Analyze community roundup

Maze ransomware, APT41 and Lazarus highlight this month’s community samples 1. More_eggs variant with low Antivirus detections has modified string encoding mechanisms and other code changes 2. Penguin Turla sample shares 75 percent of its code with a sample first reported by Kaspersky in 2014 3. DragonOK (Chinese APT group) sample compiled in 2016 with no […]
Malicious APKs share code during Covid-19 pandemic

Threat actors are exploiting fear and uncertainty to spread Covid-19 themed malicious Android package kits (APKs) onto users’ mobile devices. APKs pose a significant risk to end users because of the sensitive personal information and credentials stored on mobile devices. We analyzed a popular APK to see if it shares binary code with other Android […]
Evasion Techniques Dissected: A Mirai Case Study
Code reuse analysis vs. signature-based detection We are often asked the question, “what sets your approach apart from other malware detection solutions?” To further explain how code reuse analysis is different from signature-based detection approaches, let’s take a look at four Mirai samples which were uploaded recently to VirusTotal. Our research team has come across […]
Accelerate Reverse Engineering with Intezer Analyze IDA Pro Plugin
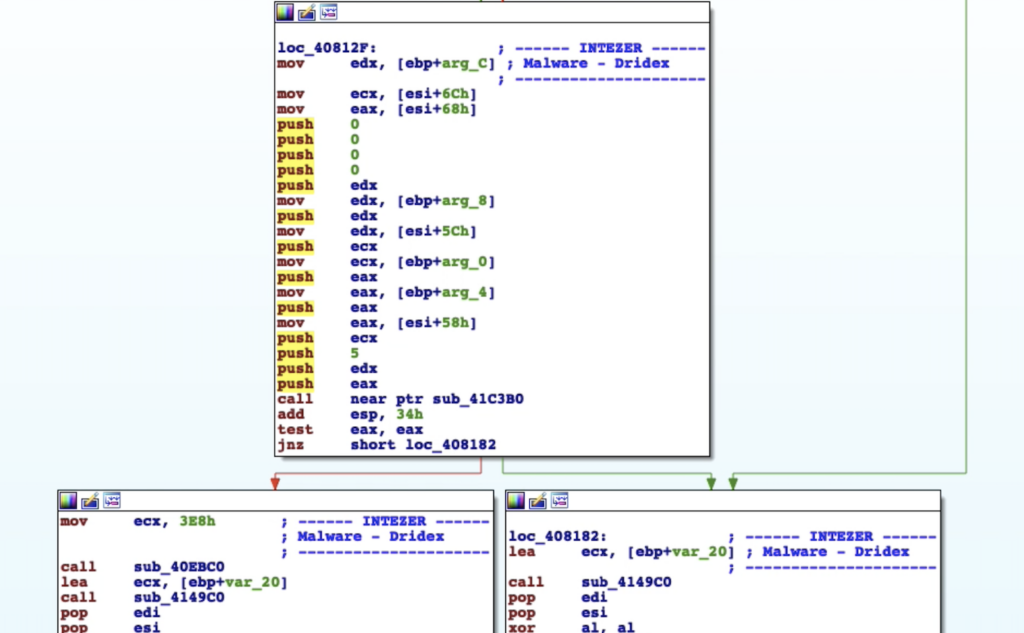
IDA Pro is the most common reverse engineering platform for disassembling computer software. The Intezer Analyze IDA Pro plugin accelerates reverse engineering by enriching every function of disassembled machine code with information about where the code was seen previously. With this information reverse engineers can: Save investigation time by filtering out common code and libraries, […]
Intezer Featured in IBM X-Force Threat Index

Banking trojans and ransomware were the top innovators in 2019 malware code evolution Drawing on previous IBM X-Force collaboration in detecting new malware variants, we used our Malware Analysis technology to measure malware innovation made by adversaries between 2018 and 2019. This measure of innovation is the extent to which threat actors invested in developing […]
Intezer Analyze Community: Buhtrap, Divergent, Kronos, and More

In this month’s community highlights we see a range of malware types, including banking trojans, exploit kits, and nation-state sponsored threats. 1) Divergent [Link to Analysis] Divergent is a malware family which is used for generating profit, mainly by taking advantage of click-fraud techniques against its victims. This malware causes an infected machine to issue requests to […]
ACBackdoor: Analysis of a New Multiplatform Backdoor

Introduction We have discovered an undetected Linux backdoor which does not have any known connections to other threat groups. VirusTotal detection rate of ACBackdoor Linux variant In addition, we have found Windows variants of the same malware. As is common with most Windows variants, this variant has a higher detection rate than its Linux counterpart. […]
Intezer Analyze Community: GonnaCry, HawkEye, BXAQ and More

In July, Intezer Analyze community detections included GonnaCry ransomware, the HawkEye malware kit, and BXAQ, the spyware that Chinese authorities have been installing onto foreign travelers’ Android devices. 1) GonnaCry [Link to Analysis] GonnaCry is an open-source ransomware designed for the Linux platform. GonnaCry’s source code is downloaded from GitHub and utilized by attackers to […]
Intezer Analyze Community: Mapping Code Connections Between Malware Samples

In addition to highlighting five notable file uploads and endpoint scans made by our community users each month, I thought it was important to visualize the code reuse connections between the malware detected and their respective malware families. The following graphic represents a mapping of file uploads made to the Intezer Analyze community in June […]