How We Escaped Docker in Azure Functions

Summary of Findings What is Azure Functions? Technical Analysis Proof of Concept Why Does this Matter? Summary of Findings In previous months we identified vulnerabilities in Microsoft Azure Network Watcher and Azure App Services, leading us to investigate other types of Azure compute infrastructure. We found a new vulnerability in Azure Functions, which would allow an attacker […]
A Rare Look Inside a Cryptojacking Campaign and its Profit
Linux threats are becoming more frequent and a more common type of Linux threat is cryptojacking, which is the unauthorized use of an IT system for the purpose of mining cryptocurrency. While cryptominers are well-documented, it’s not often that you get an inside look. It’s rare to see the dashboard of the wallets being used […]
Operation ElectroRAT: Attacker Creates Fake Companies to Drain Your Crypto Wallets

Already with thousands of victims. Intro With Bitcoin on the rise and a market exceeding billions of dollars, cryptocurrency has attracted threat actors wishing to leverage these capitals for their own financial gain. In December, we discovered a wide-ranging operation targeting cryptocurrency users, estimated to have initiated in January 2020. This extensive operation is composed of a full-fledged […]
Early Bird Catches the Worm: New Golang Worm Drops XMRig Miner on Servers

In early December, we discovered a new, undetected worm written in Golang. This worm continues the popular 2020 trend of multi-platform malware developed in Golang. The worm attempts to spread across the network in order to run XMRig Miner on a large scale. The malware targets both Windows and Linux servers and can easily maneuver from one platform […]
A Zebra in Gopher’s Clothing: Russian APT Uses COVID-19 Lures to Deliver Zebrocy

Summary In November, we uncovered COVID-19 phishing lures that were used to deliver the Go version of Zebrocy. Zebrocy is mainly used against governments and commercial organizations engaged in foreign affairs. The lures consisted of documents about Sinopharm International Corporation—a pharmaceutical company that COVID-19 vaccine is currently going through phase three clinical trials—and an impersonated evacuation […]
Stantinko’s Proxy After Your Apache Server
Intro It is common for threat actors to evolve their Linux malware. BlackTech with their new ELF_PLEAD malware and Winnti’s PWNLNX tool are recent examples. On par with this trend, we have discovered a new version of a Linux proxy trojan related to Stantinko group. The malware has just one detection in VirusTotal at the time of this publication. […]
VB2020 – Advanced Pasta Threat: Mapping Malware Use of Open Source Offensive Security Tools

The term Offensive Security Tool, also known as OST, is a controversial subject within the InfoSec community. It often sparks fierce debate with both sides of the argument weighing in on how the uncontrolled publication of offensive security capabilities should be treated. On one side of the argument, typically held by more defense-oriented people, the free […]
The Evolution of APT15’s Codebase 2020
The Ke3chang group, also known as APT15, is an alleged Chinese government-backed cluster of teams known to target various high-profile entities spanning multiple continents. Examples include attacks on European ministries, Indian embassies, and British military contractors. The group’s activities have been traced back to 2010 and it is known to boast a large number of […]
Kaiji: New Chinese Linux malware turning to Golang

It is not often that you see a botnet’s tooling written from scratch. The Internet of things (IoT) botnet ecosystem is relatively well-documented by security specialists. New threat actors are generally discovered quickly due to the inherent noise caused by DDoS operations, both in terms of infecting new machines and conducting operations. Simply, it is difficult to […]
TTPs matrix for Linux cloud servers
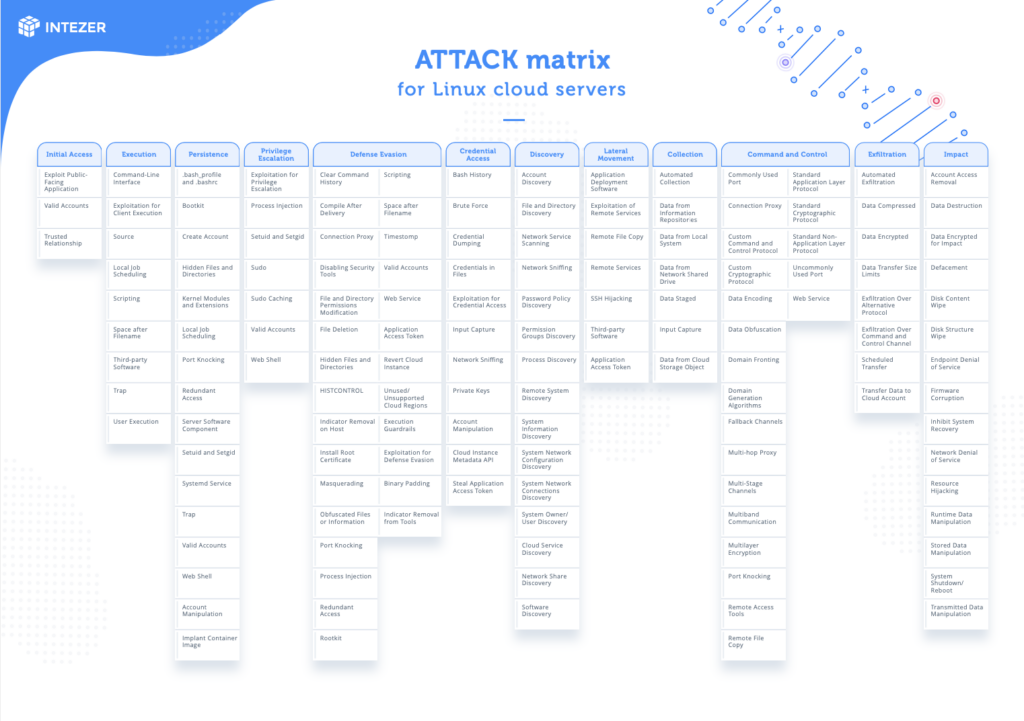
Checklist for protecting your Linux cloud servers against cyber attacksTaking inspiration from the MITRE ATT&CK® framework, we have developed a matrix categorizing adversary tactics and techniques for Linux cloud servers. We believe this is significant because Linux cloud servers are common in modern production environments.The MITRE Corporation is doing tremendous work assembling a global knowledge base […]