TL;DR – Intezer’s Autonomous SOC is transformative for phishing email investigations
Phishing attacks are increasingly sophisticated, making quick and accurate triage essential. Intezer’s Autonomous SOC fully automates the first-level analysis of reported phishing emails by evaluating links, attachments, QR codes, headers, email body — using multiple technologies analysis engines, including AI as a core component. This process delivers a clear verdict on each email, highlighting which reported emails require escalation and which are likely benign. Enabling security teams to focus on real risks without delay.
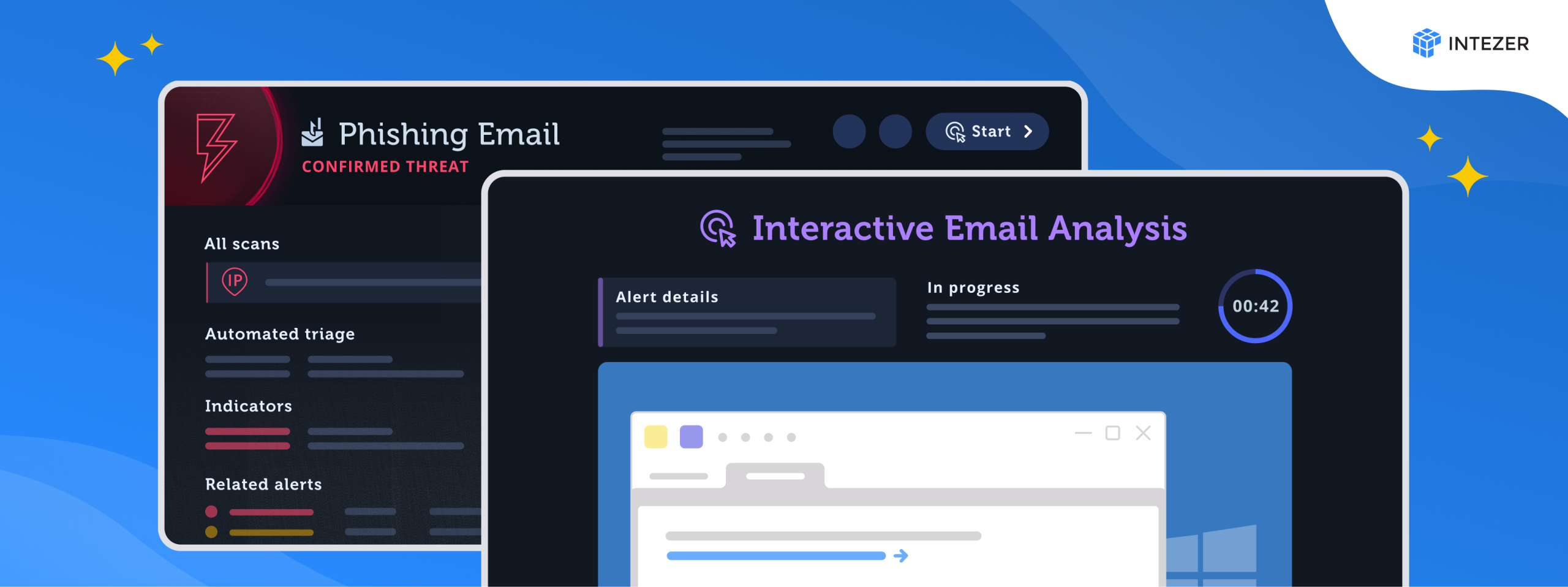
One-Click Access to Secure Interactive Analysis: A Natural Next Step for Phishing Email Investigations
After initial triage, an analyst often needs to dive deeper into specific phishing alerts to fully understand the scope and intent of the attack. Intezer already allows users to interact with individual links and files, but this new capability now extends that interaction to the entire email itself in a secure, sandboxed environment. With a single click, analysts can open suspicious emails, explore embedded elements, and monitor behavior in real time, all without leaving the platform. This smooth transition from automated triage to in-depth analysis enriches investigations and maintains an efficient workflow.
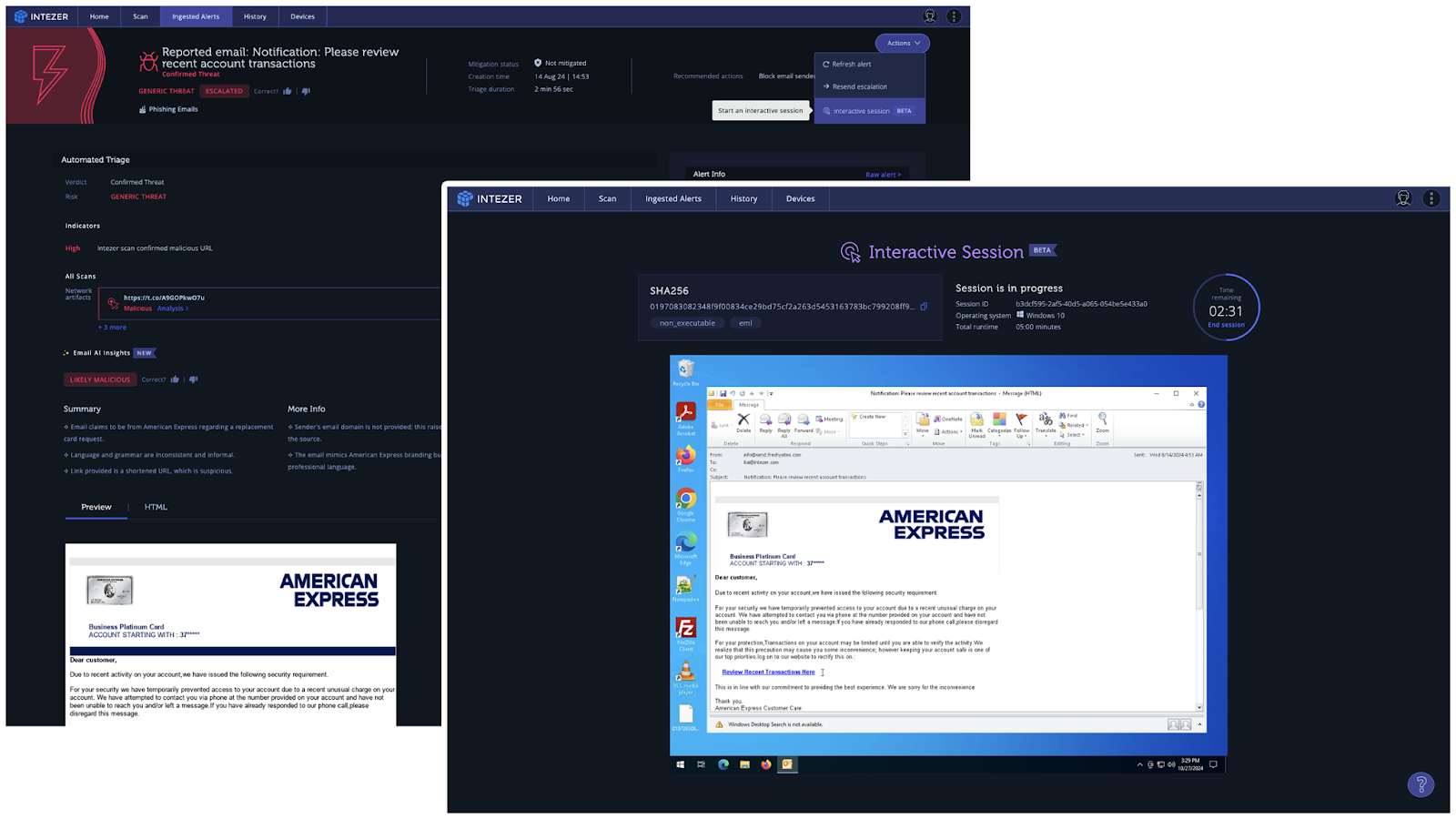
Why Interactive Analysis Matters
Interactive analysis provides a complete view of complex phishing attempts, especially when uncovering hidden IOCs and understanding attack intent. Advanced phishing attacks may use elements that only activate during interaction, which can reveal additional IOCs critical to comprehensive threat intelligence. This capability enriches the overall investigation, giving analysts deeper insights and equipping them to create better detection and defense strategies.
Combining AI Automation with On-Demand Analysis Tools
In line with Intezer’s commitment to tackling the resource and talent shortages impacting today’s security teams, we aim to not only fully automate Level 1 SOC tasks—escalating only genuine threats—but also equip analysts with the on-demand tools they need for deeper investigation when necessary. This balanced approach enhances the SOC’s efficiency by enabling analysts to swiftly conduct advanced investigations on escalated alerts. By combining intelligent automation with powerful analysis capabilities, Intezer empowers organizations to maximize the value and impact of their security teams.
Conclusion
Intezer’s one-click, interactive phishing investigation capability within a sandboxed environment transforms the depth and efficiency of phishing investigations. By combining automated triage with secure, hands-on analysis, security teams gain more actionable insights and a stronger understanding of phishing threats—helping protect their organization against evolving attacks.