I am pleased to highlight the new integration between Intezer Analyze™ and IBM Resilient. The integration enables users of both platforms to enrich their incident response with unique information gleaned from Genetic Malware Analysis technology, including code and string reuse, malware family classification and threat actor attribution.
As a result, incident responders will be better positioned to automatically reduce false positives and quickly detect and respond to a greater number of cyber threats, at scale.
Benefits include:
- Automatically analyze suspicious files attached to an incident using Genetic Malware Analysis
- Reduce false positives
- Enrich malicious verdicts with unique context such as malware classification, to assess the intent and sophistication level of threats and better prioritize and tailor the response
- Significantly reduce investigation and response time
How it Works:
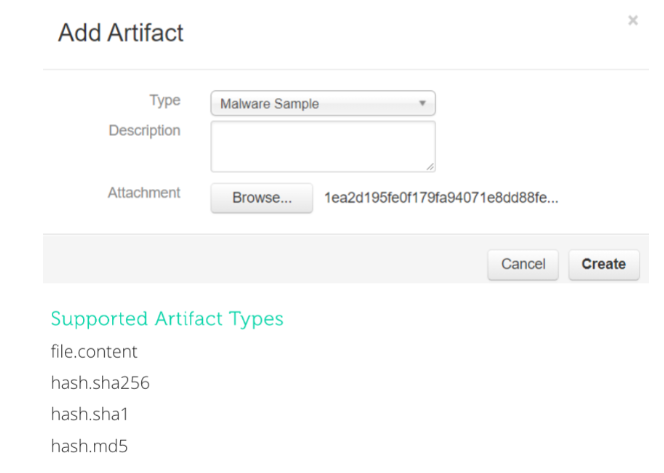
- As part of the incident response cycle, a suspicious file or hash related to an incident is submitted as an artifact through IBM Resilient.
- IBM Resilient will query Intezer Analyze for scanning the submitted artifacts in order to provide additional information about the suspected file or hash.
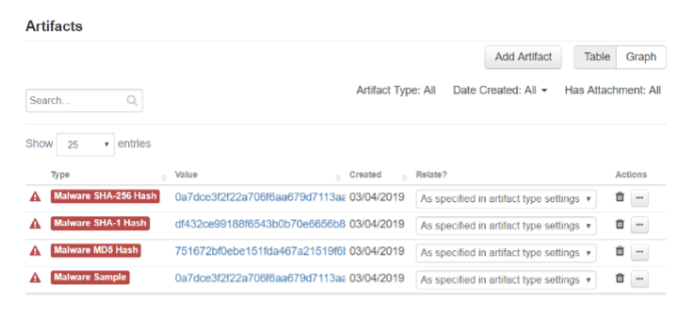
- Intezer Analyze will dissect the file or hash into tiny pieces of binary code. Detecting code reuse to known legitimate and malicious software, Intezer Analyze will provide a trusted or malicious verdict. If the verdict is malicious, the user will receive a hit in IBM Resilient (see screenshot below).
- The hit will include a link to the full analysis located within the Intezer Analyze platform, providing information such as code and string reuse, malware family classification and threat actor attribution. The information provided from the analysis can help users better understand the sophistication level of the threat.
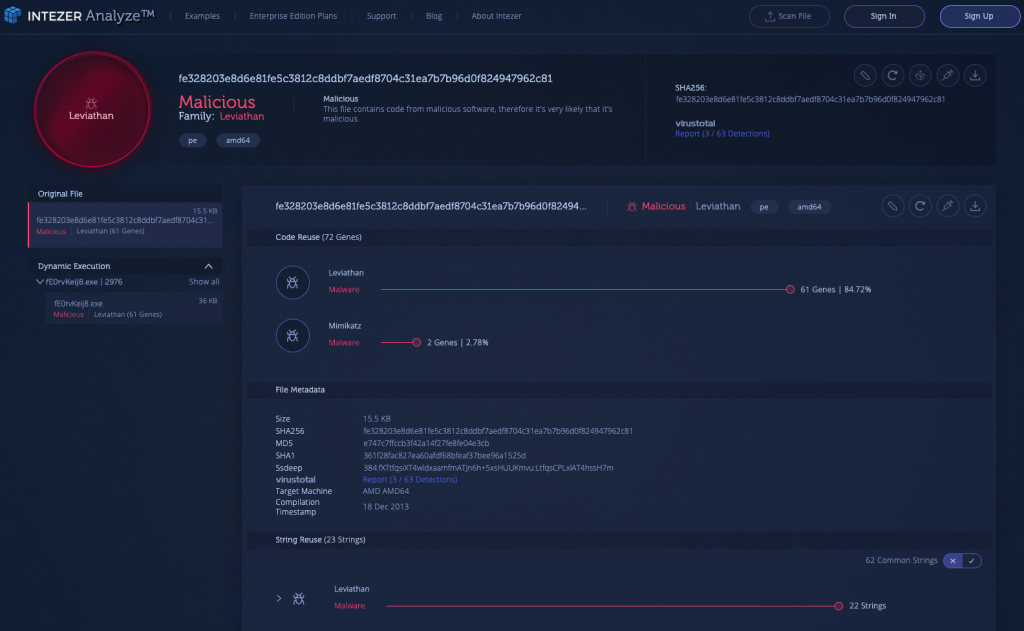
Below is an example of an Intezer Analyze analysis which classified a malicious file as a variant of Leviathan. Also known as TEMP.Periscope, Leviathan is a cyber espionage group with alleged Chinese origins. This group has been active since at least 2014, targeting a wide range of organizations, including engineering firms, universities and government agencies globally. This threat usually propagates through spear phishing campaigns, including vulnerable Microsoft word and excel documents.
The sample shows a strong connection to Leviathan based on both code and string reuse, and it also contains two Mimikatz genes, which potentially indicates usage of the popular credential stealer.
Incorrectly responding to an incident can be detrimental. This is why classifying malware is important for security teams to understand how to appropriately tailor their response. The right context is crucial for understanding the intent and sophistication of the threat, and in turn will help to dictate the appropriate response path. Understanding if a threat is a generic malware, banking trojan or a nation-state sponsored attack, for example, will help users assess the intent and scale of the attack in order to more effectively tailor the response.
- Joint IBM Resilient and Intezer Analyze enterprise users can generate automatic code-based YARA signatures in order to understand the scale of the attack—for example, how many hosts were infected—and to detect future variants of the malware and new forms of malware that reuse portions of the same code.
The integration is available in the IBM Resilient App Exchange. For more information please visit https://exchange.xforce.ibmcloud.com/hub/?q=intezer or contact partners@intezer.com. Please note that you need to be logged into the application in order to view the full integration details.