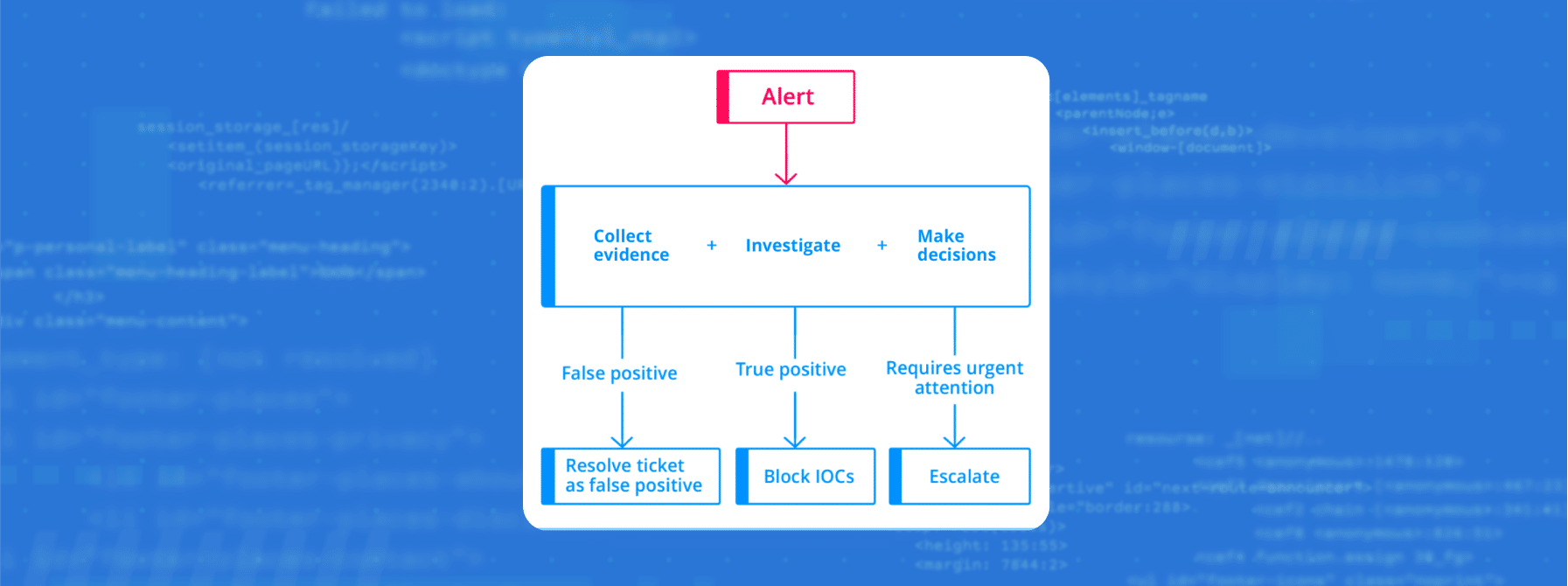
Quick and accurate responses to threats are essential for cybersecurity teams. SOAR playbooks provide structured workflows to handle common security incidents. However, as automating with SOAR has its limitations, there’s a clear need to enhance these playbooks with powerful third-party tools.
Intezer’s AI-powered solution integrates with SOAR tools to supercharge your incident response playbooks. By automatically investigating threats, extracting and analyzing evidence, and providing clear recommendations, Intezer can improve and simplify the decision-making process in your SOAR playbooks. In this post, we’ll discuss how integrating Intezer’s artificial intelligence-drive platform can make these playbooks more effective and efficient.
Let’s dive into some examples of SOAR playbooks your SOC team can simplify, while using AI to accelerate incident response time.
3 Examples of Better Incident Response Playbooks
1. Phishing Email Response Playbooks
Phishing attacks remain one of the most prevalent cybersecurity threats. They prey on human vulnerabilities, making them particularly challenging to counteract. Traditional SOAR playbooks for phishing response focus on automating tasks. That could include verifying suspicious emails, extracting indicators of compromise (IOCs), blocking malicious URLs or domains, and removing phishing emails from user inboxes.
However, the sheer volume of phishing attempts and the increasing sophistication of these attacks can overwhelm the most robust playbooks. Increased awareness from employees about phishing attacks can also result in waves of “suspicious” emails reported to the security team to investigate. (Often after a new phishing training program for employees, or a high-profile cyber attack.) This is where Intezer’s AI-driven decision making comes into play.
With Intezer’s capabilities, you can auto-investigate phishing emails. This streamlines the initial assessment process. Analysts don’t have to manually sift through every alert about a new reported phishing email anymore. Intezer can automatically extract evidence from the email, including URLs, body content, metadata, and attachments, and then analyze them. This not only speeds up the average response time but also ensures a more thorough and accurate assessment.
By leveraging Intezer’s AI recommendations, you can also enhance SOAR playbooks to take more precise automated actions. For instance, if Intezer identifies a sender or domain as malicious, the playbook can block it automatically, reducing the window of exposure.
In essence, by integrating Intezer’s decision-making data, the phishing response playbook becomes more proactive. This reduces the burden on SOC teams and ensuring that you only escalate emails that truly require attention. This results in a more efficient and effective response to one of the most persistent cyber threats. Read more about Intezer’s automated phishing investigation process.
2. Endpoint Alert Triage Playbooks
Endpoint Detection and Response (EDR) systems are critical in identifying and managing threats at the endpoint level. They generate alerts based on suspicious activities, and while these alerts are invaluable, the sheer volume can be daunting. Manually triaging these alerts is not only time-consuming but can also lead to human errors, potentially overlooking genuine threats or misclassifying benign activities.
Integrating Intezer’s decision-making data can significantly streamline the EDR alert triage process. Here’s how:
- Automated Evidence Extraction and Analysis: Intezer can automatically extract and analyze evidence associated with EDR alerts. Whether it’s a file, a process, or even memory scanning for more ambiguous alerts like “Suspicious Activity”, Intezer can provide a comprehensive initial assessment. This reduces the time spent on manual investigations and ensures a consistent analysis approach.
- Actionable Recommendations: Based on its analysis, Intezer provides clear recommendations. These can be directly integrated into the SOAR playbook to dictate automated actions. For instance, if an alert is verified as malicious, the playbook can automatically isolate the affected machine, notify specific team members, or even reset user credentials.
- False Positive Reduction: One of the challenges with EDR systems is the occurrence of false positives. By utilizing Intezer’s AI assessment, SOAR playbooks can automatically resolve alert deemed benign. This ensures that security teams focus only on genuine threats.
Incorporating Intezer’s decision-making data into the EDR alert triage process not only makes it more efficient but also more accurate. It ensures that every alert gets the attention it deserves, optimizing the use of resources and enhancing the overall security posture. Read more about leveraging Intezer’s alert triage assessments into SOAR playbooks.
3. SOAR Playbooks to Scan Files and URLs
In cybersecurity, rapid and precise analysis of suspicious files and URLs is essential, and is often used in many different kinds of SOAR playbooks. Here’s are some examples of how Intezer can enhance your playbooks that require conducting this kind of analysis:
Automating Analysis for a High Volume of Files
When a file is flagged as suspicious, its nature and intent still need to be determined. Intezer uses genetic code analysis to compare the file’s code with a database of known software. This helps in quickly identifying if the file shares code with known threats or benign software. In addition, Intezer uses a variety of more common techniques to scan files: sandboxing, reputation checks, static analysis, and more. For novel malware that contains never-before-seen code, Intezer’s comprehensive analysis abilities help you to quickly understand the capabilities, potential threat, and how you should respond.
By integrating Intezer into this SOAR playbook, flagged files can be sent to Intezer for immediate analysis. The results, which include the file’s risk level and any associated malware family, can also guide automated responses.
URL Analysis Beyond Blacklists
Traditional blacklists of malicious domains have their limits. New malicious domains are created regularly, and sometimes legitimate domains are compromised. Intezer goes beyond just checking a list. It analyzes the content associated with a URL using machine learning and other techniques to determine if it’s malicious.
For example, a URL might lead to a malicious file download. Intezer can automatically retrieve and analyze this file. If a URL is hosting content that shares code with known phishing schemes, Intezer will identify this. In addition, Intezer already does the heavy lifting of analyzing the URL with a variety of techniques, including reputation checks, generative AI to inspect the content, scanning in well-known 3rd party services (urlscan.io, APIVoid, …), and many other proprietary heuristic checks.
By adding Intezer’s capabilities to the SOAR playbook, URLs can get checked in real-time. If a URL is found to be malicious, the playbook can take automated actions, such as blocking the domain or sending out alerts. For scanned URLs that need more investigation, you can trigger a notification to your team to conduct an investigation of the website using a secure interactive browsing session.
Incorporating Intezer’s file and URL analysis into the “Scan files and URLs” playbook streamlines the process, making it more efficient and effective. This allows security teams to focus on other tasks, knowing that the initial analysis is being handled accurately and promptly, no matter how many files and URLs you need analyzed.
Smart Decision Making + Playbooks = Less Work for You
Integrating Intezer’s Autonomous SOC capabilities into these three pivotal SOAR playbooks — Phishing Response, Endpoint Alert Triage, and Scan Files and URLs — has showcased the power of combining intelligent decision-making with orchestrated security actions. Intezer’s alert triage and decision-making data mimic human-like discernment, ensuring accurate threat identification and response. When paired with SOAR’s ability to seamlessly coordinate various security tools, the result is a significant reduction in workload for SOC and security teams. This synergy ensures a more efficient, informed, and proactive approach to cybersecurity challenges.