A complete walkthrough of how the Autonomous SOC Platform works, automating your incident response process with artificial intelligence to make your team more efficient and effective.
As technology and artificial intelligence rapidly advances, the cybersecurity industry faces significant challenges. Rising alert volumes from SIEM tools, endpoint security products, and user-reporting phishing inboxes. A growing shortage of skilled professionals. More threats, not enough time to respond. As the complexity and volume of threats increase, the demand for expertise in security operations far outstrips the available supply. This is where we designed Intezer to step in. Our AI-powered Autonomous SOC Platform fully automates SOC Tier 1 processes for incident investigations, triage, and response to effectively augment your team’s capabilities.
I wrote this article to provide a technical overview of how our AI-driven platform works. From monitoring to reporting, Intezer automates functions traditionally handled manually by a Security Operations Center (SOC) team or outsourced service provider. I’ll delve into each stage of Intezer’s incident response process, explaining how we collect and analyze data with AI, how we determine the risk level of each alert, and how we respond to confirmed threats. By the end, you’ll have a comprehensive understanding of how Intezer works to keep your organization secure and team members happy.
Table of contents
- The Future of AI-Powered Autonomous SOC for Security Teams
- How the Autonomous SOC Platform Mimics Expert Security Analysts
- 1. Alert Monitoring by Intezer 24/7
- 2. How Intezer Automatically Collects and Extracts Evidence
- 3. Investigating Incidents with AI
- 4. Automating Triage Decisions for Incident Response
- 5. Responding to Confirmed Threats
- 6. Reporting on Automated Incident Response
- How Intezer is different from Incident Response Playbooks
- Learn more about the AI-Powered Autonomous SOC Platform
The Future of AI-Powered Autonomous SOC for Security Teams
Let’s be clear about one thing — Autonomous SOC isn’t about replacing your team, it’s about extending your team. It’s about maximizing incident response automation, using technology that can operate without constant intervention and interaction (aka “autonomously”). This approach allows your team to do more with the resources you have and focus on the serious, escalated threats.
Many companies rely on outsourced SOC providers these days, but incident response automation with Intezer’s AI-powered technology reduces the need for such services or replaces them. SOC automation with AI is also more affordable than such service providers. At the same time, it ensures an organization’s security operations are efficient and effective at handling evolving and advanced threats.
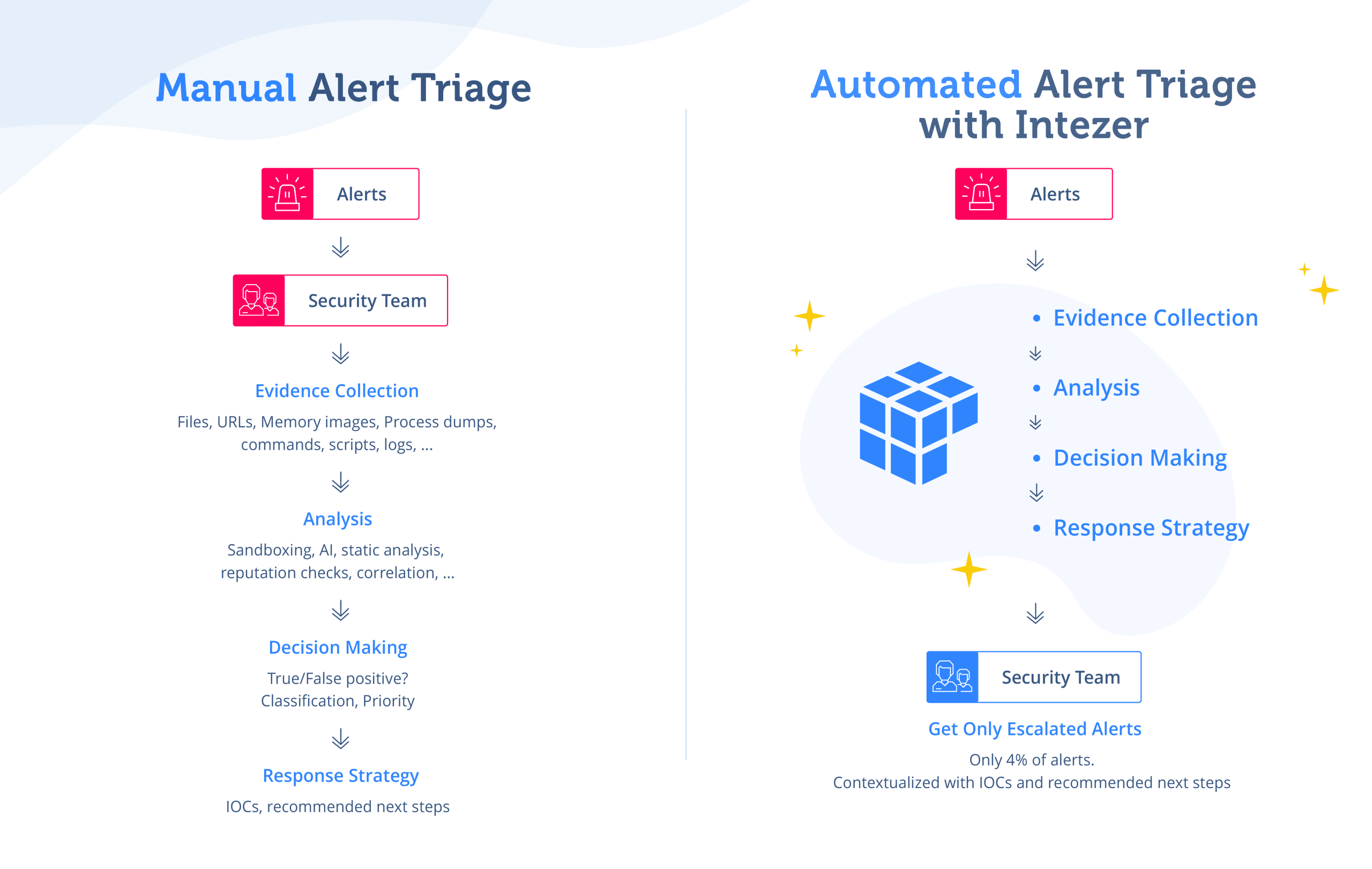
How the Autonomous SOC Platform Mimics Expert Security Analysts
Our Autonomous SOC platform is designed to mimic the actions of an expert human analyst. Intezer collects as much evidence as possible, then uses AI to conduct thorough investigations and make informed decisions based on the data. By automating these processes, we allow your security team to focus on their core responsibilities, using AI to improve efficiency and effectiveness. All without requiring you to build custom workflows or complicated playbooks.
5 Stages in the Autonomous SOC Process
To provide a clear understanding of how Intezer works, here’s a high-level overview of our five-stage process:
- Monitor – Intezer continuously monitors and collects alerts 24/7 from your integrated security tools, ensuring that no potential threat goes unnoticed.
- Collect Evidence – Upon receiving an incoming alert, Intezer collects all relevant data associated with the alert. That includes files, processes, command lines, evidence from process arguments, URLs, IPs, parent and child processes, memory images, and even getting feedback from the end-user.
- Investigate – Intezer analyzes each piece of collected evidence using AI and a variety of sophisticated techniques. That includes LLMs, generative AI, sandboxing, genetic analysis, static analysis, open-source intelligence (OSINT), memory analysis, and reverse engineering.
- Triage – Intezer uses private AI models to simulate the decision making process for the bottom-line verdict for the entire alert, taking into account all the investigation results. The bottom-line verdict includes categorizing the risk associated with each alert and decides whether to escalate it or not. In addition, Intezer reduces noise by auto remediating false positives within your detection systems, since these require no other action.
- Respond – For confirmed threats, Intezer provides assessments and recommendations. These include detection content and ready-to-use hunting rules to guide the response process. Intezer also can conduct automated deeper memory forensics if needed, to triage additional endpoints.
- Report – Intezer generates reports to keep your team informed about the alert triage process, including statistics, tuning suggestions and more — allowing for continuous improvement in your security operations.
By automating these processes, Intezer enhances the effectiveness of your security team. The efficiency gains can make a significant impact on Mean Time to Respond (MTTR). If you’re interesting in how our platform uses artificial intelligence, you can read about Intezer’s AI Framework here.
1. Alert Monitoring by Intezer 24/7
The Autonomous SOC platform connects directly to your alert sources via API Key or plugin. Within the same hour, Intezer starts automatically monitoring ingesting alerts 24/7. This ensures a seamless and immediate integration of our system with your existing security infrastructure.
Intezer support triaging alerts from multiple sources:
- Endpoint security products (including CrowdStrike, SentinelOne, and Microsoft Defender)
- SIEM tools (Splunk, Sumo Logic, Microsoft Sentinel, Elastic SIEM, and more)
- User-Reported Phishing Pipelines (via Microsoft Office 365, Google Workspace, or Proofpoint abuse inboxes or Sublime Security detection rules)
- SOAR tools (Tines, Cortex XSOAR, Splunk SOAR, and more)
Endpoint and SIEM tools are widely used and often generate the highest volume of alerts for a SOC to analyze. Intezer monitors ALL types of alerts, including fileless threats and alerts that are based on suspicious activity. For endpoint security tools, Intezer pulls the alerts directly using their APIs to ensure real-time, accurate data for analysis.
To triage reporting phishing emails, Intezer can monitor connected inboxes like from Microsoft Office 365, Google Workplace, or Proofpoint. We also connect with Security Orchestration, Automation, and Response (SOAR) tools through a dedicated app in each of those vendors’ marketplace to collect suspicious emails or other alert types.
Since Intezer and SOAR tools use different kinds of automation, they can be used together very effectively. Intezer can allow security teams to simplify playbooks (some may even be entirely replace) or automate even more processes, by combining an existing SOAR tool with powerful automation from Intezer. Currently, we support Splunk Phantom, XSOAR, and Chronicle (previously Siemplify). Connecting via SOAR allows our users to leverage Intezer’s decision-making and analysis capabilities for a wide range of custom alert sources and playbooks, like the investigation of suspicious emails and employee-reported phishing.
Through the smart combination of Intezer with your existing security tools, your team should be able to automate much more of your incident response process. We are also committed to expanding Intezer’s integration capabilities to meet your evolving security stack.
2. How Intezer Automatically Collects and Extracts Evidence
Once Intezer detects an alert, the next step is collecting evidence and all relevant data. This process mirrors the actions an expert human analyst would take. The goal is to collect as much evidence as possible to provide a comprehensive view of the potential threat.
The types of evidence Intezer collects are wide-ranging and thorough. They include files, processes, command lines, evidence from process arguments, URLs, parent and child processes, memory images, and more. As a SOC analyst would, Intezer extracts evidence related to the incident whether it is a fileless PowerShell-based ransomware attack, or a obfuscated malicious file. This extensive collection of evidence allows Intezer to gain a deep understanding of the alert and any potential threat.
We collect this evidence using the API of the security tool that fired the alert and the API of the endpoint security tool. This approach allows us to gather both textual information from the raw alert data, such as IPs/URLs, and actual artifacts from the endpoint, such as files and processes.
It’s important to note that the automatic collection of many artifacts from endpoints is a complex task. It requires sophisticated engineering to handle edge-cases, reduce duplicates, and more. However, at Intezer, we have invested heavily in developing the capabilities to carry out this task effectively and efficiently. This ensures that our platform can provide the most comprehensive and accurate analysis of each alert, allowing your security team to respond effectively to each potential threat.
3. Investigating Incidents with AI
The investigation stage is where Intezer’s AI Framework truly shines. Analyzing evidence is a critical part of our incident response process, where the goal is to assign a verdict (true/false positive), risk level, and recommended next steps for each alert. This is achieved by conducting a thorough investigation of each piece of evidence separately. Intezer assigns a verdict (malicious, trusted, and others) and classification (malware family, threat actor, or software vendor in case it is trusted) for each individual piece of evidence.
Each individual artifact is analyzed using a variety of sophisticated techniques and artificial intelligence. All Intezer plans use our proprietary AI models and genetic analysis, sandboxing, static analysis, open-source intelligence (OSINT), memory analysis, and reverse engineering. These techniques allow us to gain a deep understanding of the behavior of the threat, its origin, and its potential impact.
Once all individual pieces of evidence have been analyzed, we generate an assessment for the entire alert. This takes into account the investigation results of multiple pieces of evidence. We use smart machine learning models and AI algorithms to create this summary of all individual analyses into a coherent incident-wide verdict, risk level, and recommended next steps.
The alert investigation summary can be seen either in Intezer’s alert report, inside your connected security tool that fired the alert, or alternatively via our API.
This approach makes it easy for the user to understand the overall assessment while still enabling the user to dig into each individual artifact and explore why exactly we came to a certain conclusion. By providing both a high-level overview and detailed analysis, we ensure that your security team has all the information they need to respond effectively to each potential threat.

4. Automating Triage Decisions for Incident Response
This triage stage is where we determine the appropriate response, based on the risk level determined in the investigation stage. Here Intezer decides whether an alert should be escalated or automatically remediated as a false positive.
Escalated Incidents
Escalated alerts are those that our platform identifies as requiring further attention. They are unmitigated, confirmed threats which now require human intervention. Threat escalations can be sent as notifications via email or any other webhook-supported system, as described in our documentation. The notification method is configurable by the user, allowing for seamless integration with your existing SOAR playbooks or ServiceNow security operations workflow.
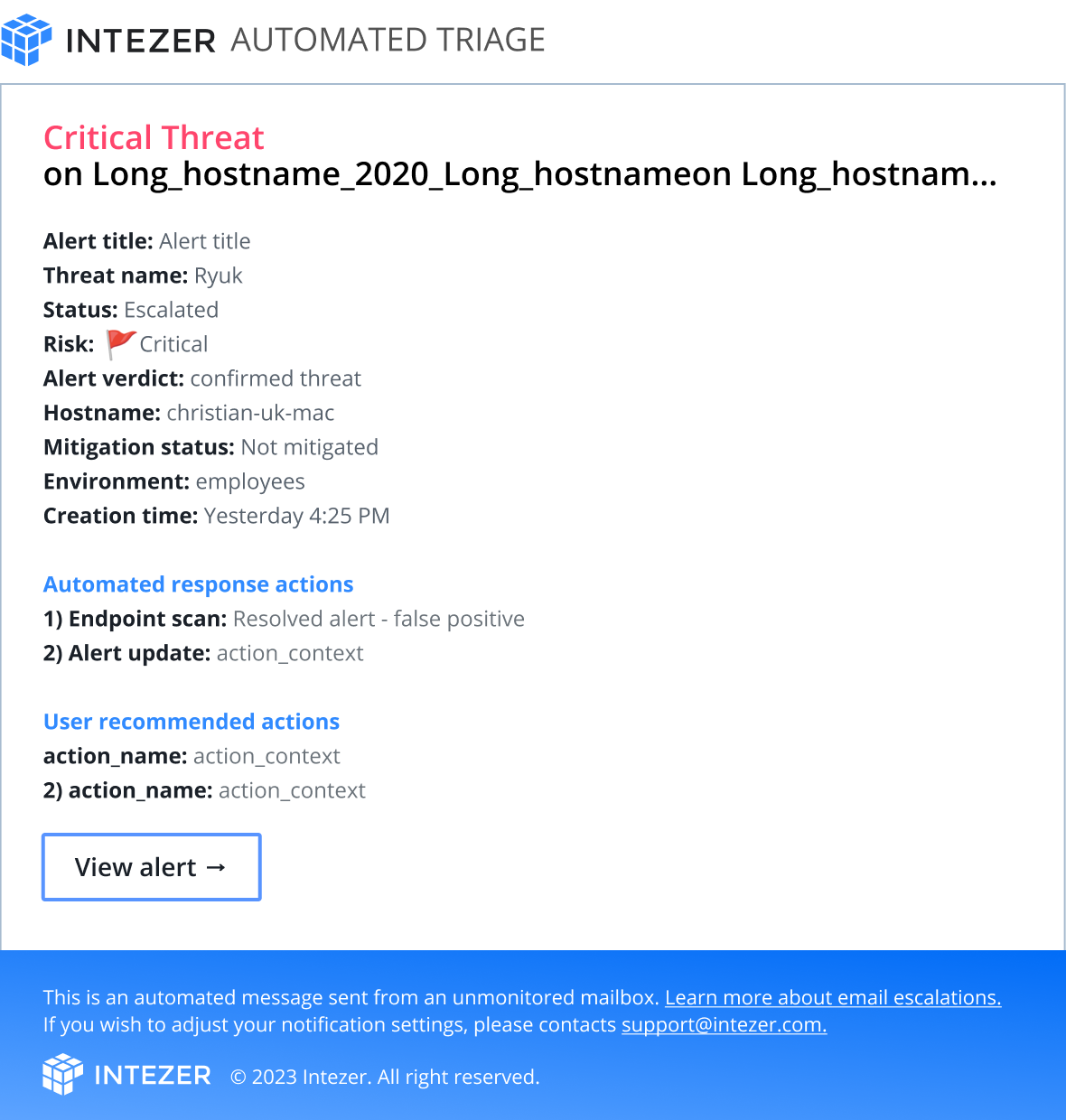
The decision to escalate an alert is not made lightly. It combines both Intezer’s sophisticated algorithm and the user’s configuration to suit the security team’s policies and workflows. Our algorithm takes into account both the investigation results done by Intezer as well as information from the security tool that originally fired the alert, to ensure maximum efficacy. For more information on how we handle incident escalations, please refer to our dedicated article about Threat Escalations.
Benign and False Positive Alerts
Intezer’s unique technology for analyzing code reuse can provide critical information that allows it to accurately determine false positive alerts. As these require no further action, alerts that are determined to be false positives can be automatically resolved by Intezer via the integrated tool that originally fired the alert. This feature is designed to reduce noise and ensure that your security team can focus on the alerts that truly matter. By automating this process, we save your team from time wasted on false positives and too many escalated alerts.
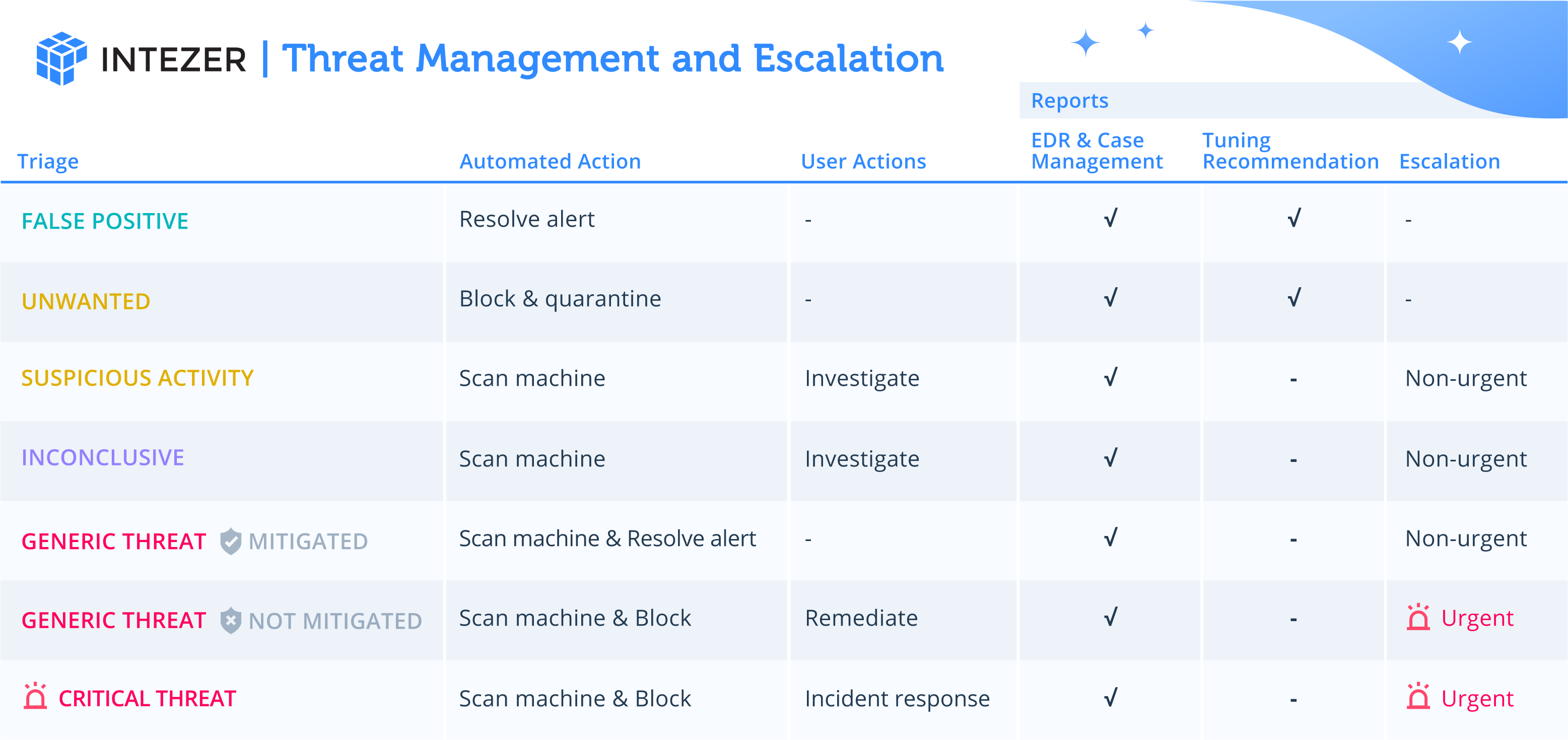
5. Responding to Confirmed Threats
The response stage is all about taking action. Based on the recommended next steps determined in the investigation stage, Intezer acts to mitigate the potential threat.
The possible responses can vary depending on the nature of the threat and the recommended next steps. They can include conducting deeper forensics on the endpoint, applying Indicators of Compromise (IOCs) and other hunting rules, or other recommended next steps that are based on industry best practices.
In this stage, Intezer leverages your integrated security tools to carry out these actions. For example, using your endpoint security tool, Intezer can remotely execute its memory scanner to conduct deeper forensics on a suspicious endpoint, if needed. This is a valuable feature for detecting fileless attacks and traces of in-memory threats. Intezer’s memory scanner allows us to automatically gather more information about the threat for you and develop a more effective response.
Looking ahead, we are working on expanding our response capabilities to automatically apply IOCs and hunting rules directly to your security tools. This will further streamline the response process, allowing your security team to respond to threats more quickly and effectively.
6. Reporting on Automated Incident Response
The final stage in our process is reporting. Intezer generates weekly Autonomous SOC Reports to keep your team focused on what matters most and provide tuning suggestions. These reports provide a clear and concise summary of all the threats detected and actions taken during the week, allowing your team to easily track progress and adjust strategies as necessary.

How Intezer is different from Incident Response Playbooks
While some tasks in Intezer’s six-step incident response process can be automated with SOAR playbooks or other security automation products, there are several key differences that set Intezer’s Autonomous SOC solution apart.
First, most tasks in traditional incident response playbooks still require significant human involvement due to the decision-making needed. This includes deciding if an alert is a false positive or not, when to escalate, and more. Intezer’s AI-powered platform on the other hand uses sophisticated algorithms to make decisions like an experience SOC analyst, reducing the need for human intervention.
Second, truly automating SOC Tier 1 triage requires heavy custom engineering to create production-ready playbooks. For example, collecting a variety of evidence from actual endpoints, while addressing many edge-cases, is a challenging task to develop. Intezer has invested heavily in this area, developing capabilities that can handle these complex tasks effectively and efficiently.
Third, even if you manage to do the required complex engineering, you often end up with large playbooks that are hard to maintain and keep up-to-date. This includes the need to maintain licenses and up-to-date logic of numerous third-party products to help automate the alert triage process for incident response, including a sandbox, URL scanner, reverse engineering platform, reputation databases, and more. Intezer’s platform, however, is designed to function as an all-in-one analysis platform for incident response, using AI to reducing the burden on your security team.
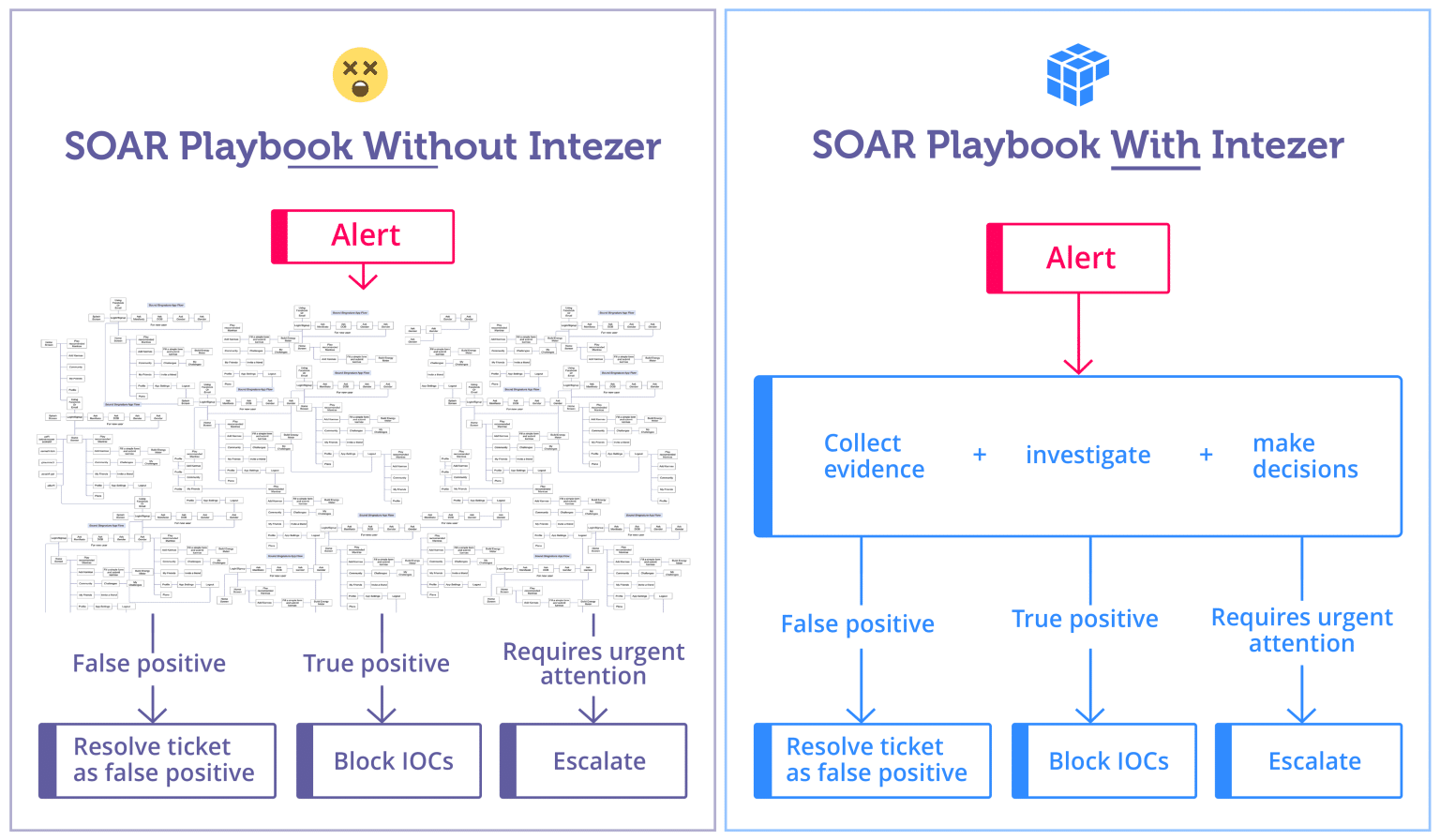
Want to know more about the difference between Intezer and SOAR platforms? Check out our blog here to learn about how Intezer and SOAR tools can work together in a complimentary way.
Learn more about the AI-Powered Autonomous SOC Platform
Discover how Intezer can help you automate alert triage and decision-making processes for security alerts — schedule your demo now. Our expert team can answer your questions about how Intezer can use AI to make your security operations even more effective and efficient.




