With a free account, you get a trial of Intezer’s Autonomous SOC capabilities and ongoing access for advanced malware analysis. In the first two weeks after creating your free account, you get up to 500 automated scans for analysis, alert triage, and incident response so you can test out everything Intezer Autonomous SOC can do. After the trial ends, you’ll get 10 public, on-demand file scans for malware analysis every month.
In 2017, we were thrilled to launch the first free “community edition” of Intezer for malware analysis. Today, while you can still use Intezer to analyze suspicious files for free, our technology has matured and evolved far beyond the scope of malware analysis into our Autonomous SOC solution.
Getting the Most Out of Your Free Intezer Account
When you look at how Intezer works now, you can still see where malware analysis fits into Intezer’s investigative processes (step 3 in the image below). But now Intezer’s automated capabilities for alert monitoring, collecting evidence, triage, and incident response go far beyond just malware analysis.

These days, free Intezer users get 10 public file scans every month for malware analysis, but you also get a 2-week trial of the Autonomous SOC capabilities so you have time to test it all out. (If you’re looking for a deeper proof-of-concept of the Autonomous SOC plan without the 14-day limitations, all the capabilities, and closer support from one of our solution engineers, book a demo to talk with us.) The trial period includes privacy for up to 500 automated scans, with features for scanning live endpoints as well as analyzing emails, memory dumps, URLs, and other supported file types.
If you’re looking to make the most our of your trial period then you’ll need the API keys for any security tools that you want to connect, so you can see how Intezer triages alerts from those sources. Connecting a new alert source takes just a few minutes, then Intezer can start monitoring, investigating, and triaging those alerts for you. Often, these are the kinds of tasks that can overwhelm security teams or have to get outsourced to Managed Detection and Response (MDR) providers. With Intezer, you get deeper analysis and visibility about every alert almost instantly, with only the confirmed and unmitigated threats escalated to your team.
Intezer started out as a plug-and-play, cloud-based solution, with an intuitive web interface and API access. These days, the interface looks a lot different, the API does so much more, and we have powerful integrations for endpoint security platforms (including CrowdStrike, SentinelOne, and Microsoft Defender), reported phishing emails, and SOAR tools that you can try out during the trial.
Looking Back at Intezer’s Origins in Malware Analysis
If you made a free account with Intezer years ago, you’ll remember that Intezer started out by analyzing executable files and then comparing code on a massive scale to a comprehensive database of malicious and trusted software. This unique technology was able to accurately identify and classify WannaCry, Turla, APT17 and APT28. Below, you can see throwback images from 2017, when Intezer’s technology was able to immediately identify a previously undetected APT.

When Intezer analyzes a file or other artifact (whether you upload it to a free account or it’s automatically extracted from an alert) our proprietary technology breaks that executable file into thousands of small fragments, and then compares them to a massive database that contains coding instances within software or malware. That effectively creates a full genetic code mapping of each file leading directly to the “origins” of the threat.
Here’s a simplified graphic we used back in 2017 when we first launched free accounts, showing how Intezer’s core analysis technology works:
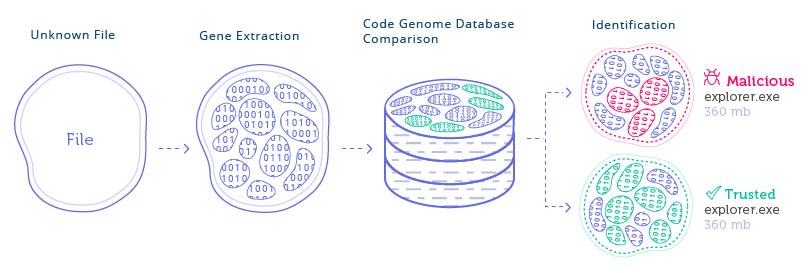
Today, this innovative Genetic Analysis is still at the heart of how Intezer reverse engineers threats to automatically make decisions and take action.
Reverse Engineering Every Threat
Over the years we’ve asked ourselves, what if security teams could go from being stretched thin to having every alert fully investigated? What if Intezer could filter out the noise, handle the grunt work, and make sure human expertise could focus on what really matters?
Could we simulate the processes, thinking, and actions of an experienced security analyst? How could we maximize our technology to automate SecOps tasks, so that it could function like an extension of a security team? How could we make the set up process dead simple?
Intezer was founded by incident team experts, for incident response teams. We understand the major challenges that our security community faces, which years ago led us to build Intezer’s ability to analyze files like a reverse engineer and accurately classify constantly evolving threats. In recent years, as a growing volume of alerts and resource shortages overwhelmed security operation teams, we built more and more features that paired our powerful analysis with automated decision-making and action.
Since we first launched access for free malware analysis, Intezer has changed a LOT.
One thing that hasn’t changed? You can still try out Intezer for free.