Organizations require efficient and effective security operations to protect their digital assets. Security Orchestration, Automation, and Response (SOAR) tools have become popular for streamlining workflows and orchestrating scenarios across multiple systems. However, while the type of automation provided by SOAR tools saves a lot of time hopping between different tools, they fall short when it comes to the critical decision-making and investigation involved in triaging alerts, necessitating additional measures for truly automating security operations.
This is where Intezer kicks in.
Intezer and SOAR tools often work hand-in-hand, enhancing each other’s capabilities to provide an automated SOC Tier-1 / Tier-2 experience.
Automating Triage, Investigation, and Decision-Making
Tools like Splunk SOAR and Cortex XSOAR streamline repetitive tasks by creating custom workflows and playbooks, excelling in orchestrating “if this, then that” scenarios across multiple systems. They are designed to handle repetitive tasks but typically rely on human analysts to manage the intricate triage, analysis, and decision-making involved in responding to security alerts.
However, they lack the native ability to handle the complex triage, analysis, and decision-making processes required to respond to security alerts. This is where Intezer steps in, automating these critical processes and working alongside SOAR tools to enhance the overall security posture of an organization.
Intezer focuses on automating the traditionally human-handled processes of Tier 1 triage, investigation, and decision-making. By leveraging powerful automated analysis to triage various alerts and incidents (such as from endpoint security or email security tools), Intezer fills a gap in many SOAR tools. Intezer only requires the API key of your security tools to start monitoring alerts and investigating threats for your team 24/7 using automated analysis, smart recommendations, and auto-remediation.
How Intezer and SOAR are Different
- With Intezer, you would get every alert deeply investigated to determine if it’s a false positive or not. Intezer would automatically collect many pieces of evidence (files, processes, URLs, IPs, command line parameters, phishing email content, and even memory scans of suspected endpoints) seamlessly from each fired alert. Intezer handles the investigation of fileless threats. All of the above are either impossible or extremely hard to achieve with SOAR, as it would require the custom engineering of huge workflows that would be hard to create and maintain. With a SOAR, you would also need to rely on numerous 3rd party services for analysis, that most likely won’t get the end result you need. For example, a simple hash check in VirusTotal cannot really help drive decisions in most cases.
- With SOAR you could manage and create tickets for your team; create playbooks to automate employee onboarding; propagate IOCs to multiple security tools automatically. Those are things that require workflow-building and case-management capabilities which Intezer does not possess and is not focused on.
The Power of Collaboration
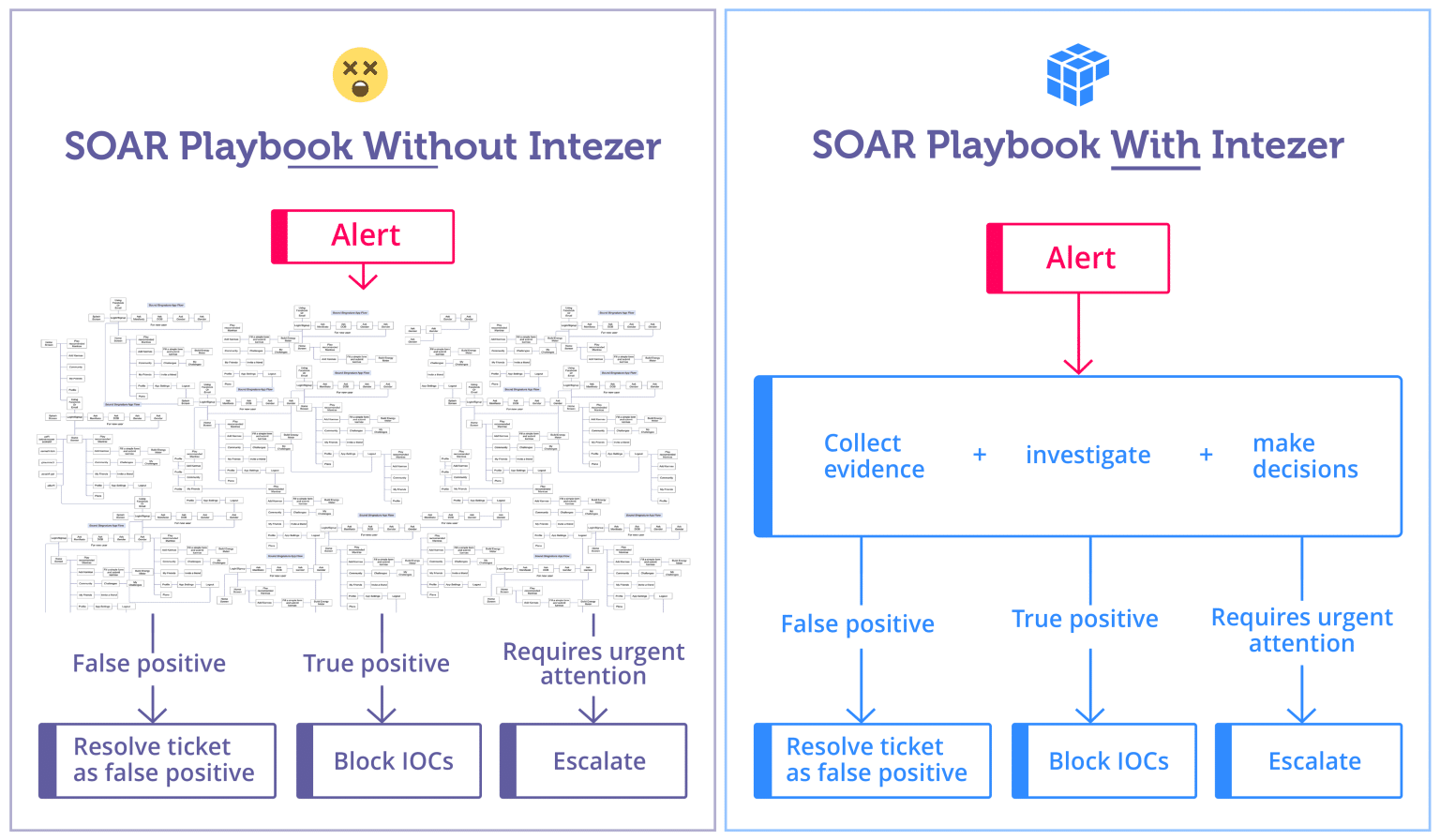
With Intezer, existing and complex SOAR playbooks for automatically triaging alerts can be streamlined to involve fewer steps and tools, while producing higher quality results for incident response teams.
While Intezer and SOAR systems serve different functions, they often complement each other when used together. Intezer’s decision-making and analysis results can be integrated into custom playbooks and workflows within your SOAR tool, enhancing the value of the security team’s investment in SOAR tools. This integration allows for a more comprehensive and efficient security operations process, leveraging the strengths of both systems. (See examples and recommendations about how to incorporate Intezer into your SOAR playbooks here.)
Side-By-Side Comparison of Intezer and SOAR Capabilities
To understand the differences between Intezer and SOAR tools, let’s examine some key features:
| Intezer | SOAR | |
| Primary Function | Automates the investigation, triage, and decision-making processes for security alerts | Automates workflows and playbooks to streamline repetitive tasks |
| Alert Handling | Automated alert triage, monitoring alerts and investigating threats | Does not include the decision-making process required to triage alerts. Relies on 3rd party services to conduct forensic analysis and requires custom engineering to develop real-world alert triage automation |
| Workflow Building | No workflow building except the ability to configure threat escalation processes via email or webhook. | Building highly customized workflows as the primary function |
| Case Management | Escalates alerts and integrates with your existing case management or ticketing system | Often used as a case management system for security teams |
| Integration with Existing Tools | Focuses on endpoint and phishing email alerts. Requires only the API key of your security tools | Typically integrates with multiple systems to create workflows |
| Role in Your Organization | Can serve as an extension of your team, automating a significant portion of SOC/IR workload | Typically serves as a tool to automate repetitive tasks and create custom workflows that in many cases are not related to incident response or alert triage, such as vulnerability management, employee onboarding, and more. |
| Expert Assistance | On-demand expert assistance is available | Does not typically include IR expert assistance |
| Workload for Your Team | Reduced due to automation of alert triage and incident response | Reduced due to automation of repetitive tasks and by eliminating system-hopping, but does not handle alert triage |
| Implementation Time | Typically within a few hours as no custom engineering or configuration is required | Typically long due to the need for custom engineering to create production-ready workflows |
Better SOAR Playbooks for Automated Alert Triage
Intezer and SOAR systems play complementary roles in enhancing an organization’s security operations. While SOAR tools excel at automating repetitive tasks and workflows, Intezer focuses on automating critical triage, analysis, and decision-making processes. By integrating these systems, organizations can achieve a more comprehensive and efficient security operations process, leveraging automation, analysis, and expert assistance.
Contact us today to learn more about how we can help you automate your alert triage and decision-making processes for security alerts.




