After launching Intezer community edition in November 2017, we noticed that many of our users uploaded packed samples. Yet packed files don’t reveal the true ‘DNA’ of the files.
Our goal at Intezer is to provide a clear detection (“Is the file good or bad?”), classify the malware (“Which kind of malware is it? What malware family is it?”) and accelerate the investigation time.
In order to achieve these goals, we developed unpacking capabilities as part of our analysis system, using both dynamic and static unpacking techniques. In this post, we’ll discuss what packers are, and how our technology assists security researchers in their daily work.
Staying Under the Radar
Malware authors use a lot of techniques to avoid detection. One of the most popular techniques is to use packers–tools that compress, encrypt, and/or modify a malicious file’s format. It can be an industrial packer like UPX, Themida, etc., or a custom packer for specific campaign, which we have seen before. Packers can also be used for protecting legitimate software, so it’s important not to automatically classify a given packer as a malicious program. It’s clear, though, that unpacking adds another challenge for the security researchers and increases the amount of required investigation time.
In this screenshot, before implementing the Unpacking feature, you can see that we’ve identified a custom packer, but could not classify the specific malware behind it (you can see in its DNA mapping that there are only 15 genes).
Dynamic Unpacking – How Does It Work?
In order to dynamically execute files and analyze the memory payload, we integrated our technology with a sandbox solution. After a short time (~2 minutes) when the file is running in the sandbox, we can access the memory modules and build the PE files from the memory dumps. Once we have the PE files, we can analyze them normally using our Code Intelligence™ technology to provide much deeper analysis on the uploaded file and inspect every piece of code in these running modules.
After analysis of the original file and the memory modules is complete, we can make a final determination about the nature of a file. It’s enough to identify a single file/memory module as malware in order to determine that the whole file is malicious.
You can see some very cool results here: https://analyze.intezer.com/#/analyses/d75a14ef-2e17-41e6-b020-a200f0da7520
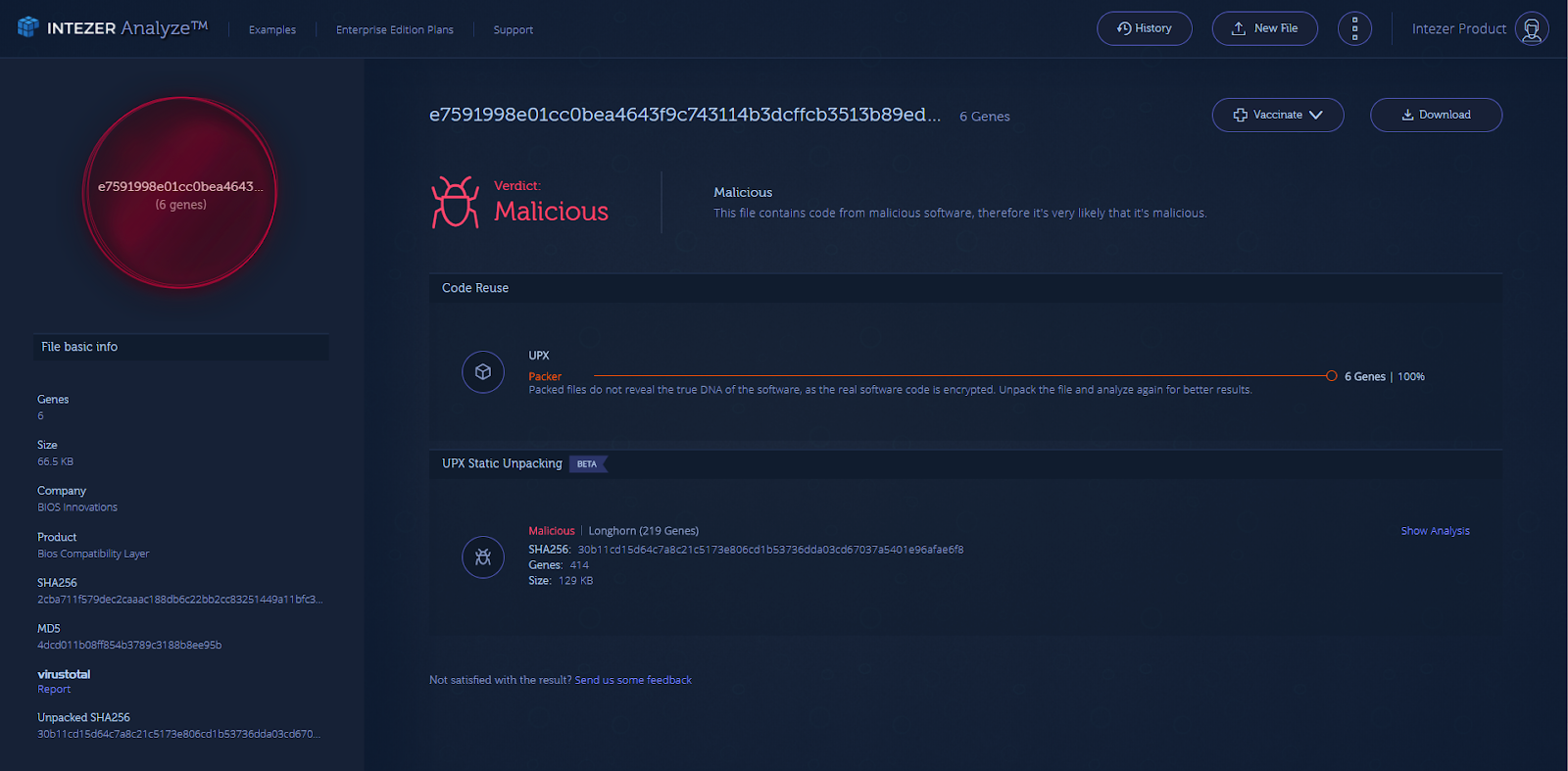
In this screenshot, we display the same example above, only now using our new unpacking capabilities.
After unpacking the original file and analyzing the memory dumps, we revealed 1014 genes– 971 of them connected with the Ramnit malware! While we display the bottom line from the memory module, it’s always possible to access the full analysis.
Our team would like to emphasize here the uniqueness of this kind of integration between dynamic unpacking to our Code Reuse technique: we combine the ability of a sandbox to run malware in an isolated environment with our method of analyzing every piece of code actually running in memory.
In a similar way to dynamic unpacking, we are able to identify packers that can be unpacked statically like UPX and obtain some noteworthy results as well:
https://analyze.intezer.com/#/analyses/58018a59-b80e-403a-a2f1-ce2cb1dedd9d
As you can see, we have redesigned our web interface in order to support even richer analysis.Your feedback is incredibly important to us, so we encourage you to try out this new feature and send us your thoughts at: support@intezer.com