Product Tour
Take a spin through Intezer’s AI SOC to see how to automatically triage, investigate and respond to every alert at unmatched speed and accuracy.
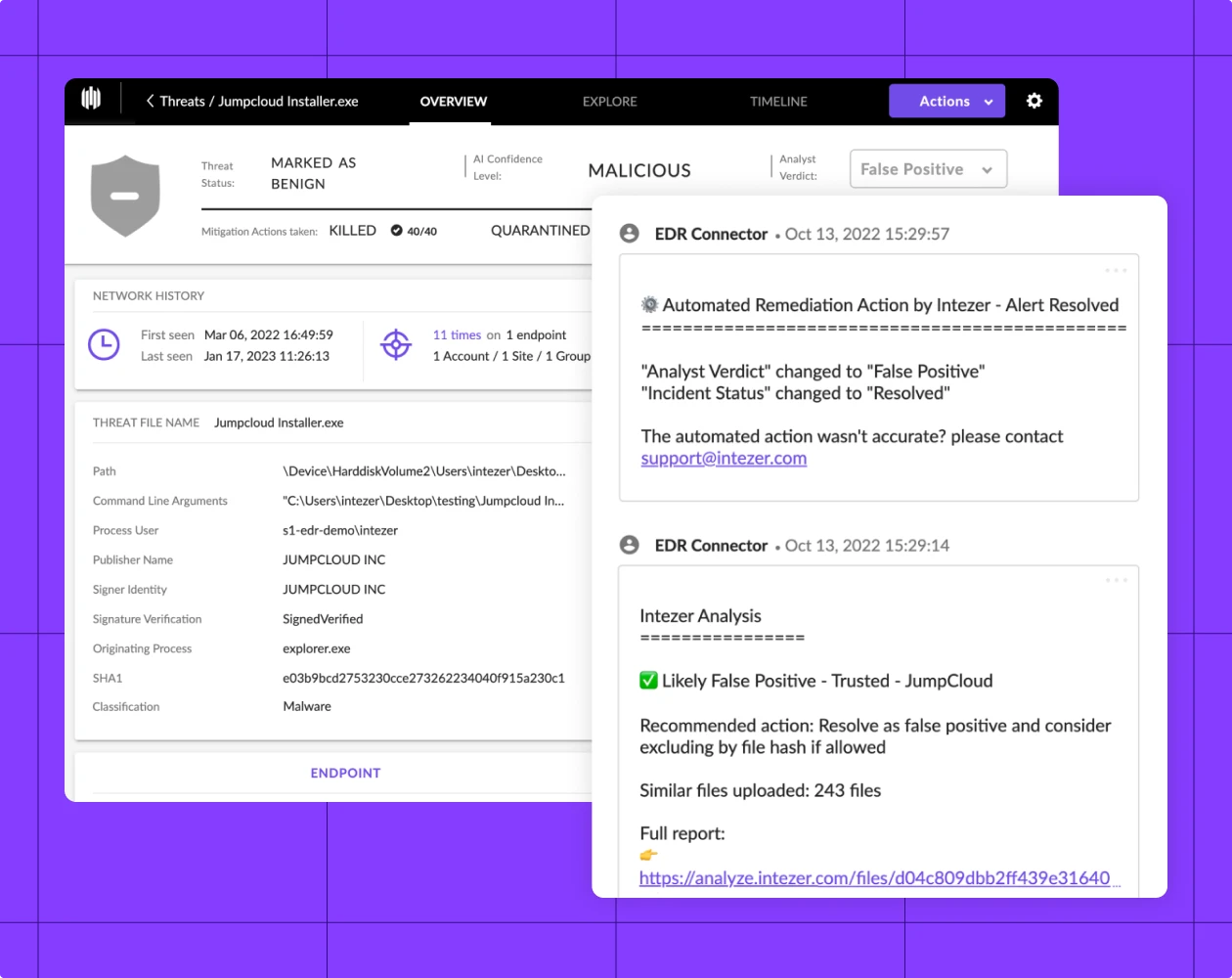
Let Intezer for SentinelOne monitor alerts 24/7 and resolve incidents for you



In just minutes, Intezer can start managing SentinelOne alerts for you – no engineering required to set up. After each new alert, get assessments and recommended actions pushed from Intezer right to your SentinelOne console.
Less Noise of false positive alerts resolved for you, tuning recommendations, and true threats clustered for efficient response
No Overlooked Incidents of alerts deeply investigated automatically, with actionable recommendations for every alert
Quick Time to Value the cost of traditional outsource SOC providers, with easy setup to save your team from time-consuming tasks
Intezer investigates evidence related to each alert to determine a clear classification, assessment, and recommended next steps.
Intezer auto-resolves false positives, escalating only the important incidents to your team with a complete analysis report.
Intezer auto-remediates confirmed threats and provides ready-to-use rules for response and hunting purposes.
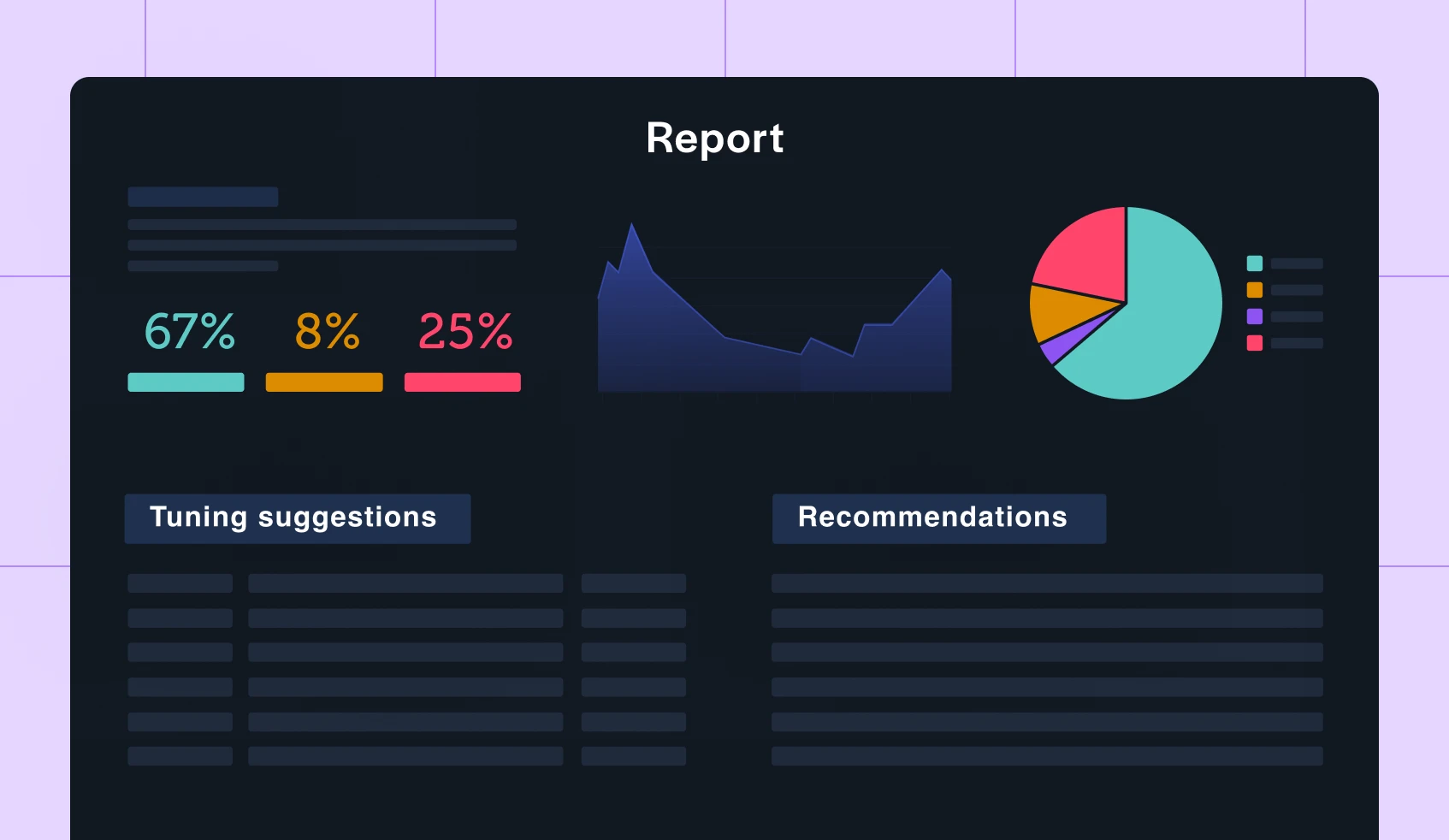
Intezer generates weekly reports to provide tuning suggestions and give you full visibility over your security operations and alert pipelines.
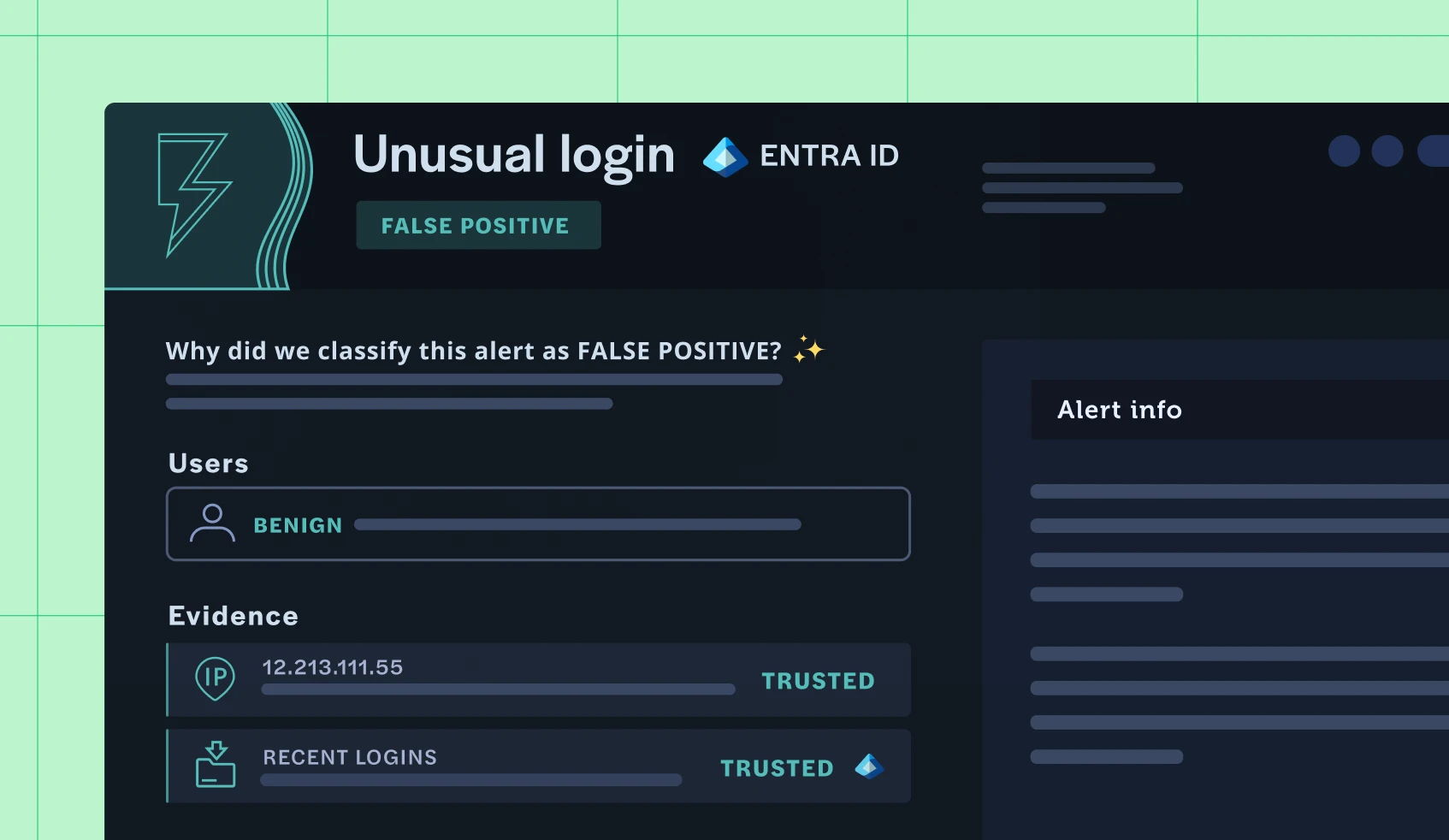

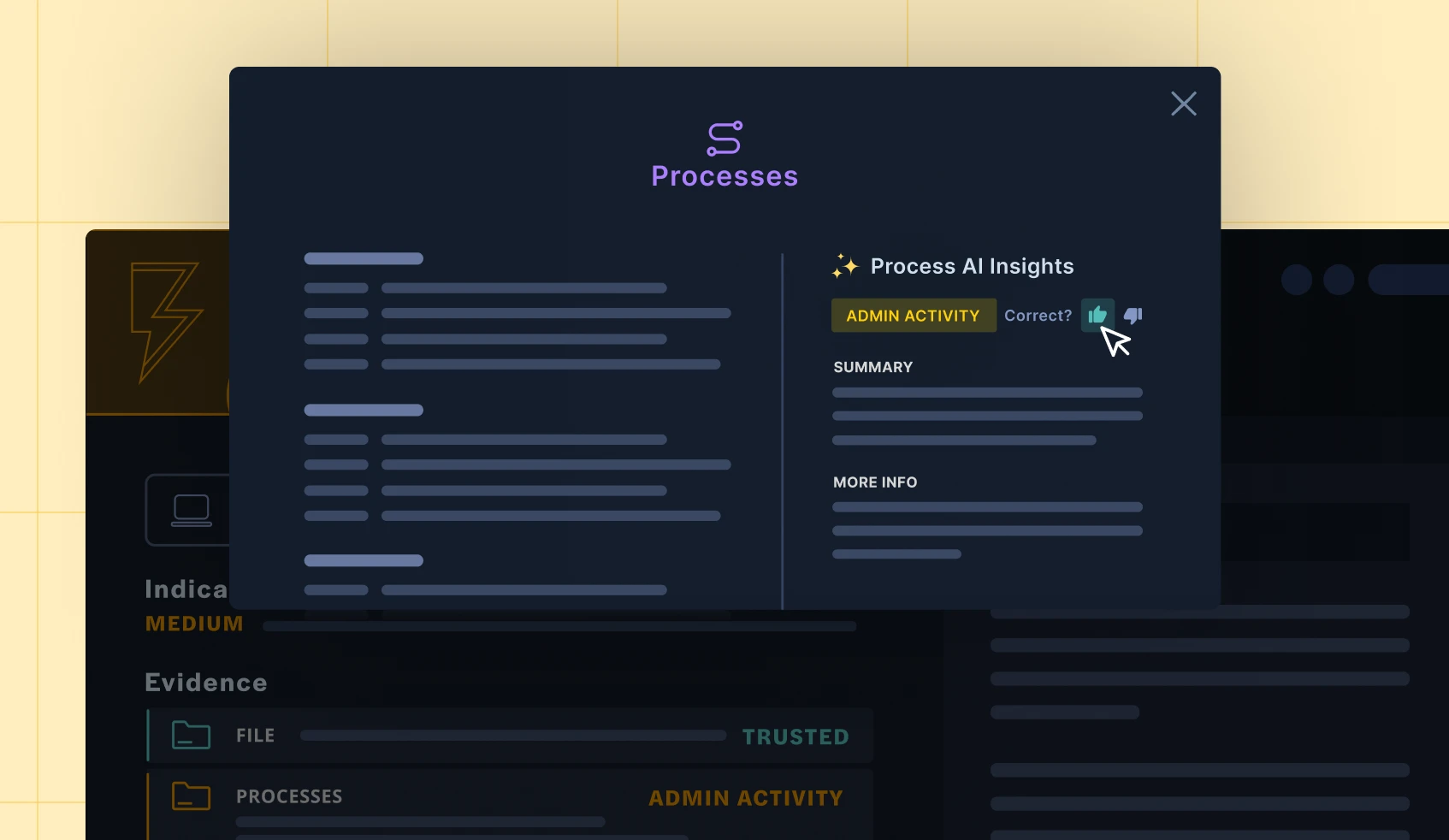

Intezer leverages a variety of techniques to analyze evidence, however, the unique core technology is Genetic Code Analysis. This proprietary technology identifies the origins of any unknown software or piece of code, which is a critical capability for investigating security alerts. For crafting the bottom-line alert triage assessments, Intezer uses machine learning and AI models that take into account the multiple analysis results for each individual evidence, as well as information from the user’s existing security tools. Intezer’s automated alert triage process starts by collecting all evidence associated with an alert (file, process, command line, IP, URL, memory image, etc.), deeply analyzes each artifact, and then builds an overall assessment for the incident with smart recommendations.
Unlike a SOAR that you’d use for case management and creating playbooks for repetitive operational tasks, Intezer focuses on automating the decision making and investigation process of security alerts that is usually handled by human analysts. Read more
Unlike a Sandbox that detonates individual files manually, Intezer allows you to directly connect your security tools to investigate alerts automatically, investigating multiple types of evidence (even fileless threats). Read more
Unlike outsourced SOC services which are primarily human-operated, Intezer is a SaaS platform that leverages advanced technology for alert monitoring and triage processes. This reduces the potential for human error and ensures a high level of accuracy and efficiency. Read more
The primary onboarding tasks are connecting your alert sources (adding an API key with the required permissions) and then adding members of your team as new users to Intezer.
After your API key gets added to Intezer, you should start seeing alert triage results in your dashboard within the hour. If you want to know more about getting started with Intezer, you can book a demo to talk with us about integrating Intezer into your tech stack and processes.
Top brands like Pepsico, Adobe, Equifax, Anheuser-Busch InBev, and other Fortune 500 enterprise security teams use Intezer to triage the high volume of alerts (and all the associated artifacts) from their endpoint and email security systems. Enterprise organizations also use Intezer’s Autonomous SOC capabilities across their SecOps teams, incident response, and cyber threat intelligence teams (as well as top security research teams, which frequently use Intezer’s best-in-class Malware Analysis toolset to analyze evolving and novel threats).
You can watch a 5 minute recorded demo here.
Trying out Intezer is easy! You have two options to access our solution for a trial period: